njsscan is a SAST tool that can find insecure code patterns in your Node.js applications.
Project description
njsscan
njsscan is a static application testing (SAST) tool that can find insecure code patterns in your node.js applications using simple pattern matcher from libsast and syntax-aware semantic code pattern search tool semgrep.
e-Learning Courses & Certifications

Installation
pip install njsscan
Requires Python 3.6+ and supports only Mac and Linux
Command Line Options
$ njsscan
usage: njsscan [-h] [--json] [--sonarqube] [-o OUTPUT] [--missing-controls]
[-w] [-v]
[path [path ...]]
positional arguments:
path Path can be file(s) or directories with source code
optional arguments:
-h, --help show this help message and exit
--json set output format as JSON
--sonarqube set output format compatible with SonarQube
-o OUTPUT, --output OUTPUT
output filename to save the result
--missing-controls enable missing security controls check
-w, --exit-warning non zero exit code on warning
-v, --version show njsscan version
Example Usage
$ njsscan xss_node.js
- Pattern Match ████████████████████████████████████████████████████████████ 1
- Semantic Grep ████████████████████████████████████████████████████████████ 53
======================================================================================================
RULE ID: express_xss
OWASP: A1: Injection
CWE: CWE-79: Improper Neutralization of Input During Web Page Generation ('Cross-site Scripting')
DESCRIPTION: Untrusted User Input in Response will result in Reflected Cross Site Scripting Vulnerability.
SEVERITY: ERROR
======================================================================================================
__________________FILES___________________________
File: xss_node.js
Match Position: 5 - 37
Line Number(s): 5: 6
Match String: var html = "Hello" + req.query.name + ". How are you?"
res.write('Response</br>' + html);
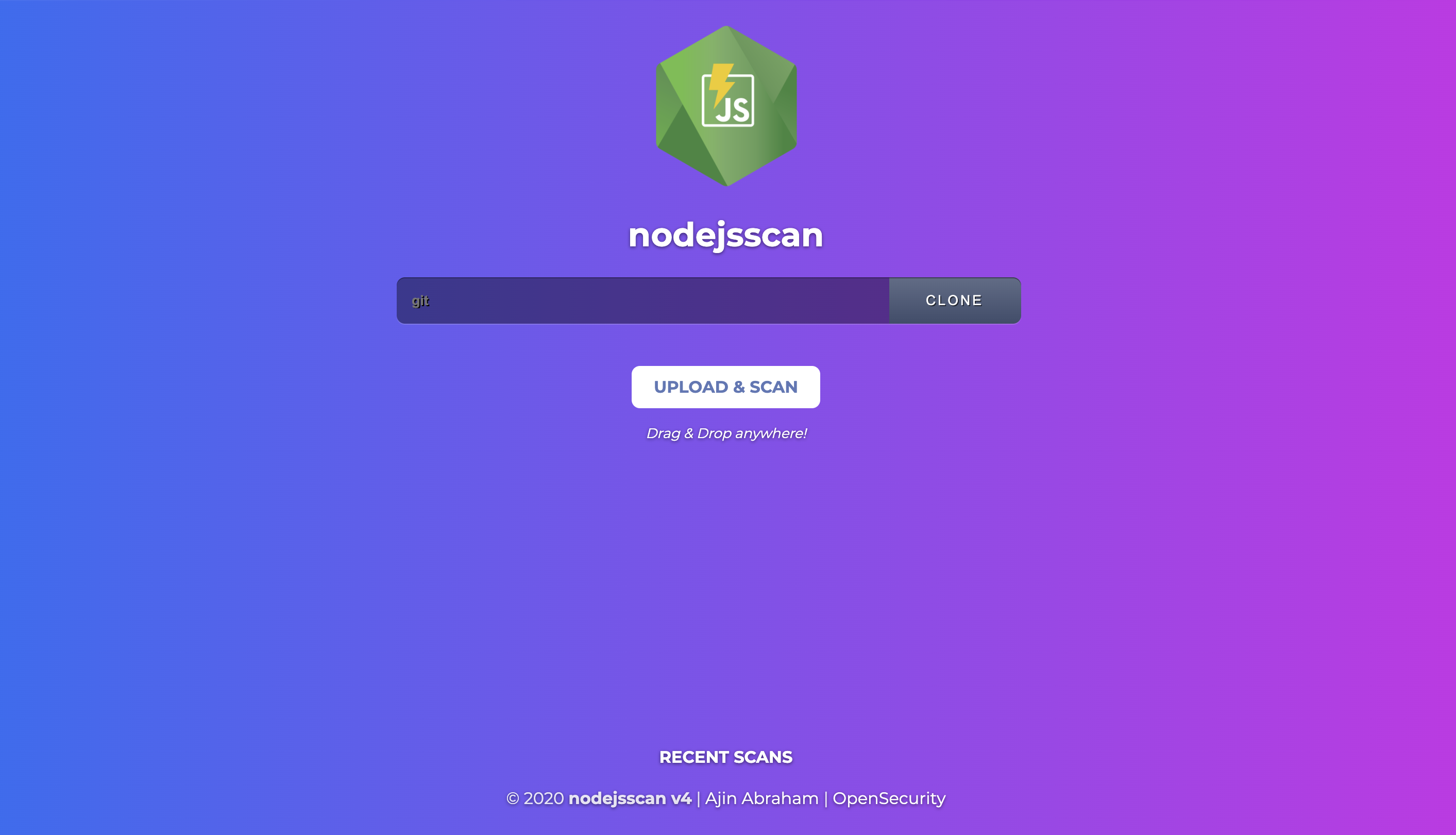
nodejsscan SAST
nodejsscan, built on top of njsscan provides a full fledged vulnerability management user interface along with other nifty integrations.
See nodejsscan
Python API
>>> from njsscan.njsscan import NJSScan
>>> node_source = '/node_source/true_positives/sqli_node.js'
>>> scanner = NJSScan([node_source], json=True, check_controls=False)
>>> scanner.scan()
{
'templates': {},
'nodejs': {
'node_sqli_injection': {
'files': [{
'file_path': '/node_source/true_positives/sqli_node.js',
'match_position': (1, 24),
'match_lines': (4, 11),
'match_string': 'var employeeId = req.foo;\n\nvar sql = "SELECT * FROM trn_employee WHERE employee_id = " + employeeId;\n\n\n\nconnection.query(sql, function (error, results, fields) {\n\n if (error) {\n\n throw error;\n\n }\n\n console.log(results);'
}],
'metadata': {
'owasp': 'A1: Injection',
'cwe': "CWE-89: Improper Neutralization of Special Elements used in an SQL Command ('SQL Injection')",
'description': 'Untrusted input concatinated with raw SQL query can result in SQL Injection.',
'severity': 'ERROR'
}
}
},
'errors': []
}
Configure njsscan
A .njsscan file in the root of the source code directory allows you to configure njsscan.
---
- nodejs-extensions:
- .js
template-extensions:
- .new
- .hbs
- ''
ignore-filenames:
- skip.js
ignore-paths:
- __MACOSX
- skip_dir
- node_modules
ignore-extensions:
- .jsx
ignore-rules:
- regex_injection_dos
- pug_jade_template
Suppress Findings
You can suppress findings from javascript source files by adding the comment //ignore: rule_id1, rule_id2 to the line that trigger the findings.
Example:
app.get('/some/redirect', function (req, res) {
var target = req.param("target");
res.redirect(target); //ignore: express_open_redirect
});
CI/CD Integrations
You can enable njsscan in your CI/CD or DevSecOps pipelines.
Github Action
Add the following to the file .github/workflows/njsscan.yml.
name: njsscan
on:
push:
branches: [ master ]
pull_request:
branches: [ master ]
jobs:
njsscan:
runs-on: ubuntu-latest
name: njsscan check
steps:
- uses: actions/checkout@v1
- name: njsscan
id: njsscan
uses: ajinabraham/njsscan-action@v5
with:
args: '.'
Example: dvna with njsscan github action
Gitlab CI/CD
Add the following to the file .gitlab-ci.yml.
stages:
- test
njsscan:
image: python
before_script:
- pip3 install --upgrade njsscan
script:
- njsscan .
Example: dvna with njsscan gitlab
Travis CI
Add the following to the file .travis.yml.
language: python
install:
- pip3 install --upgrade njsscan
script:
- njsscan .
Docker
Prebuilt image from DockerHub
docker pull opensecurity/njsscan
docker run -v /path-to-source-dir:/src opensecurity/njsscan /src
Build Locally
docker build -t njsscan .
docker run -v /path-to-source-dir:/src njsscan /src
Project details
Release history Release notifications | RSS feed
Download files
Download the file for your platform. If you're not sure which to choose, learn more about installing packages.
Source Distribution
Built Distribution
Filter files by name, interpreter, ABI, and platform.
If you're not sure about the file name format, learn more about wheel file names.
Copy a direct link to the current filters
File details
Details for the file njsscan-0.1.5.tar.gz.
File metadata
- Download URL: njsscan-0.1.5.tar.gz
- Upload date:
- Size: 33.6 kB
- Tags: Source
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/3.2.0 pkginfo/1.5.0.1 requests/2.24.0 setuptools/46.1.3 requests-toolbelt/0.9.1 tqdm/4.48.2 CPython/3.7.7
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
f19e42d83a8cafff0ac8bdb19fdb483b7749f3e4722e33dd21848ef06cfcb477
|
|
| MD5 |
b3309631c7f717b75dd34d3884cc70b0
|
|
| BLAKE2b-256 |
7e819d6c74329306f036bad785987346224409f771374e644fde1ab0bf34ecf9
|
File details
Details for the file njsscan-0.1.5-py3-none-any.whl.
File metadata
- Download URL: njsscan-0.1.5-py3-none-any.whl
- Upload date:
- Size: 68.3 kB
- Tags: Python 3
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/3.2.0 pkginfo/1.5.0.1 requests/2.24.0 setuptools/46.1.3 requests-toolbelt/0.9.1 tqdm/4.48.2 CPython/3.7.7
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
183d4605db9cced8487cbf296f6f0f176b8d2f19fbe208adf8663e9d019a5af1
|
|
| MD5 |
82a51c5094f46f865d9c7e7479f60a5c
|
|
| BLAKE2b-256 |
7e0289a9ee209340d9e86ca66a08efd2270b053ef4d7e4d5c937a7c62915bd2b
|


 in India
in India