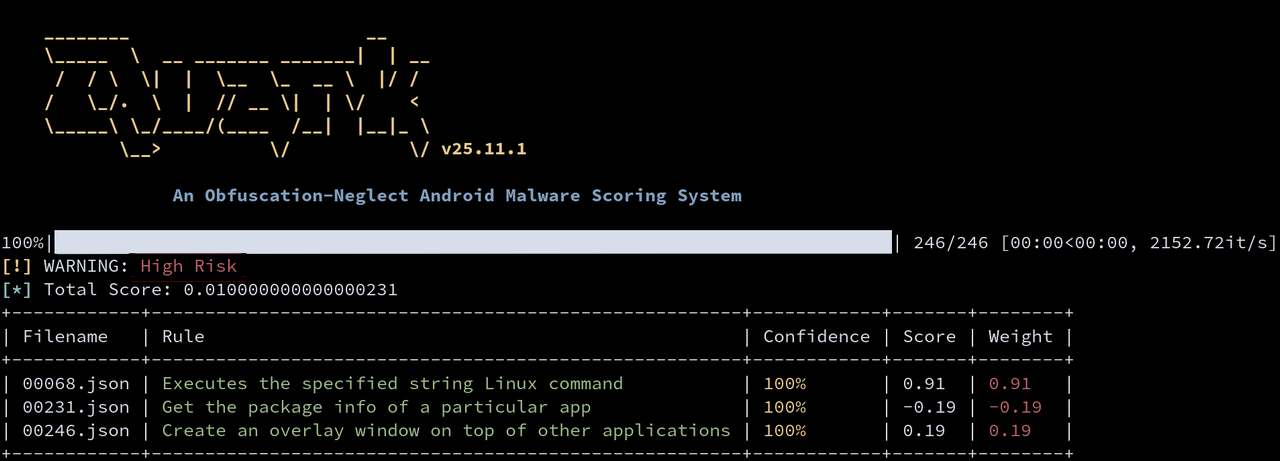
An Obfuscation-Neglect Android Malware Scoring System
Project description
Malware Family Analysis Report Showcase
 |
 |
 |
 |
 |
 |
 |
 |
 |
 |
 |
 |
| Family | Summary | Signature Behaviors | Report |
|---|---|---|---|
| DroidKungFu | Privilege escalation with C2 control. | 1. Gain unlimited access to a device. 2. Install/Uninstall additional apps. 3. Forward confidential data. |
View |
| GoldDream | SMS/call log exfiltration with remote C2 commands. | 1. Monitor SMS messages and phone calls. 2. Upload SMS messages and phone calls to remote servers. |
View |
| SpyNote | Credential theft and device surveillance via RAT. | 1. Take screenshots. 2. Simulate user gestures. 3. Log user input. 4. Communicate with C2 servers. |
View |
| DawDropper | Dropper that installs banking trojans for financial theft. | 1. Download APKs from remote servers. 2. Install additional APKs. |
View |
| SLocker | Android ransomware locking/encrypting devices. | 1. Lock the device with an overlay screen. | View |
| PhantomCard | NFC relay–based financial fraud. | 1. Communicate with C2 servers. 2. Read the payment data of NFC cards. 3. Captures PINs of NFC cards through deceptive screens. |
View |
| ToxicPanda | Banking trojan enabling on-device fraud. | 1. Abuse Accessibility. 2. Remote device control. 3. Intercept OTP. |
View |
| Hydra | Banking trojan using overlay attacks. | 1. Overlay credential theft. 2. Accessibility abuse. 3. Steal OTP/cookies. |
View |
| SharkBot | Banking trojan targeting financial credentials and transactions. | 1. Abuse Accessibility services. 2. Perform overlay attacks to steal credentials. 3. Intercept SMS messages (OTP). |
View |
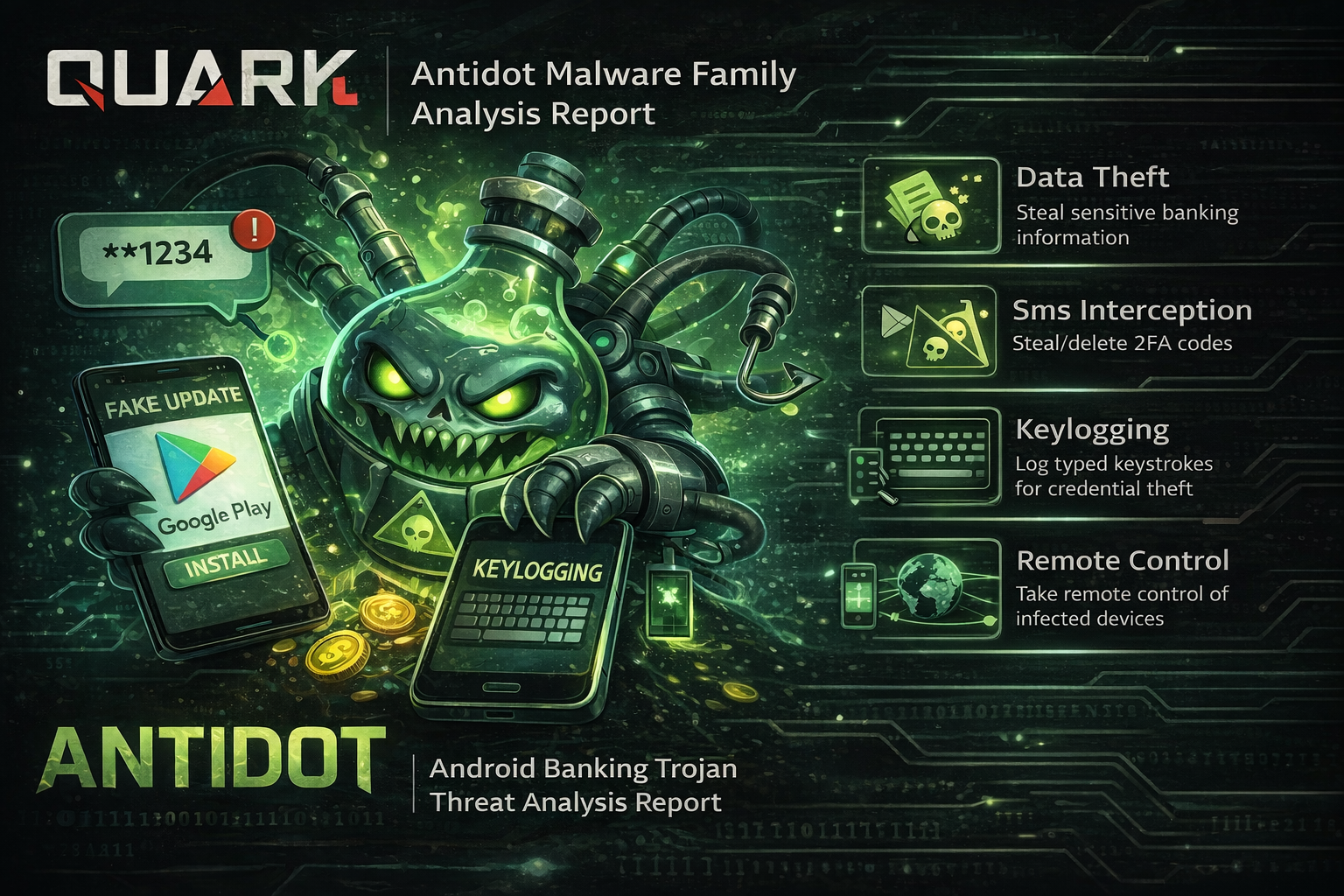
| Antidot | Banking trojan disguised as legitimate updates for financial data theft. | 1. Intercept SMS messages (OTP). 2. Log user input (keylogging). 3. Enable remote control via C2. |
View |
| Arsink | Banking trojan focusing on credential and financial data exfiltration. | 1. Steal sensitive data from device. 2. Intercept SMS messages (OTP). |
View |
| TrickMo | Banking trojan using overlay attacks and accessibility abuse for credential theft. | 1. Overlay attacks to steal banking credentials. 2. Intercept SMS for 2FA bypass. 3. Screen recording and accessibility abuse. 4. Dynamic payload loading via reflection. |
View |
Quick Start
Step 1. Install via PyPi
Install the latest version of Quark Engine:
$ pip3 install -U quark-engine
Step 2. Download Latest Rules
Fetch the latest rule database:
$ freshquark
Step 3. Run Summary Report
Analyze an APK with the downloaded rules and generate a summary report:
$ quark -a <apk_file> -s
Step 4. View Results
Example output:
Acknowledgments
The Honeynet Project
Google Summer Of Code
Quark-Engine has been participating in the GSoC under the Honeynet Project!
- 2021:
Stay tuned for the upcoming GSoC! Join the Honeynet Slack chat for more info.
Core Values of Quark Engine Team
- We love battle fields. We embrace uncertainties. We challenge impossibles. We rethink everything. We change the way people think. And the most important of all, we benefit ourselves by benefit others first.
Project details
Release history Release notifications | RSS feed
Download files
Download the file for your platform. If you're not sure which to choose, learn more about installing packages.
Source Distribution
Built Distribution
Filter files by name, interpreter, ABI, and platform.
If you're not sure about the file name format, learn more about wheel file names.
Copy a direct link to the current filters
File details
Details for the file quark_engine-26.5.1.tar.gz.
File metadata
- Download URL: quark_engine-26.5.1.tar.gz
- Upload date:
- Size: 105.4 kB
- Tags: Source
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/6.2.0 CPython/3.14.4
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
1dc5270a123983515f6e11f9b8747f230c1411ee8d9fae0ac62ab5958df7c4d3
|
|
| MD5 |
d82f12fb983c638d8fbf86fb1e7d97ee
|
|
| BLAKE2b-256 |
4bba4fafb3597700a55c5ec987bf9e01c7f5fc177fd4bb8ec35724a0272e65a8
|
File details
Details for the file quark_engine-26.5.1-py3-none-any.whl.
File metadata
- Download URL: quark_engine-26.5.1-py3-none-any.whl
- Upload date:
- Size: 127.8 kB
- Tags: Python 3
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/6.2.0 CPython/3.14.4
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
dfb63db04c5a1a34d147cb177cf3ac8268390766162477935d053193c510da9d
|
|
| MD5 |
cd8c120bcb601ba397c63fe6809ce06c
|
|
| BLAKE2b-256 |
86fe72f091d6a7663b09a1238121fb72405cd34f6d33d6f0bcea3f42eaa0a60f
|