A professional tool to automate attack surface detection in Android applications by parsing Manifest files.
Project description
📲 AndroidManifestExplorer
A high-performance static analysis utility designed to automate the discovery of attack surfaces in Android applications. By parsing decompiled AndroidManifest.xml files, this tool identifies exposed components, security misconfigurations, and deep-link vectors, providing ready-to-use adb payloads for immediate dynamic verification.
🎯 Security Objectives
- Attack Surface Mapping: Identify all exported Activities, Services, Broadcast Receivers, and Content Providers.
- Implicit Export Detection: Flag components that are exported by default due to the presence of intent-filters without explicit
android:exported="false"attributes. - Deep Link Analysis: Extract URI schemes and hosts to facilitate intent-fuzzing and unauthorized navigation testing.
- Permission Audit: Highlight unprotected components and evaluate the strength of defined custom permissions.
- Config Analysis: Detect high-risk flags such as
debuggable="true",allowBackup="true", andtestOnly="true".
🚀 Installation
Prerequisites
- Python 3.6+
- apktool (for decompiling binary XML)
Setup
- Clone the repository and install the dependencies:
$: git clone https://github.com/mateofumis/AndroidManifestExplorer.git
$: cd AndroidManifestExplorer
$: pip install .
- Alternatively, install the requirements directly:
$: pip install -r requirements.txt
- Using PyPI (Available for
piporpipx)
# with pip/pip3
$: pip install AndroidManifestExplorer
# or pipx
$: pipx install AndroidManifestExplorer
🛠 Usage Workflow
1. Decompile Target APK
The tool operates on the plain-text XML output of apktool.
$: apktool d target_app.apk -o output_dir
2. Execute Scan
Run the explorer against the generated manifest:
$: AndroidManifestExplorer -f output_dir/AndroidManifest.xml
If running the script directly without installation:
$: python3 AndroidManifestExplorer.py -f output_dir/AndroidManifest.xml
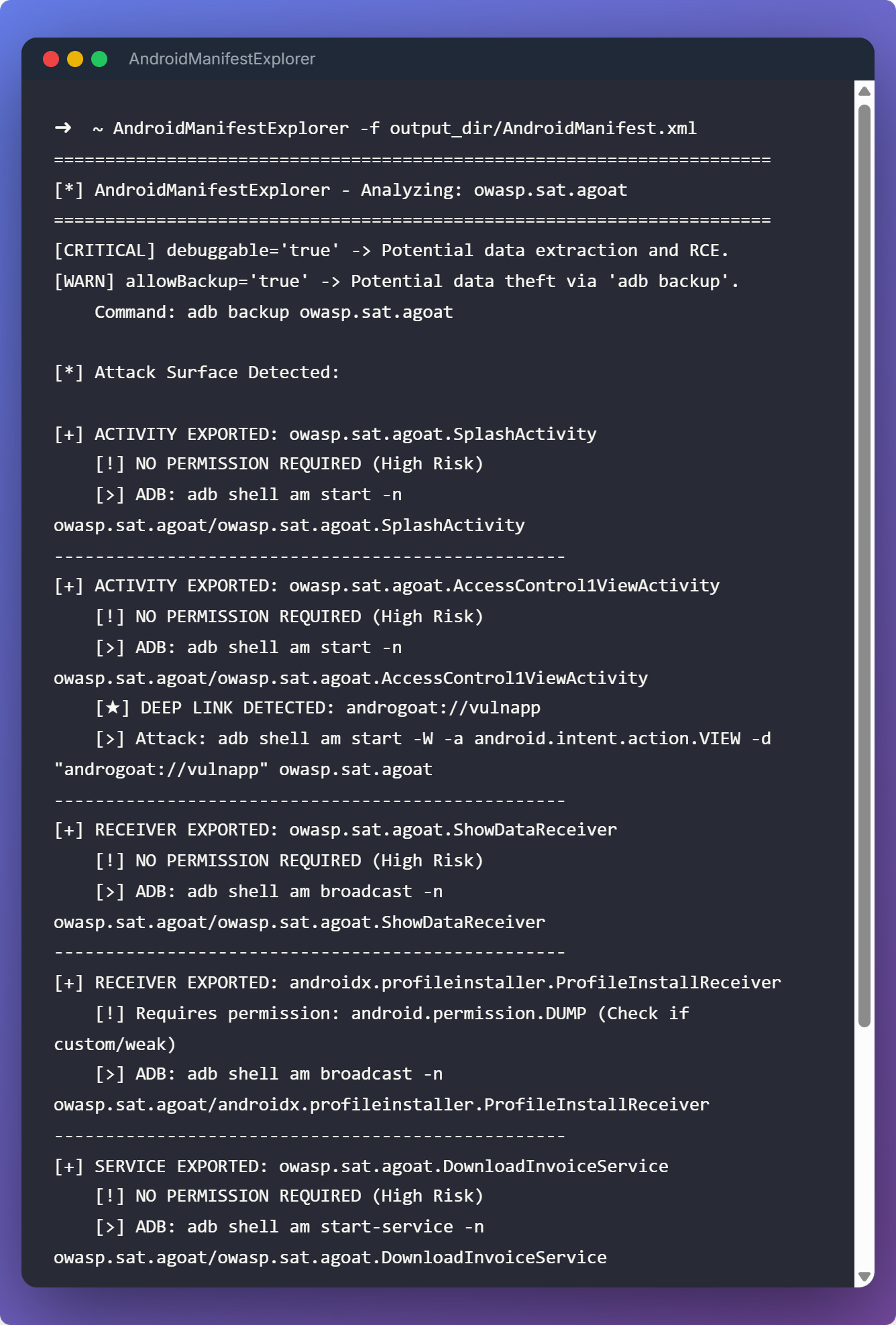
📊 Technical Output Overview
The tool categorizes findings by risk and generates specific adb commands:
- Activities: Generates
am startcommands. - Services: Generates
am start-servicecommands. - Receivers: Generates
am broadcastcommands. - Providers: Generates
content querycommands with a default SQLi test payload (--where "1=1").
Example Result:
[+] ACTIVITY EXPORTED: com.package.name.InternalActivity
[!] NO PERMISSION REQUIRED (High Risk)
[>] ADB: adb shell am start -n com.package.name/com.package.name.InternalActivity
[★] DEEP LINK DETECTED: secret-app://debug_panel
[>] Attack: adb shell am start -W -a android.intent.action.VIEW -d "secret-app://debug_panel" com.package.name
Preview
⚖️ Disclaimer
This tool is intended for professional security research and authorized penetration testing only. Unauthorized use against systems without prior written consent is strictly prohibited and may violate local and international laws. The developer assumes no liability for misuse or damage caused by this utility.
Project details
Release history Release notifications | RSS feed
Download files
Download the file for your platform. If you're not sure which to choose, learn more about installing packages.
Source Distribution
Built Distribution
Filter files by name, interpreter, ABI, and platform.
If you're not sure about the file name format, learn more about wheel file names.
Copy a direct link to the current filters
File details
Details for the file androidmanifestexplorer-1.1.0.tar.gz.
File metadata
- Download URL: androidmanifestexplorer-1.1.0.tar.gz
- Upload date:
- Size: 10.7 kB
- Tags: Source
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/6.2.0 CPython/3.13.9
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
a8cf2b25cd1b8c64fe4e1385528a93890c0a46a719250e7c9856e5ba6beb8ccd
|
|
| MD5 |
a7e517fbc860d3beeb56a130a70f53c5
|
|
| BLAKE2b-256 |
b61f619acb8eb697cb3ce1089f1230c55d329fa49f633386933c670c4c8fd888
|
File details
Details for the file androidmanifestexplorer-1.1.0-py3-none-any.whl.
File metadata
- Download URL: androidmanifestexplorer-1.1.0-py3-none-any.whl
- Upload date:
- Size: 9.9 kB
- Tags: Python 3
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/6.2.0 CPython/3.13.9
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
6abf5e016538ed4c365844d66bec77b757b05ed6d35c32340c91364b7fa4d1f7
|
|
| MD5 |
9e701c52560a1e9d9f99ff527991c387
|
|
| BLAKE2b-256 |
fce3425155b9c4eed99450625d4cb0f093fd15038eabc57b0413db9bc643f008
|