Extract credentials and other useful info from network captures
Project description
CredSLayer
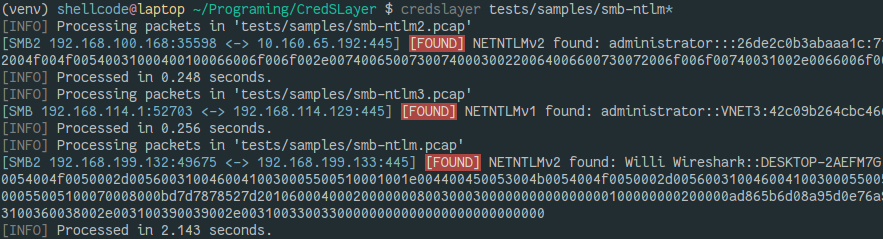
CredSLayer goal is to look for credentials and other useful stuff in network captures. Two modes are available, pcap scanning and active processing. The latest listens for packets on a chosen interface and dynamically extracts everything it can.
This tool has been heavily inspired by Pcredz and net-creds but is built with extensibility in mind. Pcredz and net-creds are great, but they are really hard to maintain and improve. Unlike these tools which are using regex and raw bytes parsing, CredSLayer takes advantage of Wireshark dissectors which have proven over time to be pretty accurate and reliable. It makes it really easy to add support for new protocols.
This tool can be really helpful if you're doing IT security or if you want to scan your own network to see if anything critical is transmitted.
Features
CredSLayer doesn't waste your time with invalid credentials, it makes sure credentials are valid. Yet if it's not able to tell whether they're valid or not, what has been found will be printed out anyway.
Right now, CredSLayer supports the following protocols:
- FTP
- SMTP / IMAP / POP3
- Telnet
- HTTP
- LDAP
- SNMP
- MySQL / PostgreSQL
- NTLMSSP
- Kerberos coming soon...
It is also able to look for email addresses and credit card numbers.
Note: To prevent false positives and performance issues, tshark (the Wireshark underlying engine) identifies protocols based on port numbers to know which dissector to use on which packets. A few protocols however have heuristic analysis to guess the protocol on different ports than the usual ones (such as HTTP). See the limitation chapter in the documentation. To address this issue, CredSLayer has a --map parameter, it enables you to map a (range of) port(s) to a specific protocol. This way you will be able to sniff credentials going to a specific service on a specific port you are aware of.
Install
You need tshark installed and Python >= 3.5. On some distribution tshark in shipped within the wireshark package.
Then simply install using :
$ pip install credslayer
I recommend you use a virtualenv to prevent conflicts.
Usage
$ credslayer -h
usage: credslayer [-h] [-l INTERFACE] [-s {enable,disable}] [-f IP]
[-m PORT:PROTOCOL] [--debug]
[pcapfiles [pcapfiles ...]]
Helps you find credentials and other interesting stuff in network captures
positional arguments:
pcapfiles pcap files you want to analyse.
optional arguments:
-h, --help show this help message and exit
-l INTERFACE, --listen INTERFACE
start active processing on specified interface
-s {enable,disable}, --string-inspection {enable,disable}
let you specify if you want to look for interesting
strings (email addresses, credit cards, ...) in
network captures. Pretty heavy on the CPU. Enabled by
default on pcap files, disabled on live captures.
-f IP, --filter IP only show packets involving the specified IP.
-m PORT:PROTOCOL, --map PORT:PROTOCOL
map a port to a protocol
--debug put CredSLayer and pyshark in debug mode.
Get involved
Thanks to Wireshark dissectors, it's really easy to write new protocols support, you're welcome to contribute !
Contributing doesn't necessarily mean writing code. You can simply contribute by opening new issues on Github if you spot any bug or if you would like to see something added to the tool.
To learn how to create support for a new protocol, head over to the documentation.
Credits
Project details
Download files
Download the file for your platform. If you're not sure which to choose, learn more about installing packages.
Source Distribution
Built Distribution
Filter files by name, interpreter, ABI, and platform.
If you're not sure about the file name format, learn more about wheel file names.
Copy a direct link to the current filters
File details
Details for the file CredSLayer-0.1.3.tar.gz.
File metadata
- Download URL: CredSLayer-0.1.3.tar.gz
- Upload date:
- Size: 33.2 kB
- Tags: Source
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/4.0.1 CPython/3.10.5
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
6b3fcf35fc943288ebb003252b39507f83ad48d505d19331da0c062a24c3b515
|
|
| MD5 |
a9907693657d509b88e1d3a2ae9d1ea0
|
|
| BLAKE2b-256 |
df2f79f0439679766d6a0a03488df06313f0d625afc9734e35cecfcbc52457b2
|
File details
Details for the file CredSLayer-0.1.3-py3-none-any.whl.
File metadata
- Download URL: CredSLayer-0.1.3-py3-none-any.whl
- Upload date:
- Size: 38.6 kB
- Tags: Python 3
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/4.0.1 CPython/3.10.5
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
1e0533795fe04fb495bcbc26c5c90e5c016cc9a76effbee5d496033e0055a935
|
|
| MD5 |
404cd6fe8dc3196f2c4c9b964fdf2079
|
|
| BLAKE2b-256 |
1c398fe10b76d18a55510e074e4be25970c95f7bbfe6c90072ecbddf59fa8003
|