Python Active Directory Reconnaissance Tool (ADRecon port) using ADWS with NTLM support.
Project description

A Python3 implementation of PyADRecon using ADWS instead of LDAP for Pentesters, Red and Blue Teams
PyADRecon is a tool which gathers information about MS Active Directory and generates an XSLX report to provide a holistic picture of the current state of the target AD environment.
[!TIP] Queries Active Directory Web Services (ADWS) over TCP/9389 instead of LDAP to fly under the EDR radar.
Table of Contents
- Installation
- Usage
- Docker
- Collection Modules
- HTML Dashboard
- Known Limitations
- Acknowledgements
- License
Installation
# stable release from pypi
pipx install pyadrecon-adws
# latest commit from github
pipx install git+https://github.com/l4rm4nd/PyADRecon-ADWS
Then verify installation:
pyadrecon_adws --version
[!TIP] For Windows, may read this. Only NTLM authentication works on Windows atm.
Usage
usage: pyadrecon_adws.py [-h] [--version] [--generate-excel-from CSV_DIR] [-d DOMAIN] [-u USERNAME] [-p PASSWORD]
[-dc DOMAIN_CONTROLLER] [--port PORT] [--auth {ntlm,kerberos}] [--spn SPN]
[--workstation WORKSTATION] [-c COLLECT] [--only-enabled] [--page-size PAGE_SIZE]
[--dormant-days DORMANT_DAYS] [--password-age PASSWORD_AGE] [-o OUTPUT] [--no-excel]
[-v]
PyADRecon-ADWS # Active Directory Reconnaissance using ADWS
options:
-h, --help show this help message and exit
--version show program's version number and exit
--generate-excel-from CSV_DIR
Generate Excel report from existing CSV files (standalone mode)
-d, --domain DOMAIN Domain name (e.g., example.com)
-u, --username USERNAME
Username (DOMAIN\user or user@domain.com)
-p, --password PASSWORD
Password or LM:NTLM hash (will prompt if not provided)
-dc, --domain-controller DOMAIN_CONTROLLER
Domain controller hostname or IP
--port PORT ADWS port (default: 9389)
--auth {ntlm,kerberos}
Authentication method: ntlm or kerberos (default: ntlm)
--spn SPN Service Principal Name override (default: HTTP/dc.fqdn)
--workstation WORKSTATION
NTLM authentication workstation name (default: random)
-c, --collect COLLECT
Comma-separated modules to collect (default: all)
--only-enabled Only collect enabled users/computers
--page-size PAGE_SIZE
ADWS query page size (default: 256)
--dormant-days DORMANT_DAYS
Users/Computers with lastLogon older than X days are dormant (default: 90)
--password-age PASSWORD_AGE
Users with pwdLastSet older than X days have old passwords (default: 180)
-o, --output OUTPUT Output directory (default: PyADRecon-Report-<timestamp>)
--no-excel Skip Excel export
--no-dashboard Skip interactive HTML dashboard generation
-v, --verbose Enable verbose output
Examples:
# Basic usage with NTLM authentication
pyadrecon_adws.py -dc 192.168.1.1 -u admin -p password123 -d DOMAIN.LOCAL
# With Kerberos authentication (only works on Linux with gssapi atm)
pyadrecon.py -dc dc01.domain.local -u admin -p password123 -d DOMAIN.LOCAL --auth kerberos
# Only collect specific modules
pyadrecon_adws.py -dc 192.168.1.1 -u admin -p pass -d DOMAIN.LOCAL --collect users,groups,computers
# Output to specific directory
pyadrecon_adws.py -dc 192.168.1.1 -u admin -p pass -d DOMAIN.LOCAL -o /tmp/adrecon_output
# Generate Excel report from existing CSV files (standalone mode)
pyadrecon_adws.py --generate-excel-from /path/to/CSV-Files -o report.xlsx
Docker
There is also a Docker image available on GHCR.IO.
docker run --rm -v /etc/krb5.conf:/etc/krb5.conf:ro -v /etc/hosts:/etc/hosts:ro -v ./:/tmp/pyadrecon_output ghcr.io/l4rm4nd/pyadrecon-adws:latest -dc dc01.domain.local -u admin -p password123 -d DOMAIN.LOCAL -o /tmp/pyadrecon_output
Collection Modules
As default, PyADRecon-ADWS runs all collection modules. They are referenced to as default or all.
Though, you can freely select your own collection of modules to run:
| Icon | Meaning |
|---|---|
| 🛑 | Requires administrative domain privileges (e.g. Domain Admins) |
| ✅ | Requires regular domain privileges (e.g. Authenticated Users) |
| 💥 | New collection modul in beta state. Results may be incorrect. |
Forest & Domain
forest✅domain✅trusts✅sites✅subnets✅schemaorschemahistory✅
Domain Controllers
dcsordomaincontrollers✅
Users & Groups
users✅userspns✅groups✅groupmembers✅protectedgroups✅💥krbtgt✅asreproastable✅kerberoastable✅
Computers & Printers
computers✅computerspns✅printers✅
OUs & Group Policy
ous✅gpos✅gplinks✅
Passwords & Credentials
passwordpolicy✅fgpporfinegrainedpasswordpolicy🛑laps🛑bitlocker🛑💥
Managed Service Accounts
gmsaorgroupmanagedserviceaccounts✅💥dmsaordelegatedmanagedserviceaccounts✅💥- Only works for Windows Server 2025+ AD schema
Certificates
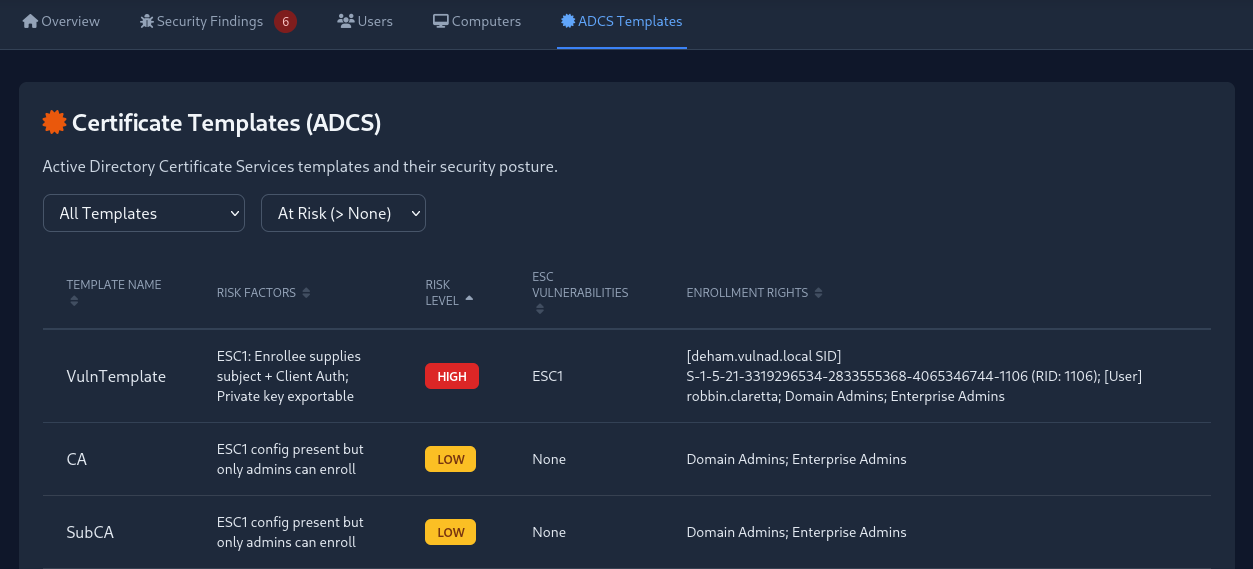
adcsorcertificates✅💥- Detects ESC1, ESC2, ESC3, ESC4 and ESC9
DNS
dnszones✅dnsrecords✅
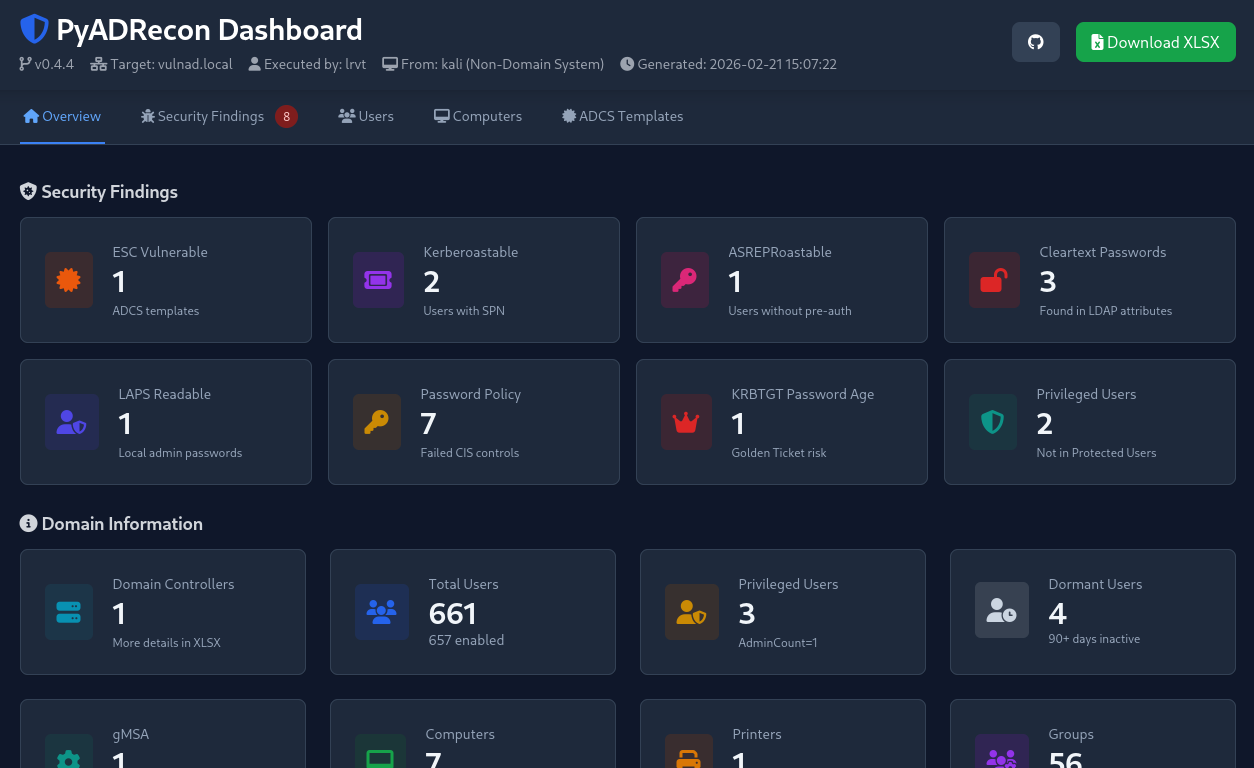
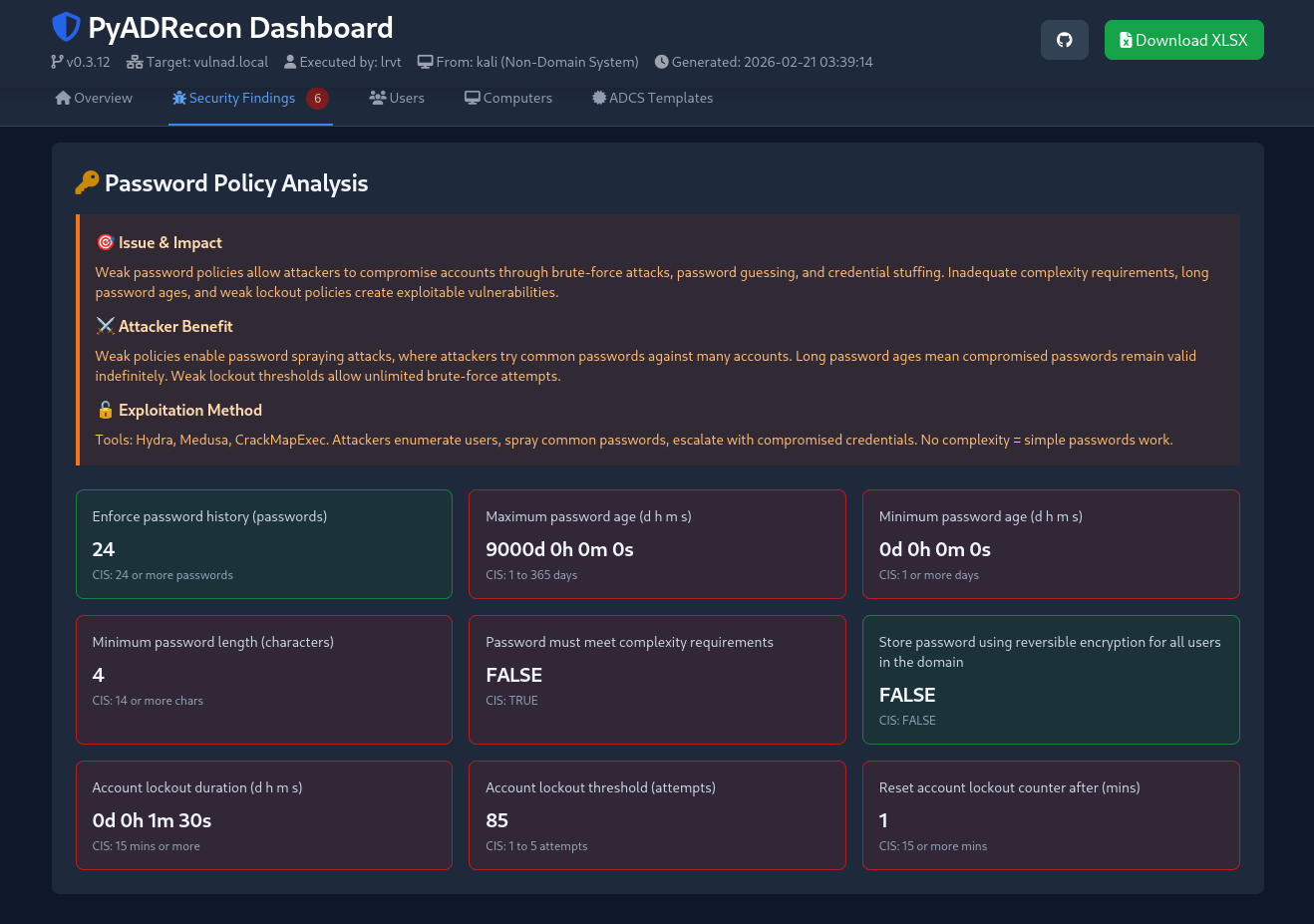
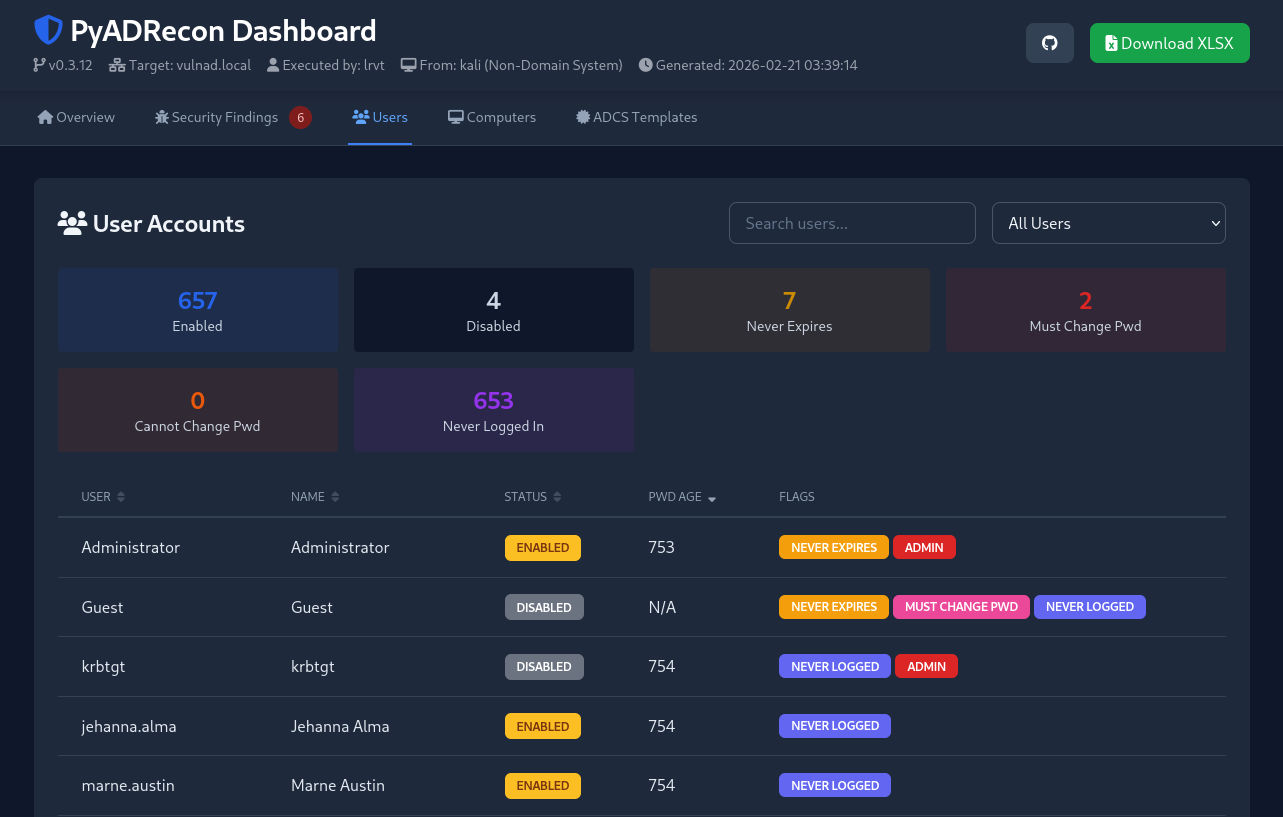
HTML Dashboard
PyADRecon-ADWS will automatically create an HTML dashboard with important stats and security findings.
You may disable HTML dashboard generation via --no-dashboard.
[!CAUTION] This is a beta feature. Displayed data may be falsely parsed or reported as issue. Take it with a grain of salt!
Known Limitations
Multi-Domain Forests – Security Descriptors
Show details
When querying child domains in a multi-domain forest, ADWS returns incomplete security descriptors for forest-wide objects like certificate templates.
Issue:
- Certificate template ACLs (enrollment rights, write permissions) may not show principals from the child domain itself
- Only parent domain principals will appear in enrollment rights
- This is an ADWS protocol limitation, not a PyADRecon-ADWS bug
Example:
- Querying from child domain (
child.domain.local): Shows parent domain principals only - Querying from parent domain (
domain.local): Shows all principals including child domain
Solution:
- For complete certificate template ACL data, connect to the forest root domain controller instead of a child DC
Multi-Domain Forests – LDAP Referrals
Show details
When querying a child domain in a multi-domain forest, LDAP may return referrals for objects that reside in a different naming context (for example, the forest root domain).
Issue:
- Queries for forest-root objects (e.g., Enterprise Admins, Schema Admins, or root-domain users/groups) may return LDAP referrals
- PyADRecon does not chase LDAP referrals
- Referred objects are therefore not collected automatically
Solution:
- To ensure complete forest-wide enumeration, run PyADRecon separately against:
- The child domain
- The forest root domain
- Combine results manually if full forest visibility is required
Acknowledgements
Many thanks to the following folks:
- S3cur3Th1sSh1t for a first Claude draft of PyADRecon using LDAP
- Sense-of-Security for the original ADRecon script in PowerShell
- dirkjanm for the original ldapdomaindump script
- mverschu for his port of ldapdomaindump using ADWS (adwsdomaindump). PyADRecon-ADWS heavily makes use of the ldap-to-adws wrapper.
- Forta for the awesome impacket suite
- Anthropic for Claude LLMs
License
PyADRecon-ADWS is released under the MIT License.
The following third-party libraries are used:
| Library | License |
|---|---|
| openpyxl | MIT |
| impacket | Apache 2.0 |
| adwsdomaindump ADWS Wrapper | MIT |
Please refer to the respective licenses of these libraries when using or redistributing this software.
Project details
Release history Release notifications | RSS feed
Download files
Download the file for your platform. If you're not sure which to choose, learn more about installing packages.
Source Distribution
Built Distribution
Filter files by name, interpreter, ABI, and platform.
If you're not sure about the file name format, learn more about wheel file names.
Copy a direct link to the current filters
File details
Details for the file pyadrecon_adws-0.4.7.tar.gz.
File metadata
- Download URL: pyadrecon_adws-0.4.7.tar.gz
- Upload date:
- Size: 1.8 MB
- Tags: Source
- Uploaded using Trusted Publishing? Yes
- Uploaded via: twine/6.1.0 CPython/3.13.7
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
f841f679cb57ae70eb252ff7ba164d3a2043a34a60bdcc7be297ef72522fa903
|
|
| MD5 |
a1562c50a813cbdd6316b52e7c7a1ee9
|
|
| BLAKE2b-256 |
12859b2ee10d3c7f7478bbf952f529b31c0f255199b6270598cf5e0f18bc003c
|
Provenance
The following attestation bundles were made for pyadrecon_adws-0.4.7.tar.gz:
Publisher:
pypi.yml on l4rm4nd/PyADRecon-ADWS
-
Statement:
-
Statement type:
https://in-toto.io/Statement/v1 -
Predicate type:
https://docs.pypi.org/attestations/publish/v1 -
Subject name:
pyadrecon_adws-0.4.7.tar.gz -
Subject digest:
f841f679cb57ae70eb252ff7ba164d3a2043a34a60bdcc7be297ef72522fa903 - Sigstore transparency entry: 975871281
- Sigstore integration time:
-
Permalink:
l4rm4nd/PyADRecon-ADWS@9c2fdfb43a17f5abc1fafa92c6e66d80f487529e -
Branch / Tag:
refs/tags/v0.4.7 - Owner: https://github.com/l4rm4nd
-
Access:
public
-
Token Issuer:
https://token.actions.githubusercontent.com -
Runner Environment:
github-hosted -
Publication workflow:
pypi.yml@9c2fdfb43a17f5abc1fafa92c6e66d80f487529e -
Trigger Event:
release
-
Statement type:
File details
Details for the file pyadrecon_adws-0.4.7-py3-none-any.whl.
File metadata
- Download URL: pyadrecon_adws-0.4.7-py3-none-any.whl
- Upload date:
- Size: 132.3 kB
- Tags: Python 3
- Uploaded using Trusted Publishing? Yes
- Uploaded via: twine/6.1.0 CPython/3.13.7
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
f6d7238c1068f6e7637a85b3531cc084f94b7530df1ce3fe8a7a1a97200540b7
|
|
| MD5 |
1186b108825759b23e011db3fe1c7bc5
|
|
| BLAKE2b-256 |
6e7f179547c9478fc833d856b53828aefa131bf8a263e2fe5c29e332253df404
|
Provenance
The following attestation bundles were made for pyadrecon_adws-0.4.7-py3-none-any.whl:
Publisher:
pypi.yml on l4rm4nd/PyADRecon-ADWS
-
Statement:
-
Statement type:
https://in-toto.io/Statement/v1 -
Predicate type:
https://docs.pypi.org/attestations/publish/v1 -
Subject name:
pyadrecon_adws-0.4.7-py3-none-any.whl -
Subject digest:
f6d7238c1068f6e7637a85b3531cc084f94b7530df1ce3fe8a7a1a97200540b7 - Sigstore transparency entry: 975871284
- Sigstore integration time:
-
Permalink:
l4rm4nd/PyADRecon-ADWS@9c2fdfb43a17f5abc1fafa92c6e66d80f487529e -
Branch / Tag:
refs/tags/v0.4.7 - Owner: https://github.com/l4rm4nd
-
Access:
public
-
Token Issuer:
https://token.actions.githubusercontent.com -
Runner Environment:
github-hosted -
Publication workflow:
pypi.yml@9c2fdfb43a17f5abc1fafa92c6e66d80f487529e -
Trigger Event:
release
-
Statement type:











