A request rate limiter for fastapi
Project description
FastAPI Limiter
FastAPI-Limiter is a rate limiting tool for fastapi routes, powered by pyrate-limiter.









🦜🕸️
NOTE: This is a fork of (https://github.com/long2ice/fastapi-limiter), currently because the original maintainer @long2ice has not published the latest version which supports FastAPI middleware.
Table of Contents
Introduction
FastAPI-Limiter is a rate limiting tool for fastapi routes, powered by pyrate-limiter.
Quick Start
Since this is just a package, and not a service, there is no real "run" action. But you can run the tests immediately.
Here are a list of available commands via make.
Bare Metal (i.e. your machine)
make install- install the required dependencies.make test- runs the tests.
Docker
make build-docker- build the docker image.make run-docker- run the docker compose services.make test-docker- run the tests in docker.make clean-docker- remove all docker containers etc.
Installation
For Dev work on the repo
Install uv, (if you haven't already)
https://docs.astral.sh/uv/getting-started/installation/#installation-methods
brew install uv
Initialise pre-commit (validates ruff on commit.)
uv run pre-commit install
Install dependencies (including dev dependencies)
uv sync
If you are adding a new dev dependency, please run:
uv add --dev {your-new-package}
Namespaces
Packages all share the same namespace ab_core. To import this package into
your project:
from ab_core.template import placeholder_func
We encourage you to make your package available to all of ab via this
ab_core namespace. The goal is to streamline development, POCs and overall
collaboration.
Usage
Adding the dependency to your project
The library is available on PyPI. You can install it using the following command:
Using pip:
pip install ab-fastapi-limiter
Using UV
Note: there is currently no nice way like poetry, hence we still needd to provide the full url. https://github.com/astral-sh/uv/issues/10140
Add the dependency
uv add ab-fastapi-limiter
Using poetry:
Then run the following command to install the package:
poetry add ab-fastapi-limiter
How tos
Quick Start
FastAPI-Limiter is simple to use, which just provides a dependency RateLimiter. The following example allows 2 requests per 5 seconds on route /.
import uvicorn
from fastapi import Depends, FastAPI
from pyrate_limiter import Duration, Limiter, Rate
from ab_core.fastapi_limiter.depends import RateLimiter
app = FastAPI()
@app.get(
"/",
dependencies=[Depends(RateLimiter(limiter=Limiter(Rate(2, Duration.SECOND * 5))))],
)
async def index():
return {"msg": "Hello World"}
if __name__ == "__main__":
uvicorn.run("main:app", reload=True)
Usage
RateLimiter
RateLimiter accepts the following parameters:
limiter: Apyrate_limiter.Limiterinstance that defines the rate limiting rules.identifier: A callable to identify the request source, default is by IP + path.callback: A callable invoked when the rate limit is exceeded, default raisesHTTPExceptionwith429status code.blocking: Whether to block the request when the rate limit is exceeded, default isFalse.skip: An async callable that takes a request and returnsTrueto skip rate limiting, default isNone.
Identifier
Identifier of route limit, default is ip + path, you can override it such as userid and so on.
async def default_identifier(request: Union[Request, WebSocket]):
forwarded = request.headers.get("X-Forwarded-For")
if forwarded:
ip = forwarded.split(",")[0]
elif request.client:
ip = request.client.host
else:
ip = "127.0.0.1"
return ip + ":" + request.scope["path"]
Callback
Callback when rate limit is exceeded, default raises HTTPException with 429 status code.
def default_callback(*args, **kwargs):
raise HTTPException(
HTTP_429_TOO_MANY_REQUESTS,
"Too Many Requests",
)
Multiple limiters
You can use multiple limiters in one route.
@app.get(
"/multiple",
dependencies=[
Depends(RateLimiter(limiter=Limiter(Rate(1, Duration.SECOND * 5)))),
Depends(RateLimiter(limiter=Limiter(Rate(2, Duration.SECOND * 15)))),
],
)
async def multiple():
return {"msg": "Hello World"}
Note that you should keep the stricter limiter (lower seconds/times ratio) first.
Skip rate limiting
You can pass a skip callable to RateLimiter to conditionally skip rate limiting for a specific route. The callable receives the request and should return True to skip.
from fastapi.requests import Request
async def skip(request: Request):
return request.scope["path"] == "/skip"
@app.get(
"/skip",
dependencies=[
Depends(RateLimiter(limiter=Limiter(Rate(1, Duration.SECOND * 5)), skip=skip))
],
)
async def skip_route():
return {"msg": "This route skips rate limiting"}
Middleware
You can also use RateLimiterMiddleware to apply rate limiting globally to all routes without adding dependencies to each route individually.
from fastapi import FastAPI
from pyrate_limiter import Duration, Limiter, Rate
from ab_core.fastapi_limiter.middleware import RateLimiterMiddleware
app = FastAPI()
app.add_middleware(
RateLimiterMiddleware,
limiter=Limiter(Rate(2, Duration.SECOND * 5)),
)
@app.get("/")
async def index():
return {"msg": "Hello World"}
RateLimiterMiddleware accepts the same identifier, callback, blocking, and skip parameters as RateLimiter.
Rate limiting within a websocket
While the above examples work with REST requests, FastAPI also allows easy usage of websockets, which require a slightly different approach.
Because websockets are likely to be long lived, you may want to rate limit in response to data sent over the socket.
You can do this by rate limiting within the body of the websocket handler:
from ab_core.fastapi_limiter.depends import WebSocketRateLimiter
@app.websocket("/ws")
async def websocket_endpoint(websocket: WebSocket):
await websocket.accept()
ratelimit = WebSocketRateLimiter(limiter=Limiter(Rate(1, Duration.SECOND * 5)))
while True:
try:
data = await websocket.receive_text()
await ratelimit(websocket, context_key=data) # NB: context_key is optional
await websocket.send_text("Hello, world")
except HTTPException:
await websocket.send_text("Hello again")
Formatting and linting
We use Ruff as the formatter and linter. The pre-commit has hooks which runs checking and applies linting automatically. The CI validates the linting, ensuring main is always looking clean.
You can manually use these commands too:
make lint- check for linting issues.make format- fix linting issues.
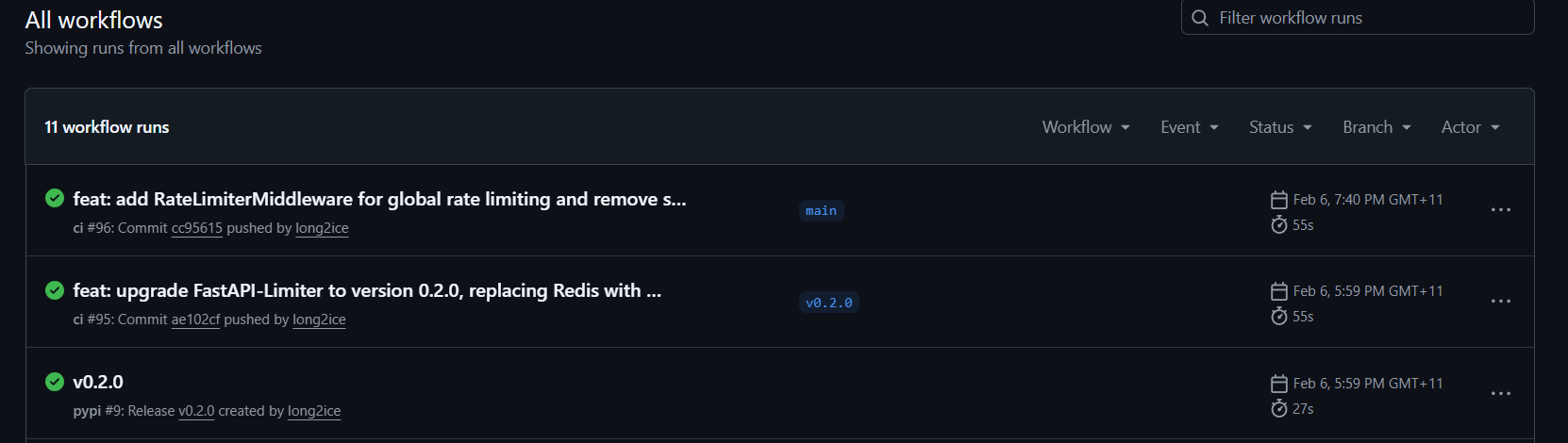
CICD
Publishing to PyPI
We publish to PyPI using Github releases. Steps are as follows:
- Manually update the version in
pyproject.tomlfile using a PR and merge to main. Useuv version --bump {patch/minor/major}to update the version. - Create a new release in Github with the tag name as the version number. This
will trigger the
publishworkflow. In the Release window, type in the version number and it will prompt to create a new tag. - Verify the release in PyPI
Project details
Download files
Download the file for your platform. If you're not sure which to choose, learn more about installing packages.
Source Distribution
Built Distribution
Filter files by name, interpreter, ABI, and platform.
If you're not sure about the file name format, learn more about wheel file names.
Copy a direct link to the current filters
File details
Details for the file ab_fastapi_limiter-0.2.1.tar.gz.
File metadata
- Download URL: ab_fastapi_limiter-0.2.1.tar.gz
- Upload date:
- Size: 8.3 kB
- Tags: Source
- Uploaded using Trusted Publishing? No
- Uploaded via: uv/0.11.8 {"installer":{"name":"uv","version":"0.11.8","subcommand":["publish"]},"python":null,"implementation":{"name":null,"version":null},"distro":{"name":"Ubuntu","version":"24.04","id":"noble","libc":null},"system":{"name":null,"release":null},"cpu":null,"openssl_version":null,"setuptools_version":null,"rustc_version":null,"ci":true}
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
a4fc6762dfe91ce78677e905e2e12db19dc374316a7f3730e6d27f64270db94b
|
|
| MD5 |
615a61ff1afd9bc1452357cb5eb2dbc5
|
|
| BLAKE2b-256 |
199720a69cefdc4d5529cc9a02fb632c4c5d2ddecd5e0ecfef530b553660a3fc
|
File details
Details for the file ab_fastapi_limiter-0.2.1-py3-none-any.whl.
File metadata
- Download URL: ab_fastapi_limiter-0.2.1-py3-none-any.whl
- Upload date:
- Size: 8.0 kB
- Tags: Python 3
- Uploaded using Trusted Publishing? No
- Uploaded via: uv/0.11.8 {"installer":{"name":"uv","version":"0.11.8","subcommand":["publish"]},"python":null,"implementation":{"name":null,"version":null},"distro":{"name":"Ubuntu","version":"24.04","id":"noble","libc":null},"system":{"name":null,"release":null},"cpu":null,"openssl_version":null,"setuptools_version":null,"rustc_version":null,"ci":true}
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
6bf5fa6c99d84401f05be5c40e37e5d9fa0b7536f6da8bf2c9f57e4d58d0c4d5
|
|
| MD5 |
7d8f0b1c75a4109c2d254259bf1a832b
|
|
| BLAKE2b-256 |
3b68e482bb51840dae906275713ca2fd118d1aeb1b6b8e4e47bf8788ecdec755
|