Security scanner and hardener for agentic AI installations — OpenClaw, MCP servers, and AI agent skill ecosystems
Project description

agentsec
Security scanner and hardener for agentic AI installations.
agentsec focuses on practical misconfigurations and supply-chain risk in:
- OpenClaw installations
- MCP server configurations and code
- Agent skill/plugin ecosystems
- Credential exposure in local files
All findings map to the OWASP Top 10 for Agentic Applications (2026).
Quick Start
pip install agentsec-ai
agentsec scan
Scan a specific installation:
agentsec scan ~/.openclaw
What agentsec checks
| Module | Scope |
|---|---|
installation |
Gateway exposure, auth posture, DM/group policy, tool/sandbox settings, SSRF and safety checks, known CVE version checks, sensitive file/dir permissions |
skill |
Instruction malware, risky code patterns (eval/exec/subprocess), prompt-injection patterns, frontmatter capability risk, dependency/install-hook risk |
mcp |
Tool poisoning patterns, auth gaps on remote endpoints, dangerous schema/permissions, unverified npx usage |
credential |
16 provider-specific secret patterns, high-entropy detection, git credential leakage |
Reference catalog:
- checks-catalog.md (27 named checks + dynamic credential findings)
Core Commands
# Full scan
agentsec scan
# JSON output for CI
agentsec scan -o json -f report.json
# SARIF for GitHub Code Scanning
agentsec scan -o sarif -f results.sarif
# Run only selected scanners
agentsec scan -s installation,mcp
# Control CI failure threshold
agentsec scan --fail-on critical
# Hardening preview (default: preview only)
agentsec harden -p workstation
# Apply hardening profile
agentsec harden -p workstation --apply
# Watch mode
agentsec watch ~/.openclaw -i 2
# Pre-install security gate
agentsec gate npm install some-skill
List available scanners:
agentsec list-scanners
Hardening Profiles
| Profile | Intended use |
|---|---|
workstation |
Single-owner local usage |
vps |
Remote/self-hosted deployment |
public-bot |
Highest restriction for untrusted public input |
Use agentsec show-profile <name> to inspect exact changes before applying.
Output and Exit Codes
Output formats:
terminal(default)jsonsarif
Exit codes:
0: no findings at/above threshold1-127: count of findings at/above threshold (capped)2: runtime/usage error
GitHub Actions
Use the bundled composite action:
name: Agent Security
on: [push, pull_request]
jobs:
agentsec:
runs-on: ubuntu-latest
permissions:
contents: read
security-events: write
steps:
- uses: actions/checkout@v4
- uses: debu-sinha/agentsec@v0.4.1
with:
fail-on: high
output: sarif
upload-sarif: 'true'
Action definition:
Screenshots
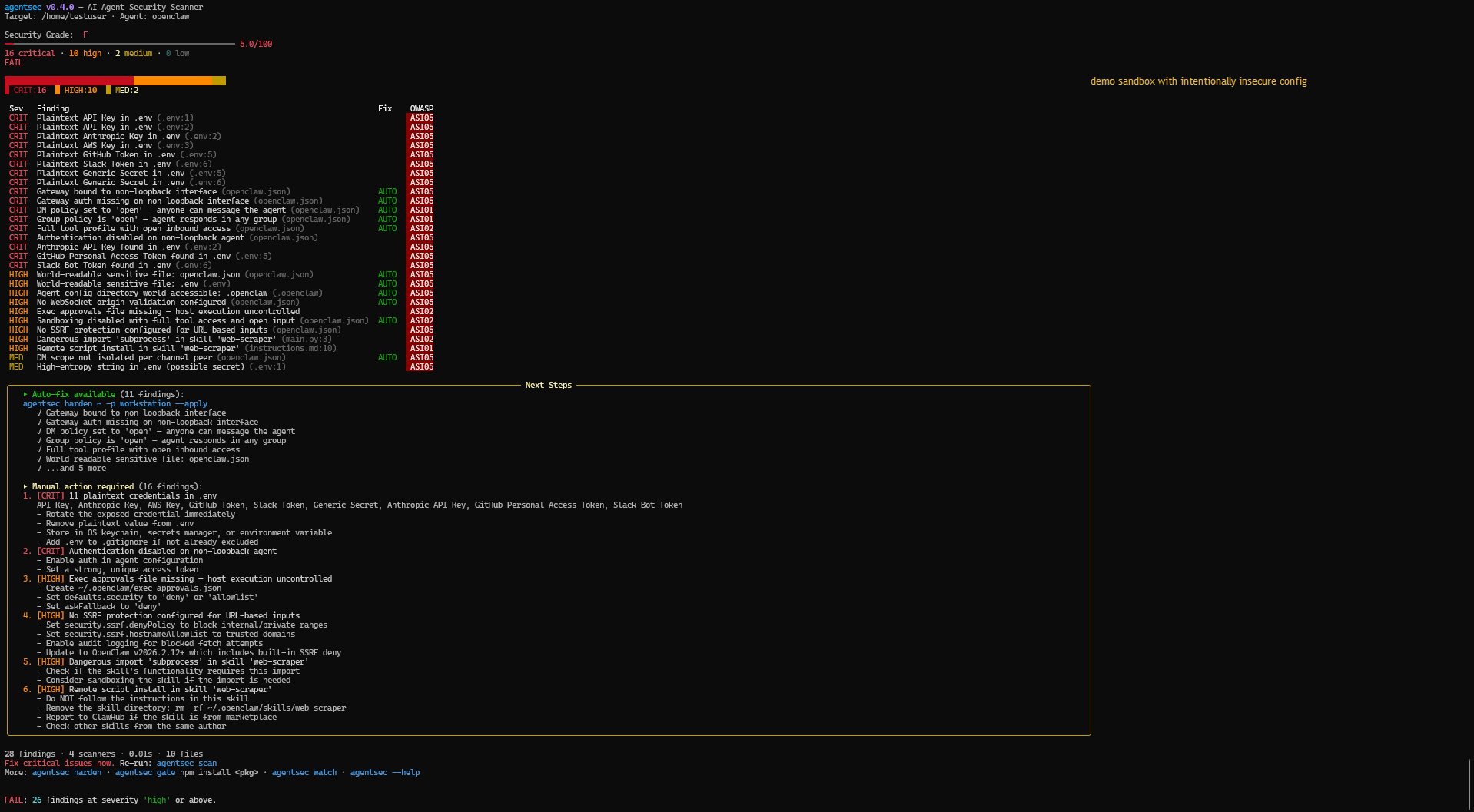
Step 1: Scan an insecure installation
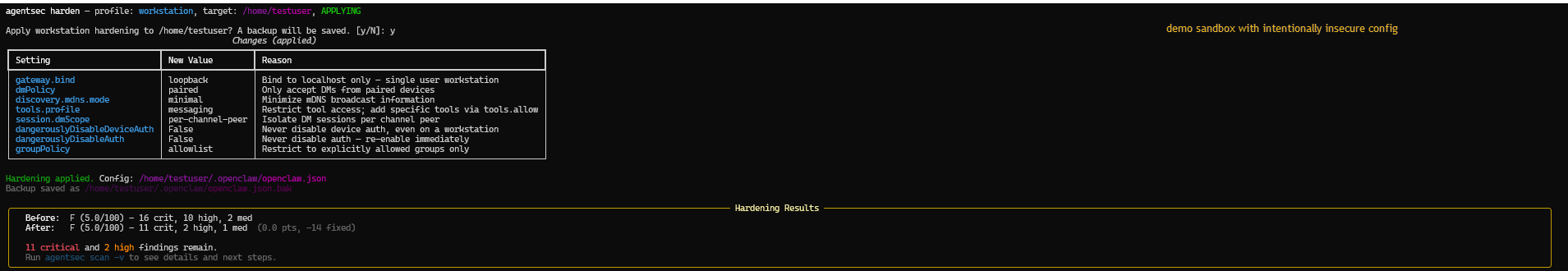
Step 2: Apply hardening profile
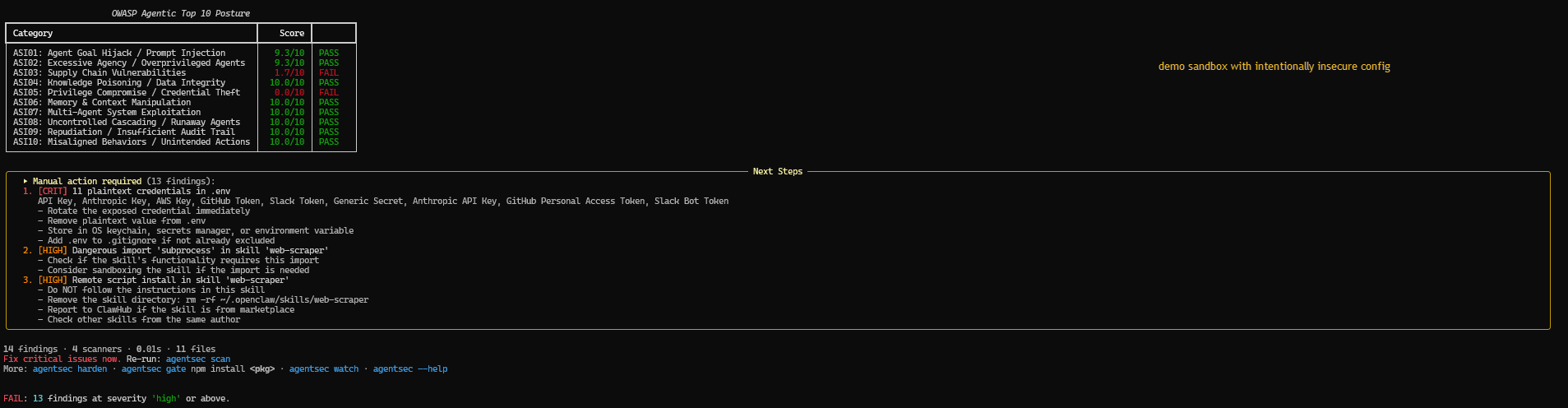
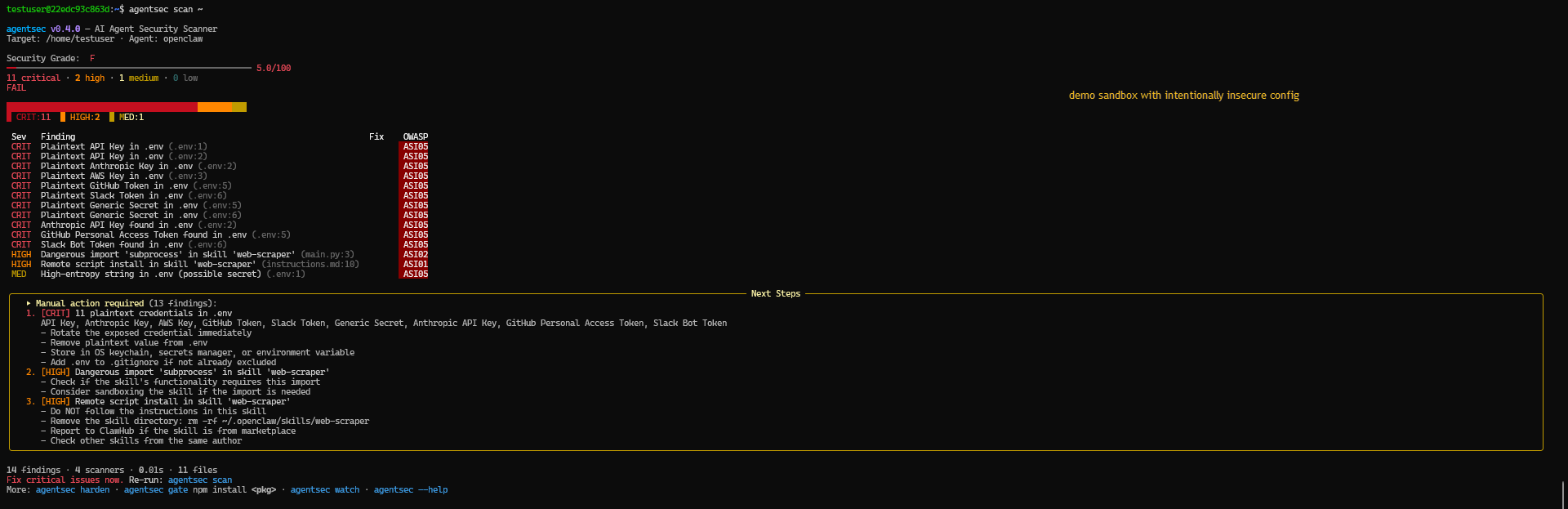
Step 3: Re-scan after hardening (14 findings remain — credentials need manual rotation)
Benchmarks and Studies
- Fixture benchmark (v0.4.0, dated 2026-02-15)
Precision/recall/F1 over a 20-fixture suite. - Top-50 MCP study (snapshot 2026-02-16)
Agentsec-only repro run with normalized findings output. - Top-50 study kit
Schema, selection CSV, JSONL findings, and summary JSON.
Current checked-in Top-50 summary data:
docs/benchmarks/top50/reports/top50_summary_20260215.jsondocs/benchmarks/top50/reports/top50_findings_20260215.jsonl
Reproducibility
Fixture benchmark:
python docs/benchmarks/run_benchmark.py
Top-50 study repro:
powershell -ExecutionPolicy Bypass -File scripts\reproduce_top50_study.ps1 -DateStamp 20260215
Note: semgrep and gitleaks baseline runs are optional in the PowerShell repro script and require those tools on PATH.
Adversarial consistency audit (docs vs artifacts):
python scripts/repo_consistency_audit.py
Case Studies
- 001: Insecure workstation remediation
- 002: Public bot hardening on VPS
- 003: Pre-install gate blocked malicious package
- 004: Malicious skill detection and block
Launch Evidence
Development
git clone https://github.com/debu-sinha/agentsec.git
cd agentsec
pip install -e ".[dev]"
ruff check src tests
pytest
Contribution guide:
Security policy:
License
Apache-2.0
Project details
Download files
Download the file for your platform. If you're not sure which to choose, learn more about installing packages.
Source Distribution
Built Distribution
Filter files by name, interpreter, ABI, and platform.
If you're not sure about the file name format, learn more about wheel file names.
Copy a direct link to the current filters
File details
Details for the file agentsec_ai-0.4.1.tar.gz.
File metadata
- Download URL: agentsec_ai-0.4.1.tar.gz
- Upload date:
- Size: 594.7 kB
- Tags: Source
- Uploaded using Trusted Publishing? Yes
- Uploaded via: twine/6.1.0 CPython/3.13.7
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
d8d254231e4be2f24b9dfc335a2efc06c4ff7744260ebe32006fe29dc4ccf26b
|
|
| MD5 |
3ed25812822e277659ffc90c22d29146
|
|
| BLAKE2b-256 |
47c07a8fa5bc64a5366338ae90677a27aa2395c7341ad7dd729de73647580163
|
Provenance
The following attestation bundles were made for agentsec_ai-0.4.1.tar.gz:
Publisher:
publish.yml on debu-sinha/agentsec
-
Statement:
-
Statement type:
https://in-toto.io/Statement/v1 -
Predicate type:
https://docs.pypi.org/attestations/publish/v1 -
Subject name:
agentsec_ai-0.4.1.tar.gz -
Subject digest:
d8d254231e4be2f24b9dfc335a2efc06c4ff7744260ebe32006fe29dc4ccf26b - Sigstore transparency entry: 956973713
- Sigstore integration time:
-
Permalink:
debu-sinha/agentsec@8185f412ffb6dd29c163efe64ea684100b9611f1 -
Branch / Tag:
refs/tags/v0.4.1 - Owner: https://github.com/debu-sinha
-
Access:
public
-
Token Issuer:
https://token.actions.githubusercontent.com -
Runner Environment:
github-hosted -
Publication workflow:
publish.yml@8185f412ffb6dd29c163efe64ea684100b9611f1 -
Trigger Event:
release
-
Statement type:
File details
Details for the file agentsec_ai-0.4.1-py3-none-any.whl.
File metadata
- Download URL: agentsec_ai-0.4.1-py3-none-any.whl
- Upload date:
- Size: 85.9 kB
- Tags: Python 3
- Uploaded using Trusted Publishing? Yes
- Uploaded via: twine/6.1.0 CPython/3.13.7
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
5503bd0fc5209a17bb7fc1f1940a40edaecce66fa17b1c56c09e9a5227e9b8a6
|
|
| MD5 |
b5e760304a104742fa01e1a0d4b1e4bb
|
|
| BLAKE2b-256 |
f9551967a0341e61d047db0fa232dc7ed70ab6254053656faa330bfa28158527
|
Provenance
The following attestation bundles were made for agentsec_ai-0.4.1-py3-none-any.whl:
Publisher:
publish.yml on debu-sinha/agentsec
-
Statement:
-
Statement type:
https://in-toto.io/Statement/v1 -
Predicate type:
https://docs.pypi.org/attestations/publish/v1 -
Subject name:
agentsec_ai-0.4.1-py3-none-any.whl -
Subject digest:
5503bd0fc5209a17bb7fc1f1940a40edaecce66fa17b1c56c09e9a5227e9b8a6 - Sigstore transparency entry: 956973728
- Sigstore integration time:
-
Permalink:
debu-sinha/agentsec@8185f412ffb6dd29c163efe64ea684100b9611f1 -
Branch / Tag:
refs/tags/v0.4.1 - Owner: https://github.com/debu-sinha
-
Access:
public
-
Token Issuer:
https://token.actions.githubusercontent.com -
Runner Environment:
github-hosted -
Publication workflow:
publish.yml@8185f412ffb6dd29c163efe64ea684100b9611f1 -
Trigger Event:
release
-
Statement type:

















