Deal with bad characters easily during exploit writing with badchars.
Project description
badbyte
Deal with bad characters easily during exploit writing with badchars.
Table of Contents
↑Instalation
using pip:
pip3 install badbyte
or from repo:
git clone git@github.com:C3l1n/badbyte.git
cd badbyte
pip3 install .
↑Usage
You can always use:
badbyte --help
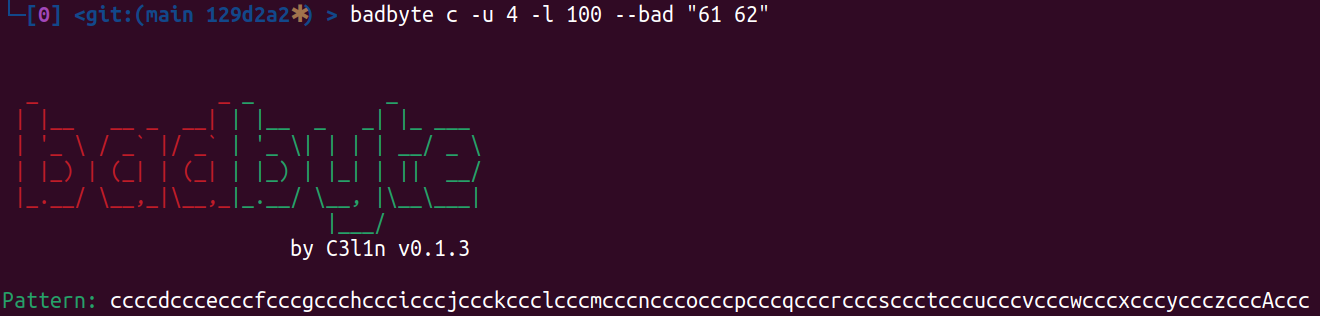
↑Cyclic pattern generate
It is useful to search for offset at which you should put your sniper shot constants. For example return address: you generate pattern with this function, trigger vulnerability with generated payload. EIP value (remember about little ending in x86) has uniq part of pattern and offset of that part could be calculated with badbyte parse (see next chapter).
badbyte c -u 4 -l 100 --bad "61 62"
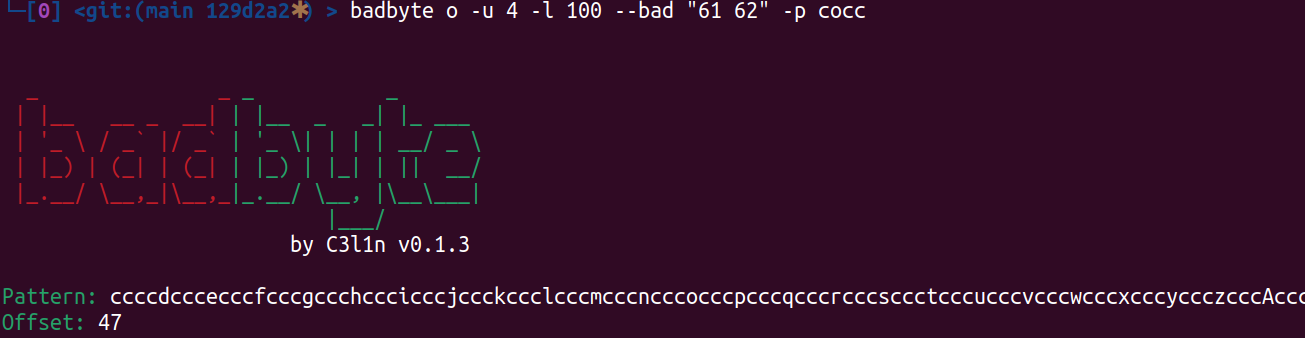
↑Search for offset in cyclic pattern
Search for offset of provided part in --pattern argument.
badbyte o -u 4 -l 100 --bad "61 62" -p cocc
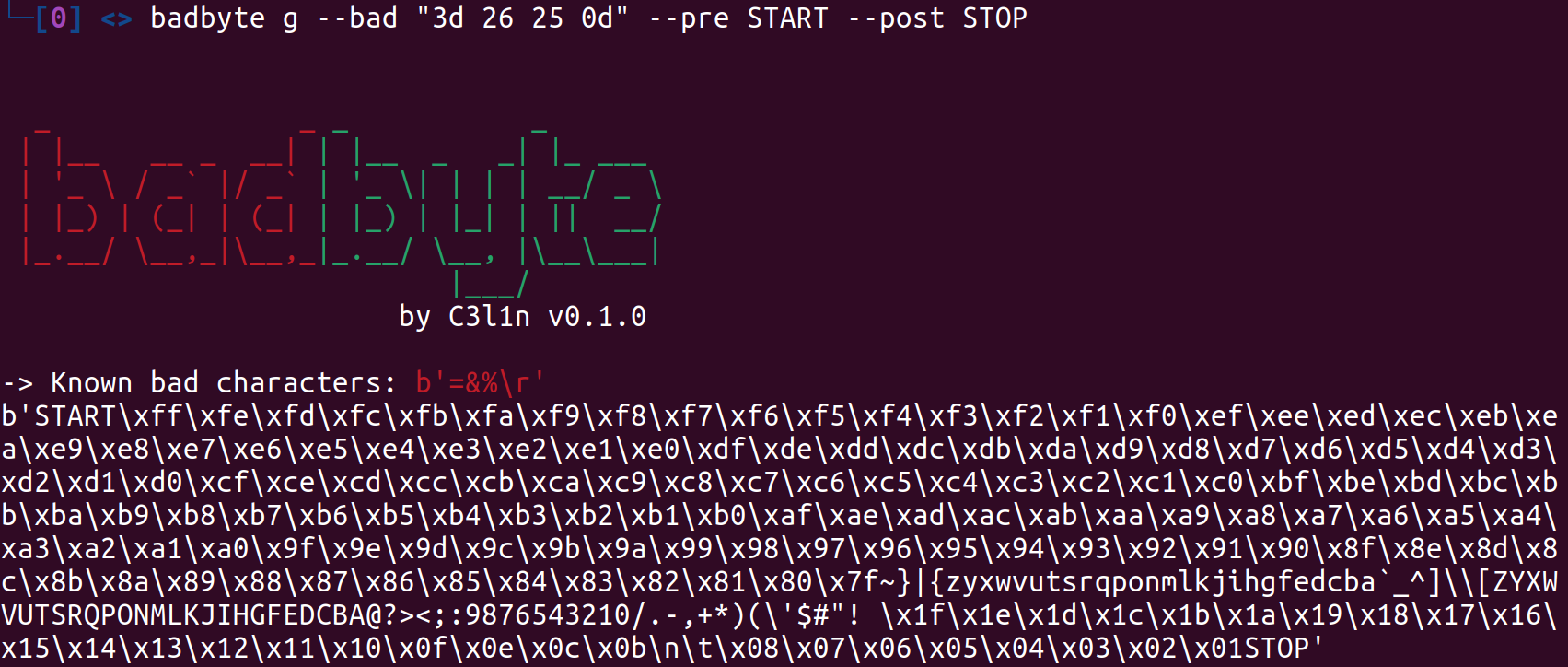
↑Generate payload to check all characters
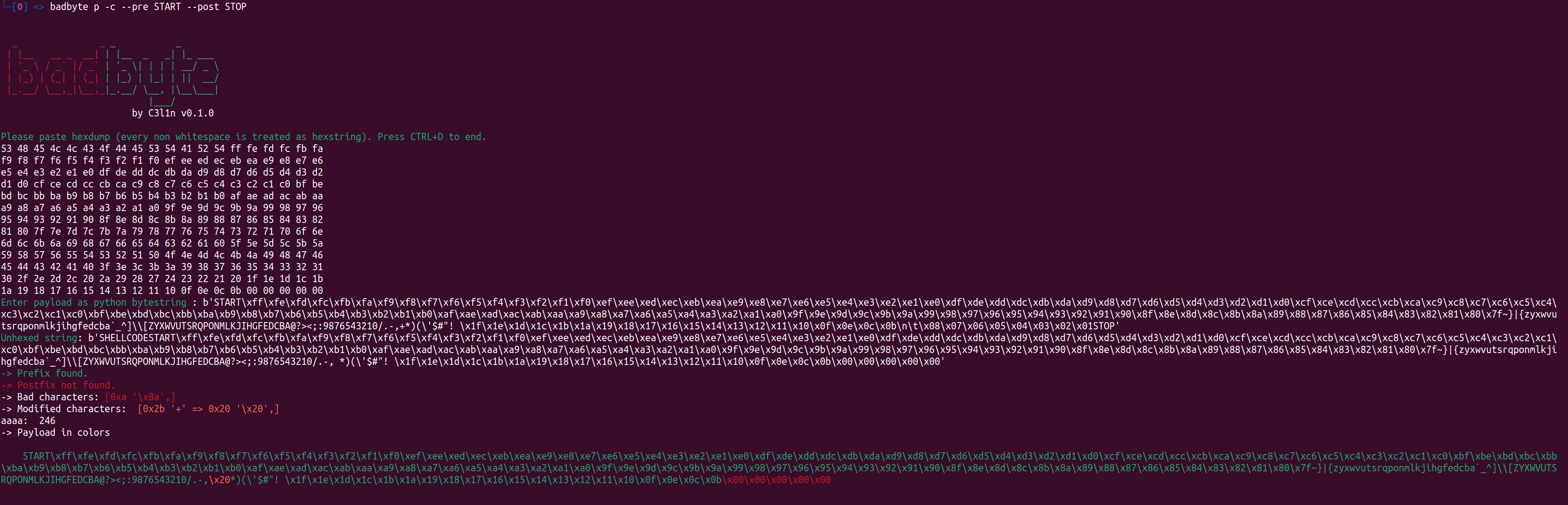
badbyte g --bad "3d 26 25 0d" --pre START --post STOP
use:
- --bad to supply hexascii values of bad characters
- --pre to set string for marking start point (or leave default)
- --post to set string for marking stop point (or leave default)
Then use payload in your exploit and fire it.
↑Analyze memory dumped after trigger
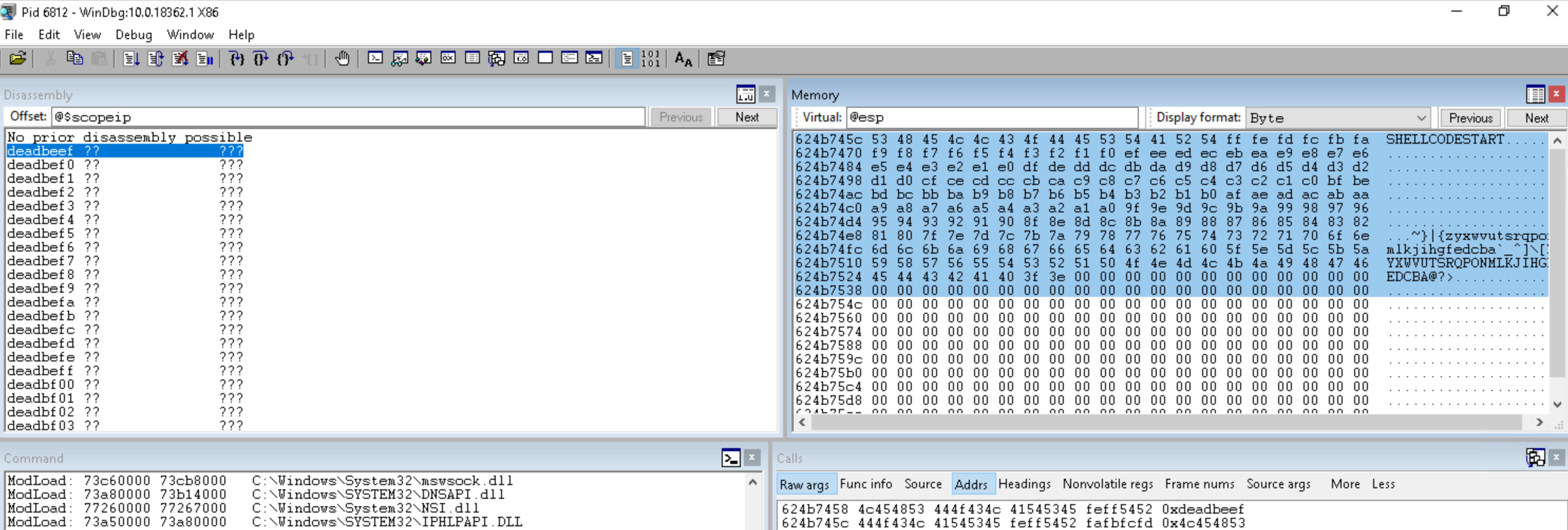
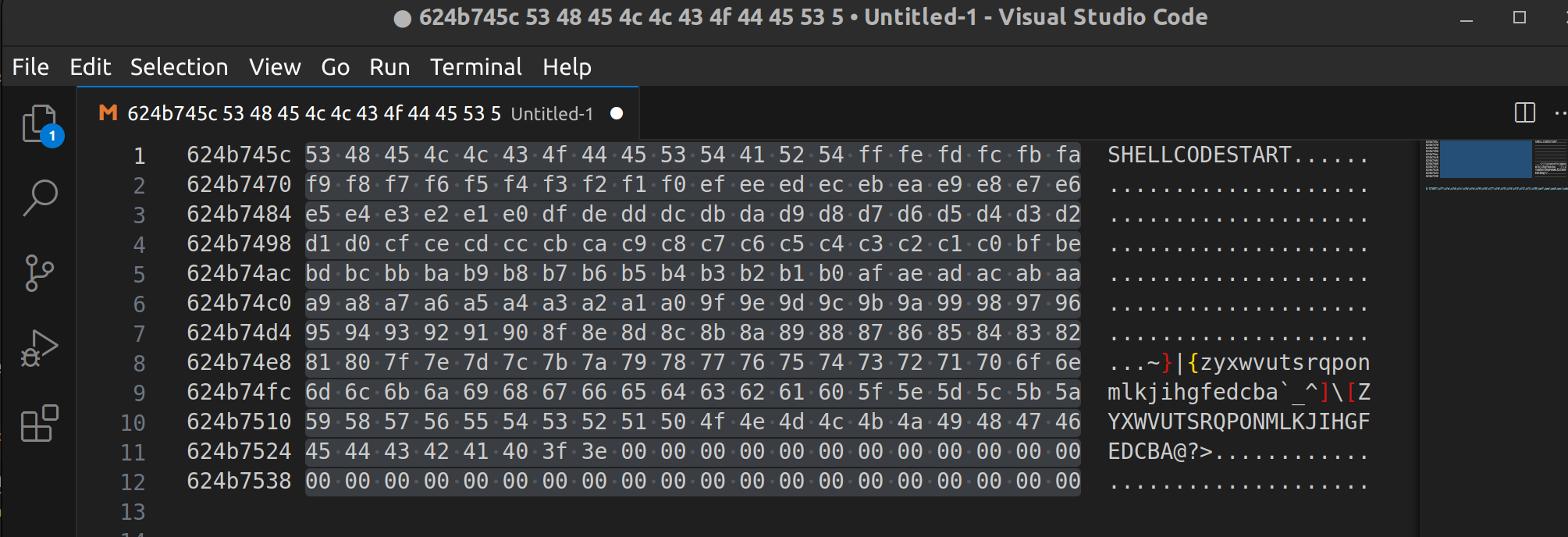
Copy hexascii from memory dump of your favourite debugger i.e. windbg:
remember to skip addresses and ascii representation. I use vim and column select or visual studio code and alt+shift select.
Fire badbyte to analyze output:
badbyte p -c --pre START --post STOP
↑Programatically use
Documentation not made (feel free to read code) but you can find in example/programatically_generate_payload.py example of payload generation in exploit.
Project details
Release history Release notifications | RSS feed
Download files
Download the file for your platform. If you're not sure which to choose, learn more about installing packages.
Source Distribution
Built Distribution
Filter files by name, interpreter, ABI, and platform.
If you're not sure about the file name format, learn more about wheel file names.
Copy a direct link to the current filters
File details
Details for the file badbyte-0.1.5.tar.gz.
File metadata
- Download URL: badbyte-0.1.5.tar.gz
- Upload date:
- Size: 6.3 kB
- Tags: Source
- Uploaded using Trusted Publishing? Yes
- Uploaded via: twine/5.0.0 CPython/3.12.3
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
41da3a3f5f20dc2530448bb6006d5a44ccac547116b141ae23d4f1998d73a346
|
|
| MD5 |
c1582e857f1b9e4702deb562c569a252
|
|
| BLAKE2b-256 |
28e1ae944a199c38c45dce7a077132669ceb2e75e0578d53d828c3c635efb789
|
File details
Details for the file badbyte-0.1.5-py3-none-any.whl.
File metadata
- Download URL: badbyte-0.1.5-py3-none-any.whl
- Upload date:
- Size: 7.2 kB
- Tags: Python 3
- Uploaded using Trusted Publishing? Yes
- Uploaded via: twine/5.0.0 CPython/3.12.3
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
2b7caf0929ff781377a84b29da5e3dbe8eb4552410d486b2ca94cf2060089724
|
|
| MD5 |
6500b175c288408c750e0ce7bb6bf22f
|
|
| BLAKE2b-256 |
808588d992ebe9114a5ea7545cd3c1ebbe88b72083f60c2f5da785bca2779408
|