Python OTP
Project description
che_guevara_otp
This module generates one-time passcodes that are based either on a counter or time using a secret key that is assumed known by server and client.
The counter-based passcodes are hash-based one-time passcodes (HOTP) and are defined in RFC 4226. The time-based passcodes are time-based one-time passcodes (TOTP) and are defined in RFC 6238. For HOTP, the pseudorandom function used is HMAC-SHA-1 and the associated counter should be incremented after each passcode generation. TOTP is HOTP with a specified time interval for validity. A common time interval is 30 seconds.
setup
pip install che_guevara_otpTo set up a launcher for the che_guevara_otp command, copy Che.svg to /usr/share/icons/hicolor/scalable/apps/ and copy che_guevara_otp.desktop to /usr/share/applications/, for example:
sudo cp /usr/local/lib/python3.5/dist-packages/che_guevara_otp-2018.5.11.1653-py3.5.egg/che_guevara_otp/data/Che.svg /usr/share/icons/hicolor/scalable/apps/
sudo cp /usr/local/lib/python3.5/dist-packages/che_guevara_otp-2018.5.11.1653-py3.5.egg/che_guevara_otp/data/che_guevara_otp.desktop /usr/share/applications/module
HOTP passcodes can be generated in a way like the following:
>>> import che_guevara_otp
>>> secret = "XXXXXXXXXXXXXXXX"
>>> for nonce in range(0, 3):
... print(che_guevara_otp.HOTP(secret = secret, nonce = nonce))
...
561452
686073
840123TOTP passcodes can be generated in a way like the following, where the default time interval is 30 seconds:
>>> import che_guevara_otp
>>> secret = "XXXXXXXXXXXXXXXX"
>>> print(che_guevara_otp.TOTP(secret = secret))
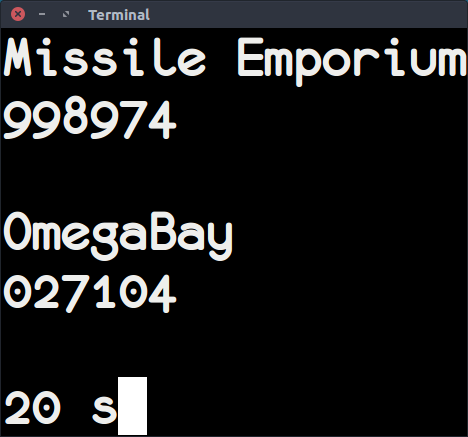
826402che_guevara_otp terminal loop display
The command che_guevara_otp displays time-based one-time passcodes at 30 second intervals based on secrets stored in a specified file ~/.secrets. The file is unencrypted plaintext so userspace encryption combined with other security is assumed. The contents of the secrets file should be of the following form:
OmegaBay: XXXXXXXXXXXXXXXXXXXXXXXX Missile Emporium: YYYYYYYYYYYYYYYYYYYYYYYY
future
Under consideration are functions to install the launcher and icon infrastructure based on Python version information.
Project details
Release history Release notifications | RSS feed
Download files
Download the file for your platform. If you're not sure which to choose, learn more about installing packages.
Source Distribution
File details
Details for the file che_guevara_otp-2021.11.4.210.tar.gz.
File metadata
- Download URL: che_guevara_otp-2021.11.4.210.tar.gz
- Upload date:
- Size: 5.9 MB
- Tags: Source
- Uploaded using Trusted Publishing? No
- Uploaded via: Python-urllib/3.8
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
a9349bc646ecaae532ddc752bbac91f921deb5b34a3bb9a2c49d2b0a33488966
|
|
| MD5 |
be3488497a78a1a8ca9e254cf4345286
|
|
| BLAKE2b-256 |
3c0c75db441f3e14baf79b5226a48dd973157c60d88928bd31a81c154ef20d69
|