Common User Password Profiler
Project description
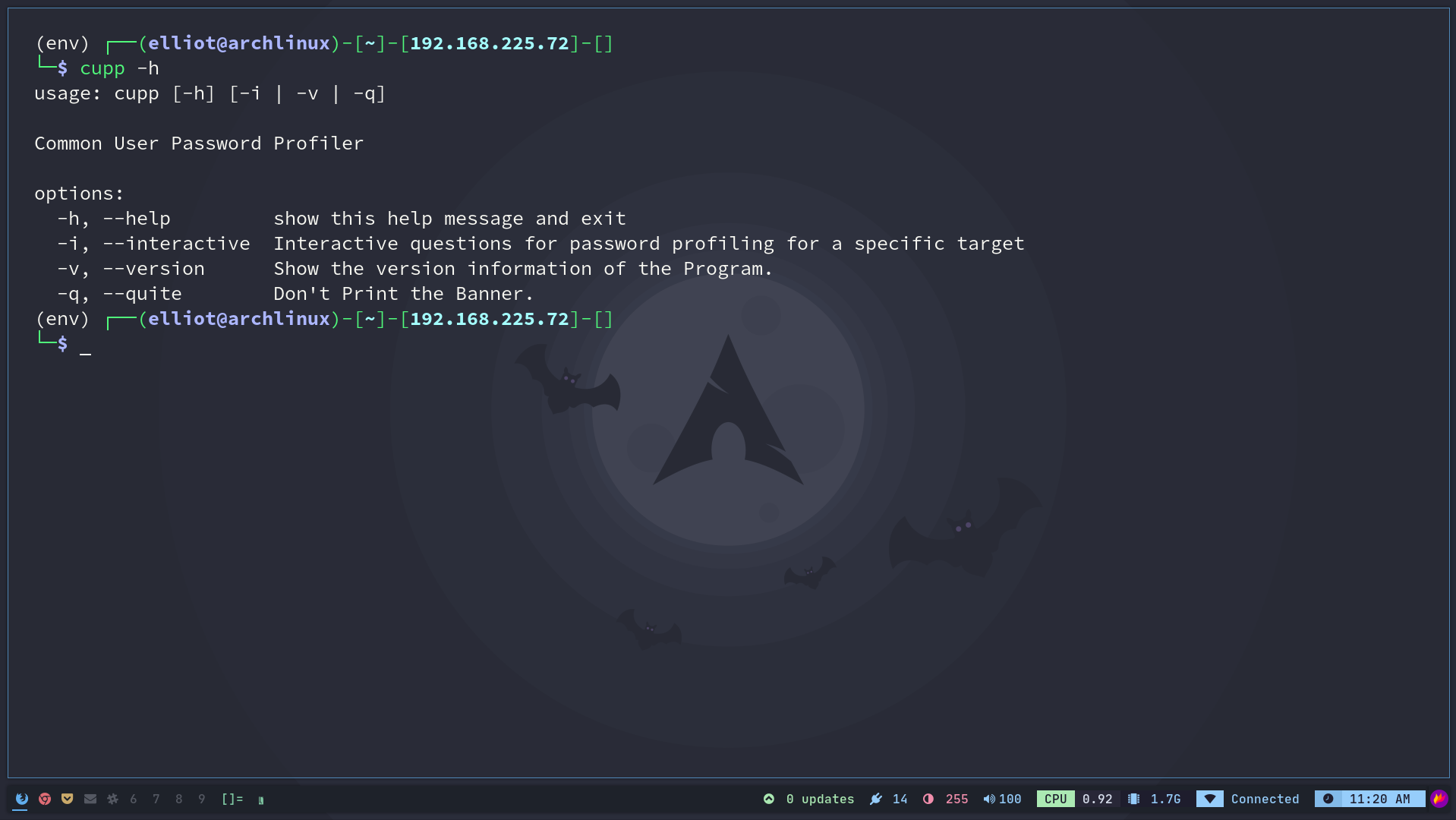
cupp
Common User Password Profiler
Description
CUPP (Common User Password Profile) is a tool to generate target specific wordlists based on their details provided.
Version
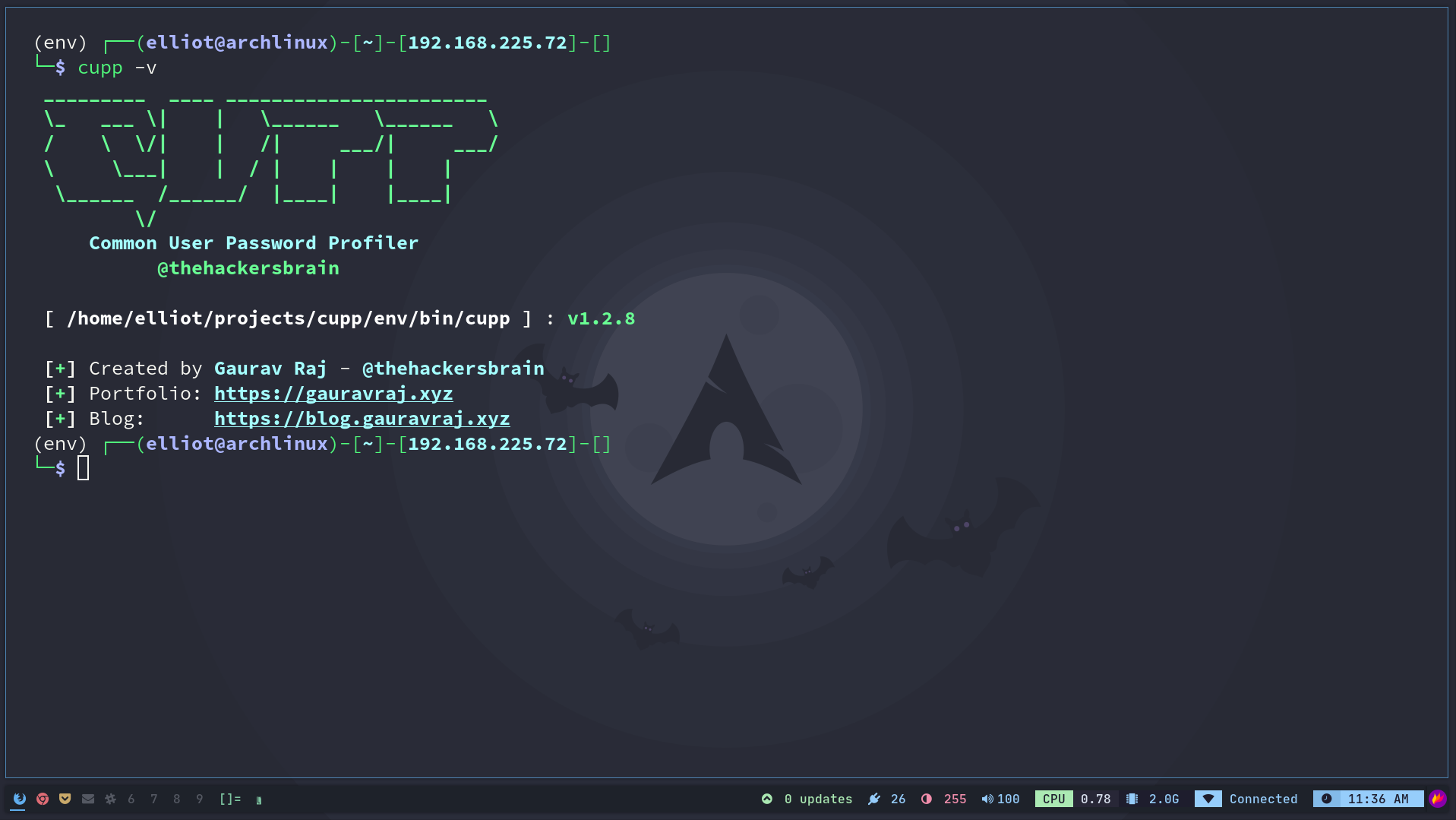
**Cupp v1.3.3
Installation
Using PIP3
- Create a new Python Virtual Environment
python3 -m venv env
- Activate the virtualenv
source env/bin/activate
- Install and run the tool
pip3 install -e . && cupp -v
- Onliner
python3 -m venv && source env/bin/activate && pip3 install -e . && cupp -v
Using this repo
- Git clone the respository
git clone https://github.com/thehackersbrain/cupp.git
- Change the directory to
cuppcd cupp
- Create new python virtualenv and activate it
python3 -m venv env && source env/bin/activate
- Install the tool using
pip3pip3 install -e .
- Oneliner
git clone https://github.com/thehackersbrain/cupp.git && cd cupp && python3 -m venv env && source env/bin/activate && pip3 install -e . && cupp -v
Screenshots
Credit
This tool is originally designed by Mebus here. I tried to enhance the UI and added some functionality than the previous version and removed some redundant code, basically it's a mess ;)
Social Handles
Project details
Release history Release notifications | RSS feed
Download files
Download the file for your platform. If you're not sure which to choose, learn more about installing packages.
Source Distribution
Built Distribution
Filter files by name, interpreter, ABI, and platform.
If you're not sure about the file name format, learn more about wheel file names.
Copy a direct link to the current filters
File details
Details for the file cupp-1.3.3.tar.gz.
File metadata
- Download URL: cupp-1.3.3.tar.gz
- Upload date:
- Size: 7.2 kB
- Tags: Source
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/4.0.0 CPython/3.10.4
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
f5e7ccc44ff3b2e2a2e0e74361712e81086659c0badd782be576c6b80b06557e
|
|
| MD5 |
76aeedfc73c0423cfb8b0fa29ad62cbe
|
|
| BLAKE2b-256 |
ec43d532a4a0e9ebd79863e2adf76dc314e2999068bf7491920204330ff34c1c
|
File details
Details for the file cupp-1.3.3-py3-none-any.whl.
File metadata
- Download URL: cupp-1.3.3-py3-none-any.whl
- Upload date:
- Size: 7.7 kB
- Tags: Python 3
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/4.0.0 CPython/3.10.4
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
43327747d08c4ffa90f4b7ad13247c56f79728331bea8861ea4b69329a4f3bf2
|
|
| MD5 |
c32f318c50fc5249b407a1fb5e94ced6
|
|
| BLAKE2b-256 |
5dbf7617a6899e54a041a6d65107c1ad4cc51e5bf6c662307e008ae8aeba60ac
|