Django app to map Keycloak roles and groups to Django user permissions and groups using OIDC
Project description
django-keyclock-oidc
This project depends on mozilla-django-oidc and map keycloak roles and groups to django user permissions and groups.
Features
- Automatic mapping of Keycloak roles and groups to Django user permissions and groups
- Django admin login integration with Keycloak
- OIDC authentication with Keycloak
Installation
- You can install the package via your python package manager, example:
pip install mozilla-django-oidc
pip install django-keycloak-oidc
# or
poetry add mozilla-django-oidc
poetry add django-keycloak-oidc
# or
uv add mozilla-django-oidc
uv add django-keycloak-oidc
- Add
django_keycloak_oidcandmozilla_django_oidcto yourINSTALLED_APPSinsettings.py:
INSTALLED_APPS = [
"django_keycloak_oidc", # top of admin app
"django.contrib.admin",
"django.contrib.auth",
"mozilla_django_oidc", # bottom of auth app
...
]
- Add the authentication backend to your
AUTHENTICATION_BACKENDSinsettings.py:
AUTHENTICATION_BACKENDS = [
"django_keycloak_oidc.auth.KeyCloakAuthenticationBackend", # here
"django.contrib.auth.backends.ModelBackend", # django default (need it too)
..., # and other
]
- Add
mozilla_django_oidcurls to yoururls.py:
urlpatterns = [
...,
path("oidc/", include("mozilla_django_oidc.urls")),
...,
]
Important Note: If you changed your admin root path, make sure that the oidc/ and admin/ paths are in same root.
for example:
urlpatterns = [
...,
path(
"root/", # your root (if you did it)
include(
[
...,
path("admin/", admin.site.urls),
path("oidc/", include("mozilla_django_oidc.urls")),
...,
]
)
),
...,
]
- Add the settings_context to your context_processors in
settings.py:
TEMPLATES = [
{
...,
"OPTIONS": {
"context_processors": [
...,
"django_keycloak_oidc.context_processor.settings_context", # here
],
},
},
]
- Run migrations (Done):
python manage.py migrate
Configuration
You can see configuration of the original project here.
-
Keycloak setup:
- You need to add
Group MembershipandUser Realm Rolefrom Client scopes -> profile -> Mappers -> Add mapper -> By configuration:- User Realm Role:
- Mapper Type:
User Realm Role - Name:
roles - Token Claim Name:
roles - Add to ID token, Add to access token, Add to userinfo, Add to token introspection:
on
- Mapper Type:
- Group Membership:
- Mapper Type:
Group Membership - Name:
groups - Token Claim Name:
groups - Full group path:
off. if its on, you must enter group name in django admin with full path. - Add to ID token, Add to access token, Add to userinfo, Add to token introspection:
on
- Mapper Type:
- User Realm Role:
- And create you
rolesandgroupsin your Keycloak console.
- You need to add
-
My Django sample configuration(
settings.py) is as below:
OIDC_RP_CLIENT_ID = "<client-id>"
OIDC_RP_CLIENT_SECRET = "<client-secret>"
OIDC_RP_SIGN_ALGO = "RS256"
OIDC_VERIFY_SSL = False
OIDC_OP_AUTHORIZATION_ENDPOINT = "http://<keycloak-host>/realms/<realm>/protocol/openid-connect/auth"
OIDC_OP_TOKEN_ENDPOINT = "http://<keycloak-host>/realms/<realm>/protocol/openid-connect/token"
OIDC_OP_USER_ENDPOINT = "http://<keycloak-host>/realms/<realm>/protocol/openid-connect/userinfo"
OIDC_OP_JWKS_ENDPOINT = "http://<keycloak-host>/realms/<realm>/protocol/openid-connect/certs"
LOGIN_URL = "/oidc/authenticate/"
LOGIN_REDIRECT_URL = "/leasing/admin/"
LOGIN_REDIRECT_URL_FAILURE = "/leasing/admin/"
LOGOUT_REDIRECT_URL = "/leasing/admin/login/"
# (django-keycloak-oidc) settings for customizing the login button in django admin login page(make sure you did step 5 in installation):
KEYCLOAK_DJANGO_ADMIN_LOGIN_VISIBLE = True
KEYCLOAK_DJANGO_ADMIN_LOGIN_DIRECTION = "rtl"
KEYCLOAK_DJANGO_ADMIN_LOGIN_TEXT = "Login with"
KEYCLOAK_DJANGO_ADMIN_LOGIN_LOGO = "https://karnameh.com/assets/logos/karnameh-logo.svg"
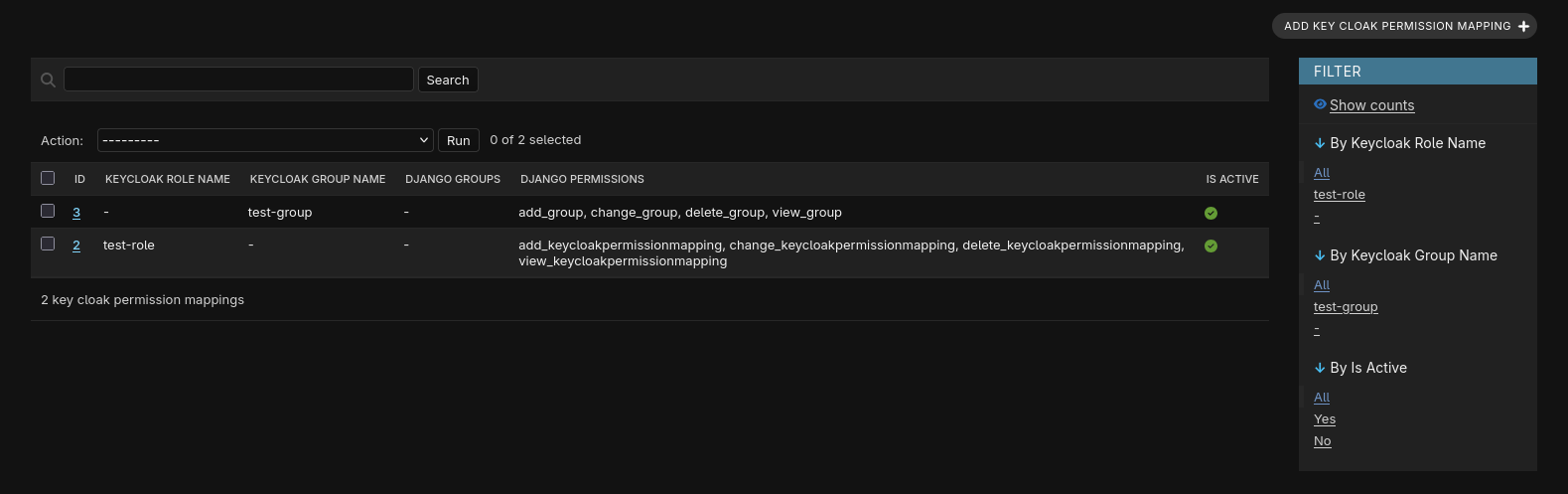
- Go to your Django admin and start mapping:
Project details
Download files
Download the file for your platform. If you're not sure which to choose, learn more about installing packages.
Source Distribution
Built Distribution
Filter files by name, interpreter, ABI, and platform.
If you're not sure about the file name format, learn more about wheel file names.
Copy a direct link to the current filters
File details
Details for the file django_keycloak_oidc-0.3.255.tar.gz.
File metadata
- Download URL: django_keycloak_oidc-0.3.255.tar.gz
- Upload date:
- Size: 9.5 kB
- Tags: Source
- Uploaded using Trusted Publishing? Yes
- Uploaded via: twine/6.1.0 CPython/3.13.7
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
bf91183cac74aada4067064ef9a4649d6ed516f92c5b118b7536a1de2591d1b7
|
|
| MD5 |
32103badc0dee5ea77ccd16818c865fa
|
|
| BLAKE2b-256 |
ddc7074cd049ae4ed7a9728e44c0e39453042de95773e3f44a89be9438c7db58
|
Provenance
The following attestation bundles were made for django_keycloak_oidc-0.3.255.tar.gz:
Publisher:
publish.yml on karnameh-tech/django-keycloak-oidc
-
Statement:
-
Statement type:
https://in-toto.io/Statement/v1 -
Predicate type:
https://docs.pypi.org/attestations/publish/v1 -
Subject name:
django_keycloak_oidc-0.3.255.tar.gz -
Subject digest:
bf91183cac74aada4067064ef9a4649d6ed516f92c5b118b7536a1de2591d1b7 - Sigstore transparency entry: 793248974
- Sigstore integration time:
-
Permalink:
karnameh-tech/django-keycloak-oidc@f63fd8c4f42031af183b83cf5b6d801e23ae9dff -
Branch / Tag:
refs/heads/main - Owner: https://github.com/karnameh-tech
-
Access:
public
-
Token Issuer:
https://token.actions.githubusercontent.com -
Runner Environment:
github-hosted -
Publication workflow:
publish.yml@f63fd8c4f42031af183b83cf5b6d801e23ae9dff -
Trigger Event:
workflow_dispatch
-
Statement type:
File details
Details for the file django_keycloak_oidc-0.3.255-py3-none-any.whl.
File metadata
- Download URL: django_keycloak_oidc-0.3.255-py3-none-any.whl
- Upload date:
- Size: 10.2 kB
- Tags: Python 3
- Uploaded using Trusted Publishing? Yes
- Uploaded via: twine/6.1.0 CPython/3.13.7
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
937888c896be1cb1b6c3ad92373c64b9e182a1ae175ab3236b6c199e192dbad6
|
|
| MD5 |
5ad0fef17bea73388d6c248a657723e0
|
|
| BLAKE2b-256 |
d98500d422ca98ab89eb5b7e69abc756179444d61bf0039b325160810e41df33
|
Provenance
The following attestation bundles were made for django_keycloak_oidc-0.3.255-py3-none-any.whl:
Publisher:
publish.yml on karnameh-tech/django-keycloak-oidc
-
Statement:
-
Statement type:
https://in-toto.io/Statement/v1 -
Predicate type:
https://docs.pypi.org/attestations/publish/v1 -
Subject name:
django_keycloak_oidc-0.3.255-py3-none-any.whl -
Subject digest:
937888c896be1cb1b6c3ad92373c64b9e182a1ae175ab3236b6c199e192dbad6 - Sigstore transparency entry: 793248998
- Sigstore integration time:
-
Permalink:
karnameh-tech/django-keycloak-oidc@f63fd8c4f42031af183b83cf5b6d801e23ae9dff -
Branch / Tag:
refs/heads/main - Owner: https://github.com/karnameh-tech
-
Access:
public
-
Token Issuer:
https://token.actions.githubusercontent.com -
Runner Environment:
github-hosted -
Publication workflow:
publish.yml@f63fd8c4f42031af183b83cf5b6d801e23ae9dff -
Trigger Event:
workflow_dispatch
-
Statement type: