A simple CLI tool for encrypting/hashing files and strings.
Project description


____ ____ _
| _ \ | _ \ | | 🌍: https://icodexys.net
| | | || |_) |_ | | 🛠️: https://github.com/jheffat/DPJ
| |_| || __/| |_| | 📊: 3.5.2 (05/04/2025)
|____/ |_| \___/
**DATA PROTECTION JHEFF**, a Cryptographic Software.
🔐 DPJ - CLI Data Cryptographic Tool
DPJ is a command-line data encryption tool, an improvement of Fixor 2.50(Discontinued). The Name Fixor changed to DPJ in honor of the my first encryption tool developed in QBasic and Visual Basic (2003–2007), DPJ is faster, more secure, and packed with new features designed to keep your data safe. Is a lightweight CLI tool, encrypt/decrypt files securely using custom-built methods. Good tool to encrypt your work projects or your sensitive data(documents, PDFs, photos, videos, etc.). -->✨ Changelog
🧾 Features
- 🔒 Fast Encrypt & Decrypt Files, using custom-built encryption.
- ⚡ IV Support, Uses a cryptographically secure IV to ensure ciphertext uniqueness, even with the same key and plaintext.
- 🧠 Choose or Autogenerate Passphrase, for encryption
- 🚫 No Overwrites, a file will not be altered if the provided passphrase is incorrect. DPJ detects if a file is encrypted and prevents redundant encryption.
- 🔐 KDF Support, Passphrases are transformed via a
Key Derivation Functionbefore use, making brute-force attempts extremely difficult. - 🧂 Secure Password Hashing, stored in encrypted metadata
- 🧬 Encrypted Metadata with AES, Used to protect internal config
- 🔍 File Scan Mode, to check encryption details
- ✅ Integrity Check Passed, A SHA-256-based verification step checks whether the decrypted data matches the original, ensuring the decryption process was successful.
- 🛡️ HMAC Support, A SHA-256-based HMAC is generated during encryption and verified during decryption to detect tampering or corruption.
- #️⃣ Hash tools included, Hash files/Msg using any theses algorithms (blake2b, sha3_512, sha256, sha1, sha512, shake_128, shake_256, sha3_256, blake2s, md5), In the absence of a specified algorithm, the default SHA256 will be applied.
☠️Please Note!
Im using a custom-built encryption, is multilayer linear transformation(See more in CHANGELOG.MD). For now Im rebuilding DPJ to be able to encrypt more secure with methods used in real world cryptographic like AES. The reason I building encryption from scratch(no modules ej:cryptographic.fernet) is to learning and get improve my problem-solving skill.
🚀 Performance
DPJ improves on Fixor with significantly faster encryption and decryption processes, optimized for modern systems and large files.
⚠️ Disclaimer
DPJ is a secure encryption tool intended for responsible use. By using this software, you acknowledge and accept the following:
-You are solely responsible for managing your passwords, keys, and encrypted data.
-If you lose or forget your passphrase, there is no way to recover your data. This is by design, as DPJ does not store or transmit any recovery information.
-The author(s) of DPJ are not liable for any data loss, damage, or consequences resulting from misuse, forgotten credentials, or failure to follow best security practices.
Use at your own risk.
🔧 Installation
You can install DPJ,
++by cloning this repo:
git clone https://github.com/jheffat/dpj.git
cd dpj
python3 -m pip install
++by using pypi pypi.org/dpj... or:
pip install dpj
++By download and install executable for:
*Windows
DPJ 3.0.7 Installer.exe (Need to setup your anti-virus to allow using this app)
*Linux Debian
DPJ_307LinuxDeb.deb (Link Dead**Fixing...)
sudo dpkg -i DPJ_307LinuxDeb.deb
🧪 Usage Examples
Encrypt all files including sub-directories with a key #R3ds0ftwar3!len3zz
dpj -e *.* -r -k #R3ds0ftwar3!len3zz
Encrypt all files with the extension .JPG on the current path c:\pictures
dpj -e c:\pictures\*.jpg
Decrypt all files including in sub-directories on the current local
dpj -d *.* -r
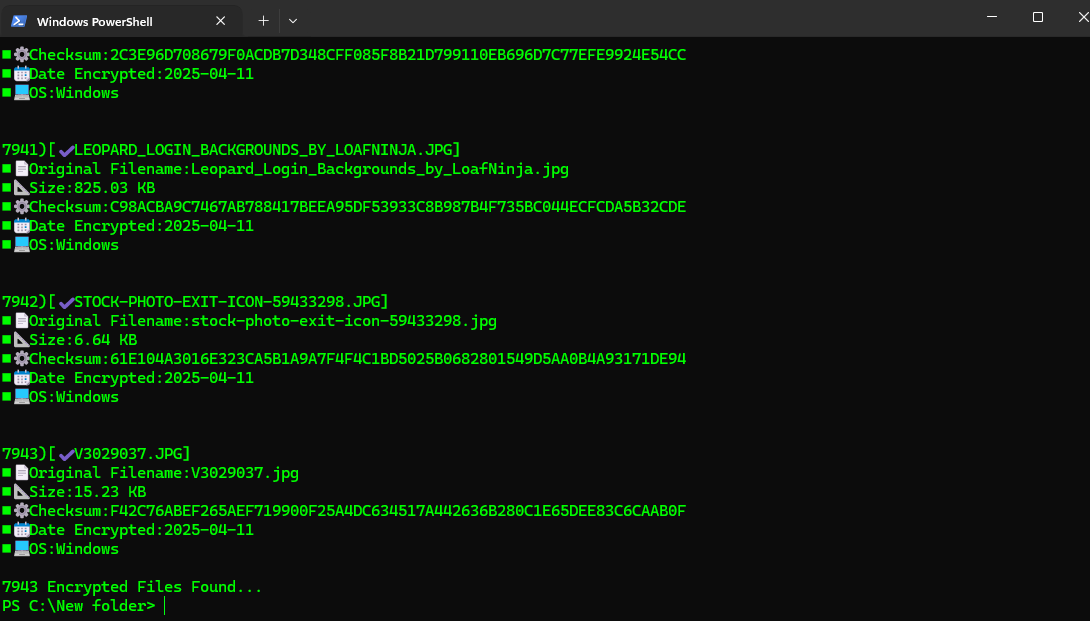
scan all files including in sub-directories on the current local
dpj -s *.* -r
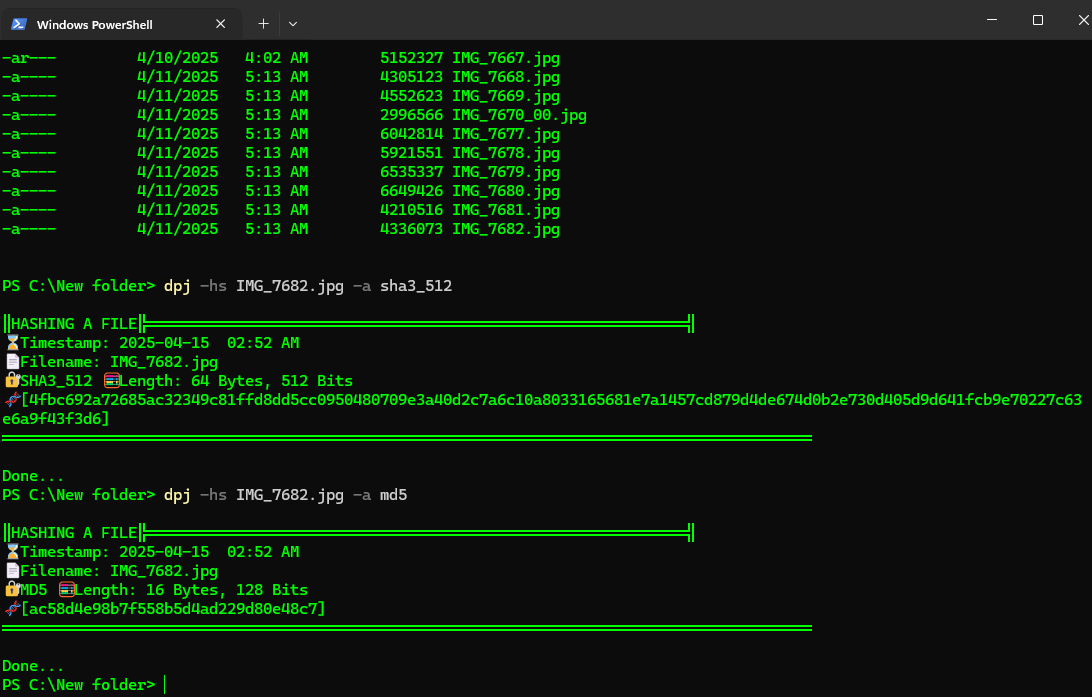
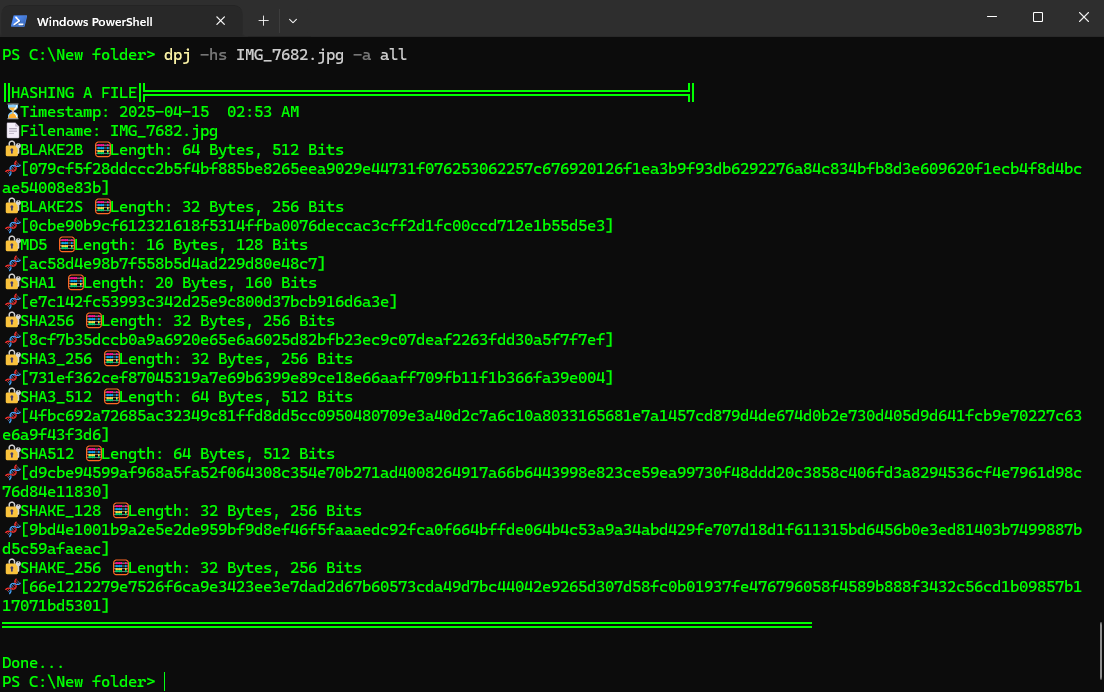
Hash all files using all algorithms
dpj -hs *.* -a all
Hash a text using md5
dpj -hs 'Life is Good' -a md5
📷 Screenshots
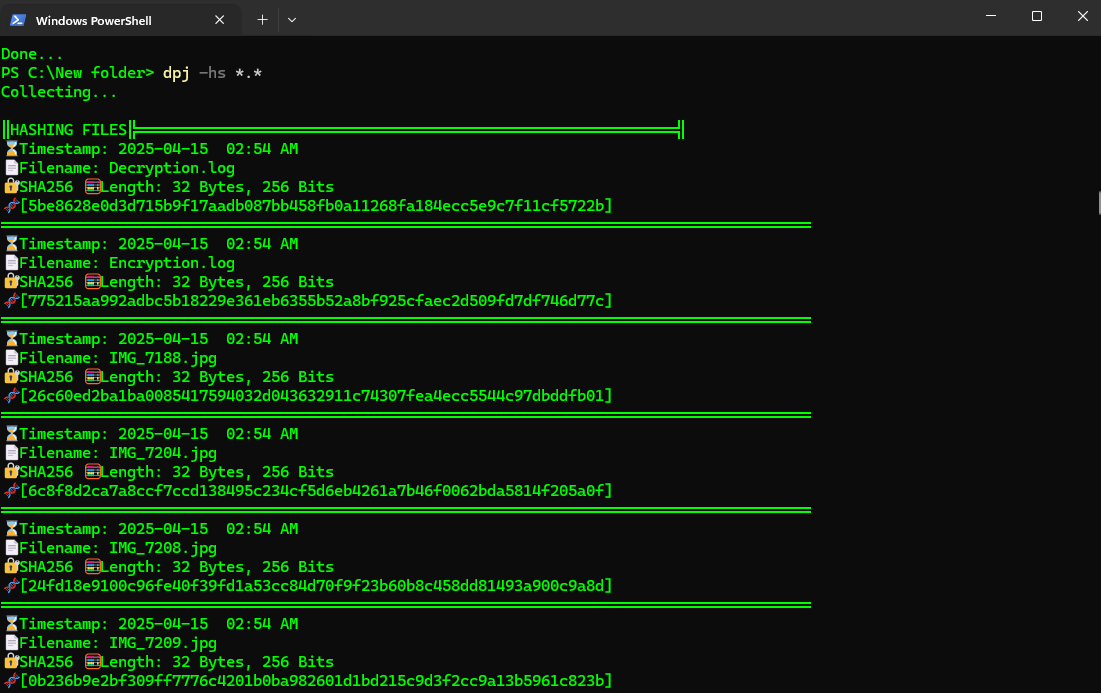
List of Files ready to be encrypted
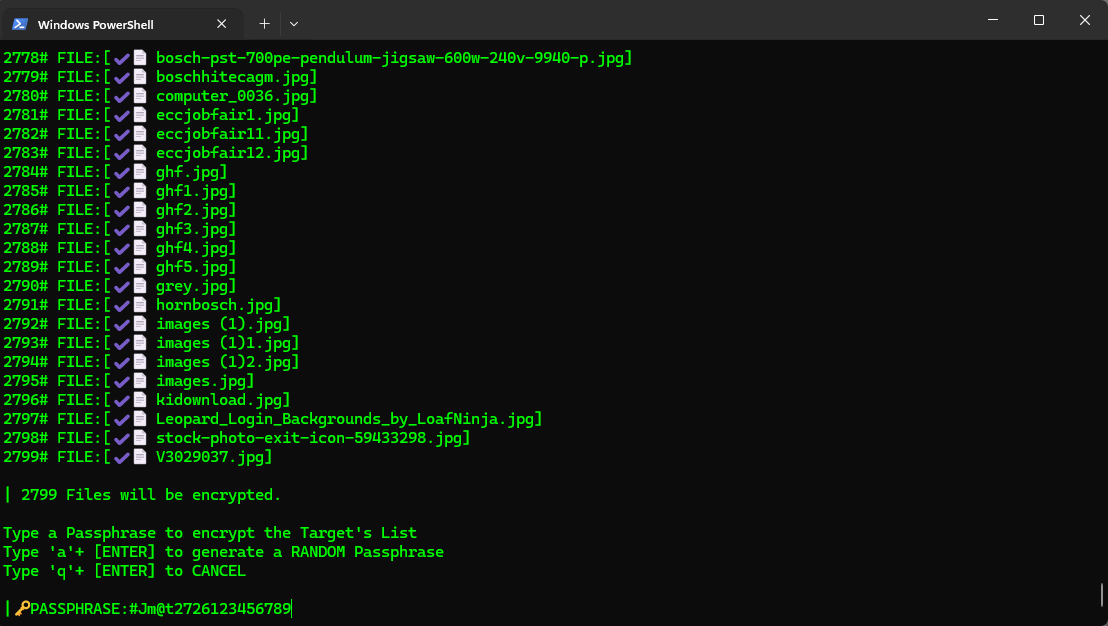
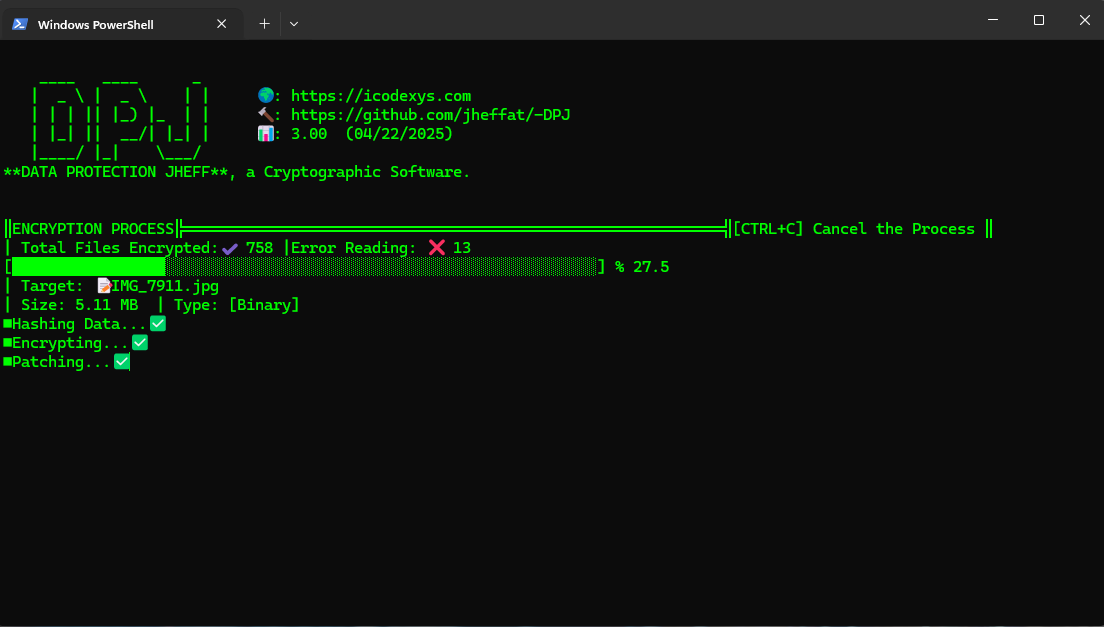
Encryption Process
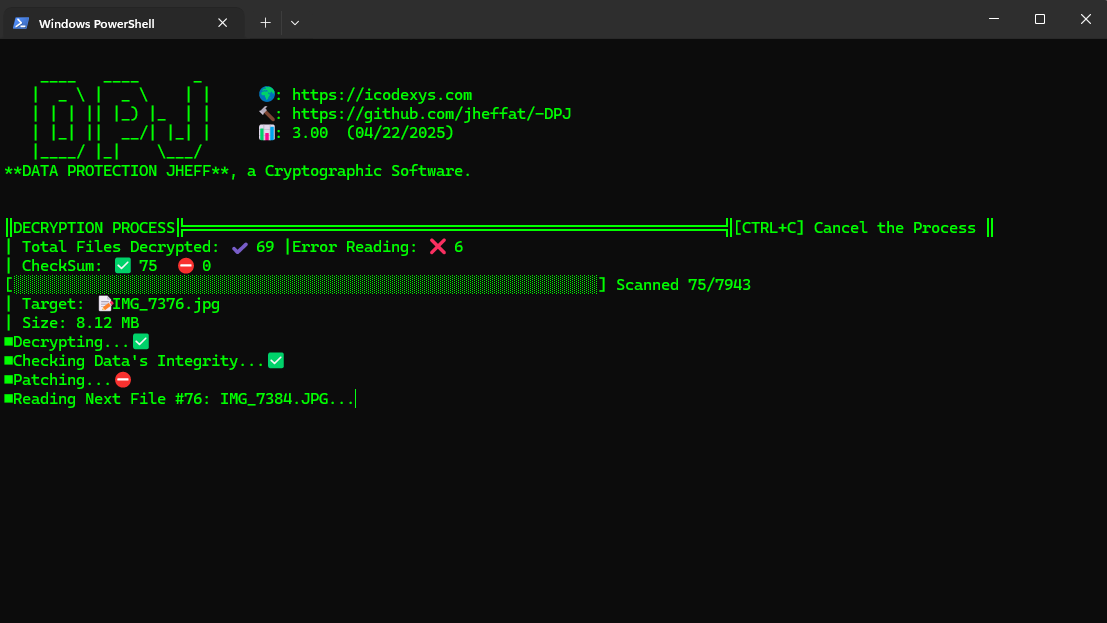
Decryption Process
Scanning files encrypted
Hashing a file
Hashing a file with all algorithms
Hashing all files using only the algorithm SHA256
📜 License
This project is licensed under the MIT License - see the LICENSE file for details.
🙌 Acknowledgements
DPJ(Data protection Jeff), was my first encryption app crafted in QBasic(CLI) and Visual Basic(GUI) between 2003–2007. This project is a modern revival with more power, speed, and security, thanks to the powerful language PYTHON.
Project details
Release history Release notifications | RSS feed
Download files
Download the file for your platform. If you're not sure which to choose, learn more about installing packages.
Source Distribution
Built Distribution
Filter files by name, interpreter, ABI, and platform.
If you're not sure about the file name format, learn more about wheel file names.
Copy a direct link to the current filters
File details
Details for the file dpj-3.5.2.tar.gz.
File metadata
- Download URL: dpj-3.5.2.tar.gz
- Upload date:
- Size: 22.9 kB
- Tags: Source
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/6.1.0 CPython/3.12.1
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
bd1ef4d2aba57eb1b20a90f5135fcd44dfc34d7e287f1df7ac07b74d3953afeb
|
|
| MD5 |
7087a9f9da36faa1a97c6936bd0c0812
|
|
| BLAKE2b-256 |
311796f2f57645b6697a982782094f573d9e014a14113583cbf147bfe6023ee3
|
File details
Details for the file dpj-3.5.2-py3-none-any.whl.
File metadata
- Download URL: dpj-3.5.2-py3-none-any.whl
- Upload date:
- Size: 15.6 kB
- Tags: Python 3
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/6.1.0 CPython/3.12.1
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
fad4972f2f7625431c233a9e598a276188920f7444d5c7a252198838918b0cb2
|
|
| MD5 |
6e68375c9228c1cb27f5faf65c19eb16
|
|
| BLAKE2b-256 |
4ed6f93e477218fc653f2b2c06e00d8463d99e0fa92757b1f529dedda8afa115
|