Fake traceroute generator using IP address spoofing
Project description
fakeroute
Fakeroute allows you to insert fake IPv4 and IPv6 hops between the last real hop and your Linux server by making use of IP address spoofing.
Setup
Install the package using pip install .. Run sudo fakeroute on the machine for
which you want to spoof the traceroute.
You can supply the path to a text file with custom IP addresses to be spoofed using --hops.
The file can contain IPv4 and IPv6 addresses, one per line.
To test the script, you can set up a virtual machine with a bridged network interface, such that it obtains its own IP via DHCP, and traceroute the IP of the host.
Most ISPs will not allow you to spoof IP addresses nowadays. You can still make use of fakeroute by externalizing the
spoofing process. To this end, start fakeroute with the --spoofer option, which expects IP:port to listen on, in a
data center that allows spoofing. Then, on the machine for which you want to fake the traceroute, supply fakeroute with
the remote endpoint (IP:port) of the spoofer using --remote. You can add an HMAC --key to not allow everyone to
use your spoofing service.
usage: fakeroute.py [-h] [--hops HOPS] [--remote REMOTE] [--spoofer SPOOFER] [--key KEY]
Fake traceroute generator
options:
-h, --help show this help message and exit
--hops HOPS Path to file containing IPv4 and IPv6 addresses
--remote REMOTE IP:port of remote spoofing service
--spoofer SPOOFER IP:port to launch a spoofing service locally
--key KEY HMAC-SHA256 signing key for remote spoofing authentication in hex format
How does it work?
IP packet headers contain a one byte time to live (TTL, IPv4) or hop limit (HL, IPv6) field which is supposed to be
decreased by every router on the packet's path to prevent infinite circulations.
Initially, the sender populates the packet with a sufficiently large value.
Most routers signal the expiry of the TTL by replying with an ICMP "TTL expired" packet to the packet sender.
Tracerouting works by sending out packets with increasing TTL.
The first router will drop the packet with TTL 1 and send an ICMP reply, the second router will drop the packet with TTL
2 and so on.
By simply dropping all packets with a TTL below a certain threshold N at the last hop, it will appear as if N hops, that
do not reply with ICMP packets, had been inserted.
The fakeroute.py script uses a raw socket to capture packets with low TTL and either relays them to a server in
a data center without egress filtering (i.e. where packets with spoofed source
IP address are not filtered) or generates ICMP replies for them from fake source IP addresses directly.
Where does it work?
Most providers will filter packets with forged IP addresses. An incomplete list of server providers without egress filtering is available here:
| Provider | Product | Date | Status |
|---|---|---|---|
| no longer working |
If you know more server providers, please submit a pull request with the details (provider name, product name, date, and, if possible, a CAIDA Spoofer report).
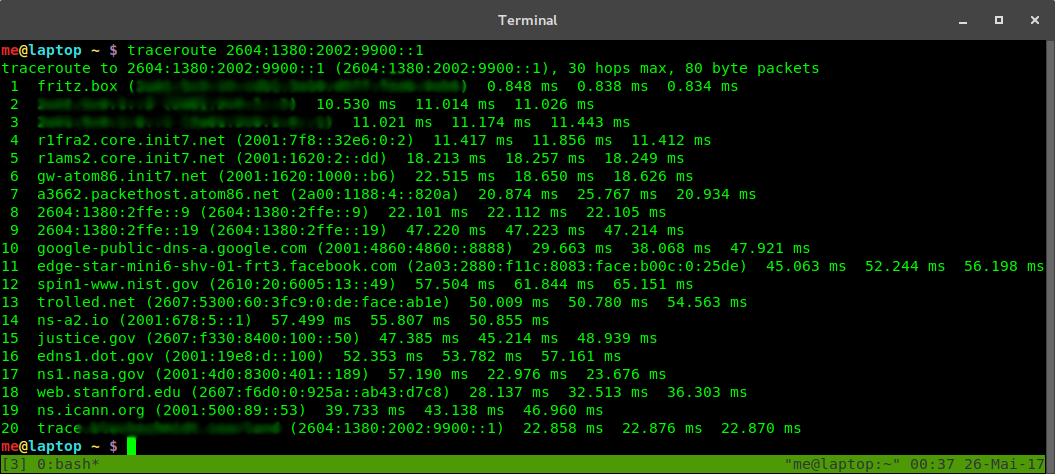
Screenshot
Project details
Release history Release notifications | RSS feed
Download files
Download the file for your platform. If you're not sure which to choose, learn more about installing packages.
Source Distribution
Built Distribution
Filter files by name, interpreter, ABI, and platform.
If you're not sure about the file name format, learn more about wheel file names.
Copy a direct link to the current filters
File details
Details for the file fakeroute-1.0.1.tar.gz.
File metadata
- Download URL: fakeroute-1.0.1.tar.gz
- Upload date:
- Size: 7.2 kB
- Tags: Source
- Uploaded using Trusted Publishing? Yes
- Uploaded via: twine/6.1.0 CPython/3.13.7
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
271d42d75880fced01b77870e4d9a0b3133169ef081d5032ea49b2019e8bfa20
|
|
| MD5 |
987657f5f1841b16d6106d0fcfe4bdcd
|
|
| BLAKE2b-256 |
afdf322dfe51027f20456dbe816968dbd430c30615745575cc7f50413a5f0206
|
Provenance
The following attestation bundles were made for fakeroute-1.0.1.tar.gz:
Publisher:
publish.yml on blechschmidt/fakeroute
-
Statement:
-
Statement type:
https://in-toto.io/Statement/v1 -
Predicate type:
https://docs.pypi.org/attestations/publish/v1 -
Subject name:
fakeroute-1.0.1.tar.gz -
Subject digest:
271d42d75880fced01b77870e4d9a0b3133169ef081d5032ea49b2019e8bfa20 - Sigstore transparency entry: 1186496133
- Sigstore integration time:
-
Permalink:
blechschmidt/fakeroute@ad5a41d11d1258a51b8a40c03441fef295df1a7e -
Branch / Tag:
refs/tags/v1.0.1 - Owner: https://github.com/blechschmidt
-
Access:
public
-
Token Issuer:
https://token.actions.githubusercontent.com -
Runner Environment:
github-hosted -
Publication workflow:
publish.yml@ad5a41d11d1258a51b8a40c03441fef295df1a7e -
Trigger Event:
push
-
Statement type:
File details
Details for the file fakeroute-1.0.1-py3-none-any.whl.
File metadata
- Download URL: fakeroute-1.0.1-py3-none-any.whl
- Upload date:
- Size: 7.7 kB
- Tags: Python 3
- Uploaded using Trusted Publishing? Yes
- Uploaded via: twine/6.1.0 CPython/3.13.7
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
ed5190b8861223a7cd4020d8502ce584f3d772369e798da36dfda1fa04237274
|
|
| MD5 |
1c54970652603c4245f80d53d0292ee7
|
|
| BLAKE2b-256 |
dffa7a68abf24bb6372513fc739952e875bc145f4fa0aeea165a59b6bbd663c8
|
Provenance
The following attestation bundles were made for fakeroute-1.0.1-py3-none-any.whl:
Publisher:
publish.yml on blechschmidt/fakeroute
-
Statement:
-
Statement type:
https://in-toto.io/Statement/v1 -
Predicate type:
https://docs.pypi.org/attestations/publish/v1 -
Subject name:
fakeroute-1.0.1-py3-none-any.whl -
Subject digest:
ed5190b8861223a7cd4020d8502ce584f3d772369e798da36dfda1fa04237274 - Sigstore transparency entry: 1186496136
- Sigstore integration time:
-
Permalink:
blechschmidt/fakeroute@ad5a41d11d1258a51b8a40c03441fef295df1a7e -
Branch / Tag:
refs/tags/v1.0.1 - Owner: https://github.com/blechschmidt
-
Access:
public
-
Token Issuer:
https://token.actions.githubusercontent.com -
Runner Environment:
github-hosted -
Publication workflow:
publish.yml@ad5a41d11d1258a51b8a40c03441fef295df1a7e -
Trigger Event:
push
-
Statement type: