A hackable Model Context Protocol (MCP) gateway
Project description
Gatekit
A hackable MCP gateway.
Gatekit is a Model Context Protocol gateway that controls traffic between your LLM and MCP tools for better visibility, security, and control.
It ships with plugins for tool management, content security, audit logging, and token usage tracking. Supports both local stdio servers and remote HTTP/SSE servers.
Need custom behavior? Extend with plugins, not forks. Your customizations stay separate, so you can keep getting Gatekit updates without merge conflicts.
Built-in plugins handle:
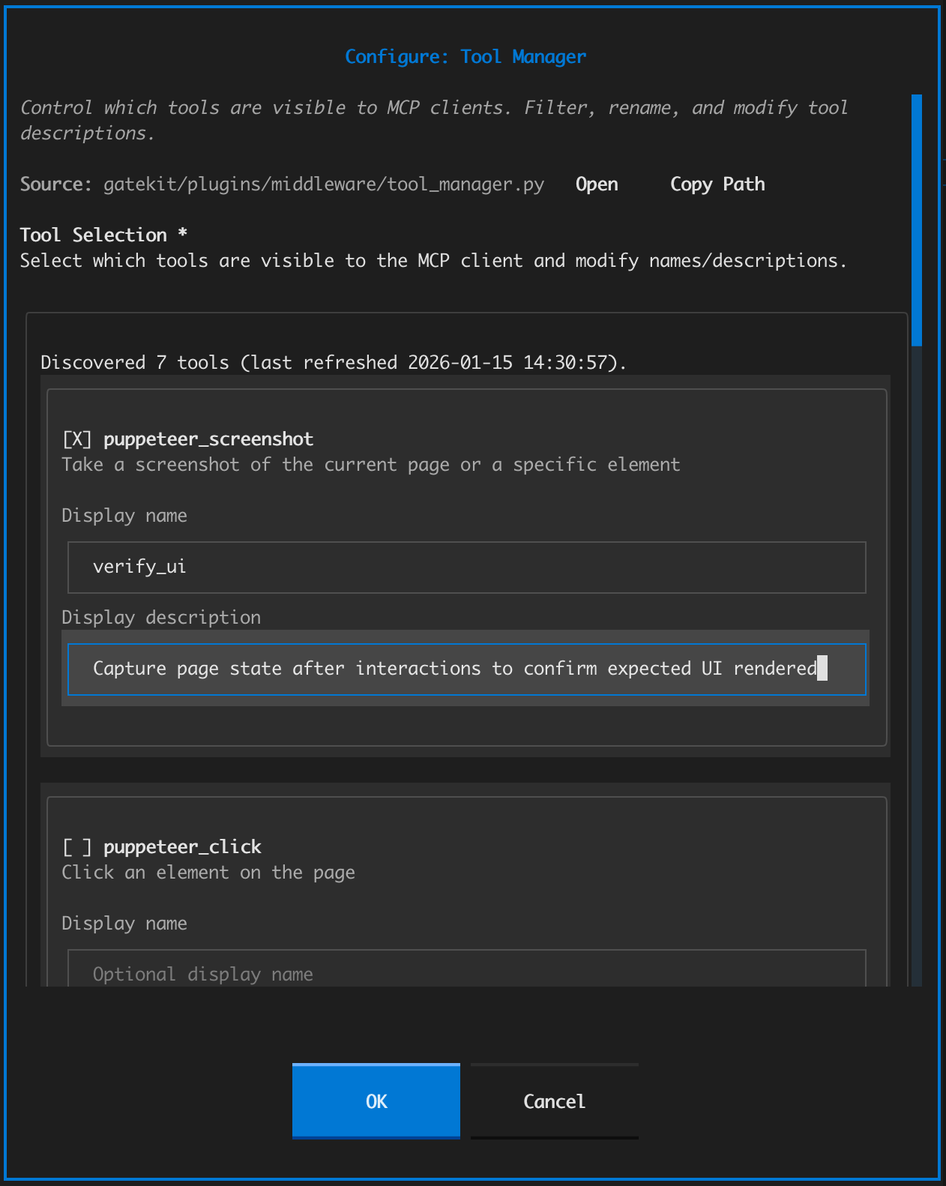
- Tool management — expose only the tools you want, rename and modify descriptions for cleaner context and better discoverability
- Content security — catch PII and secrets before they leave your machine, defend against basic prompt injection attacks (regex-based)
- Audit logging — debug failures, track usage, inspect full request and response bodies
- Token usage tracking — estimate token consumption per server and tool, with CSV export
- Stdio server sandboxing — restrict what local MCP servers can access on your machine using OS-native isolation (macOS Seatbelt, Linux bubblewrap)
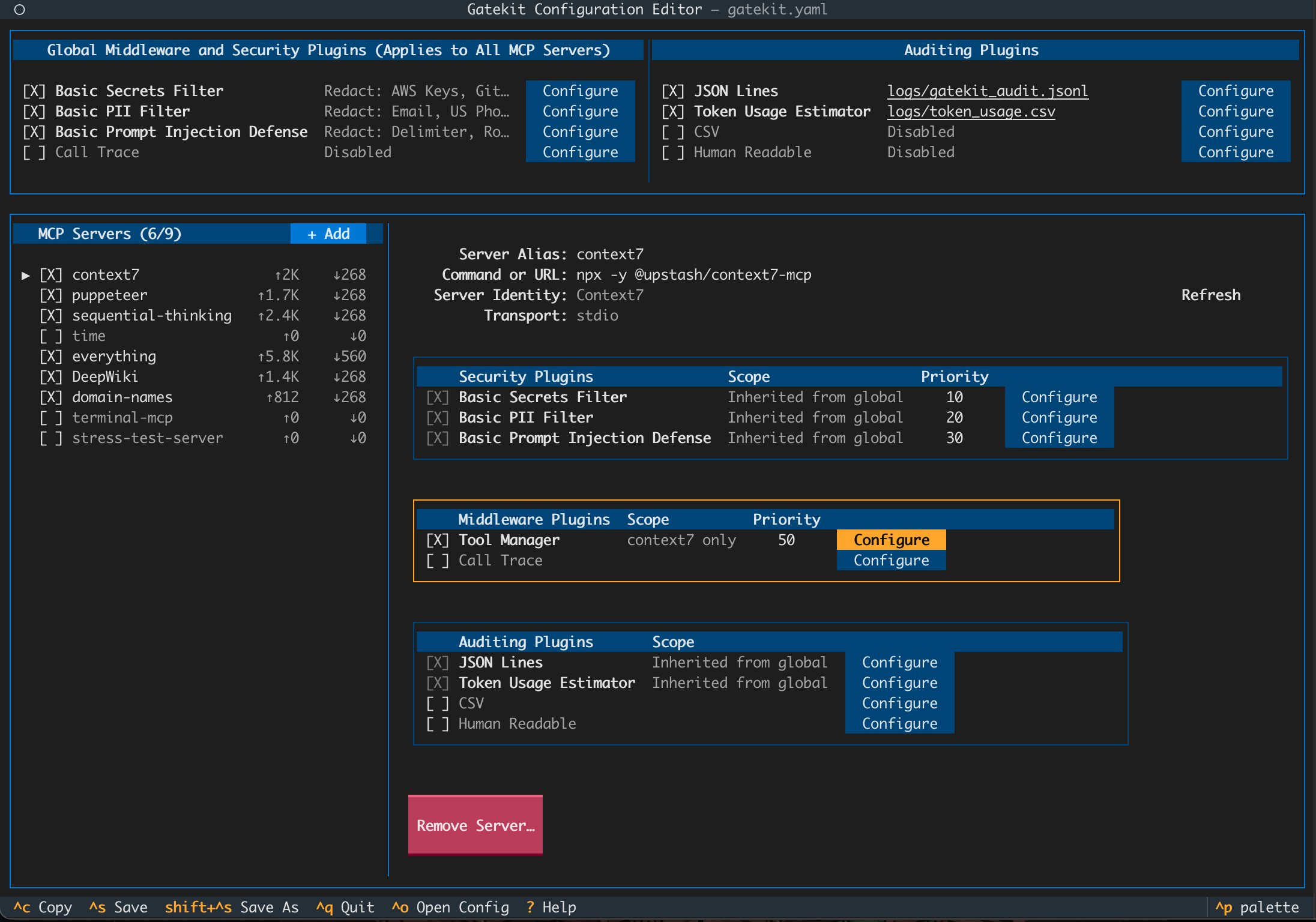
Gatekit configuration editor (Terminal UI)
Quick Start
Installation
# With uv (recommended)
uv tool install gatekit
# With pipx
pipx install gatekit
# With pip (in a virtual environment)
pip install gatekit
Requires Python 3.10+. Works on macOS, Linux, and Windows.
Usage
gatekit
Guided Setup
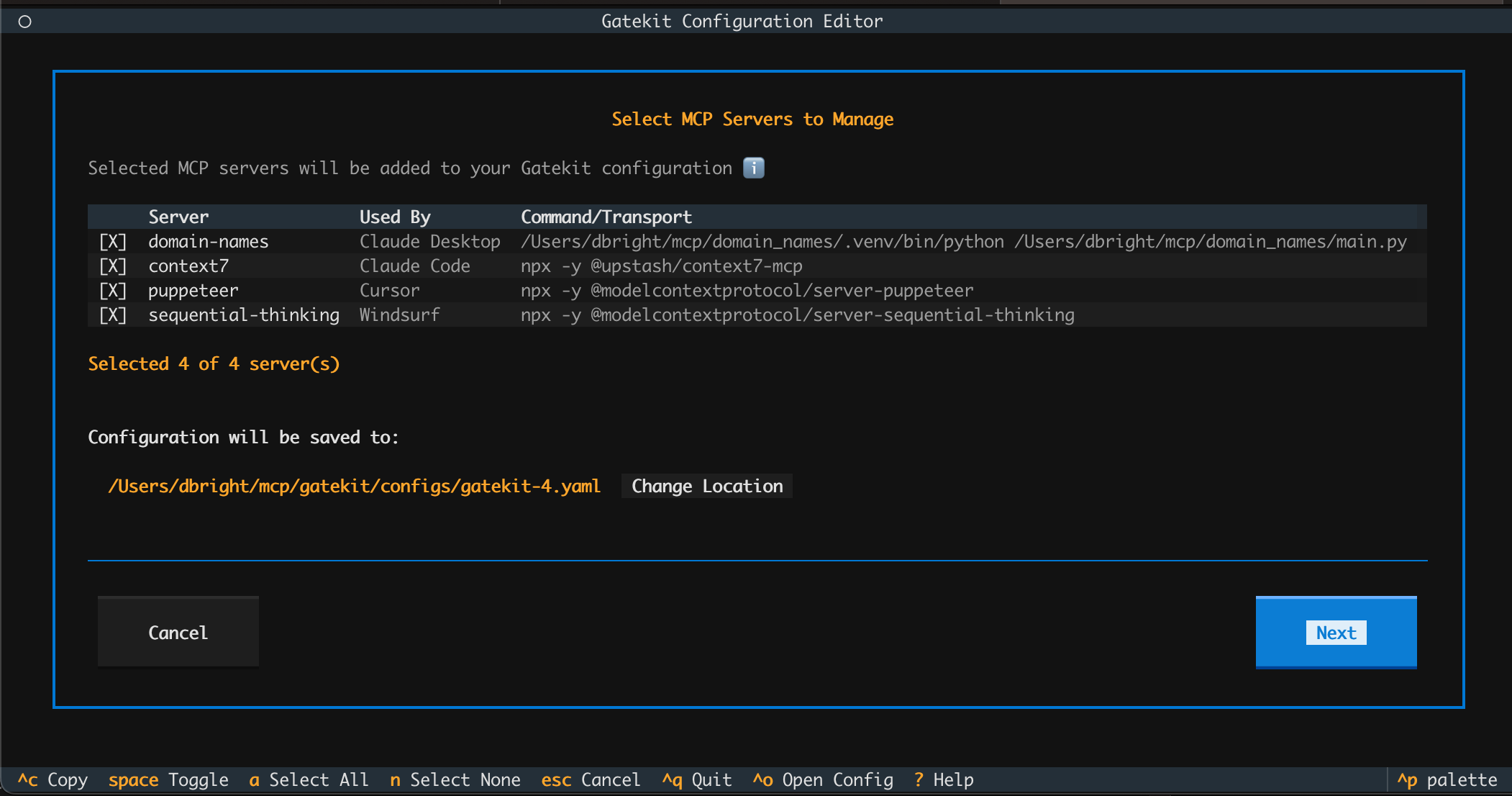
The TUI includes a guided setup wizard that:
- Auto-detects MCP clients on your system (Claude Desktop, Codex, Claude Code, Cursor, Windsurf)
- Discovers all configured MCP servers from each client
- Generates a complete Gatekit configuration
- Provides client-specific setup instructions with copy buttons
- Creates restore scripts in case you want to revert
Manual Configuration
For MCP clients not detected by Guided Setup, configure Gatekit as an MCP server with command and args:
{
"servers": {
"gatekit": {
"command": "gatekit-gateway",
"args": ["--config", "/absolute/path/to/gatekit.yaml"]
}
}
}
Example for VS Code (.vscode/mcp.json):
{
"servers": {
"gatekit": {
"command": "gatekit-gateway",
"args": ["--config", "${userHome}/.config/gatekit/gatekit.yaml"]
}
}
}
How It Works
Gatekit proxies traffic between Model Context Protocol (MCP) clients and servers. Config files define which servers to proxy and which plugins to run.
┌─────────────┐ ┌───────────────────┐ ┌─────────────────┐
│ MCP Client │ │ gatekit-gateway │ │ MCP Server(s) │
│ (Claude, │─────────────▶│ │─────────────▶│ (filesystem, │
│ Cursor) │◀─────────────│ plugins │◀─────────────│ github, etc.) │
└─────────────┘ └───────────────────┘ └─────────────────┘
▲
│ configures
│
┌─────────┴────────┐ ┌─────────────┐
│ gatekit.yaml │ writes │ gatekit │
│ │◀─────────────│ (TUI) │
│ • mcp servers │ └─────────────┘
│ • security │
│ • auditing │
│ • middleware │
└──────────────────┘
gatekit- The TUI. Detects your MCP clients, discovers servers, and generates YAML config files.gatekit.yaml- Your config. Defines upstream servers and plugins.gatekit-gateway- The runtime. Your MCP client points here. Applies your plugins to all traffic.
Plugins intercept traffic between client and servers, allowing you to modify, block, or log messages:
- Security - Block or redact sensitive content (PII, secrets)
- Middleware - Transform requests/responses (filter tools, rename, modify)
- Auditing - Log all MCP traffic for debugging or compliance
Built-in Plugins
Middleware
- Tool Manager - Filter, rename, and customize tool descriptions
- Call Trace - Append diagnostic info to tool responses
Security
- PII Filter - Detect and redact personally identifiable information (regex-based)
- Secrets Filter - Detect API keys, tokens, and other secrets (regex-based)
- Prompt Injection Filter - Detect common prompt injection patterns (regex-based basic protection)
Auditing
- JSON Lines - Structured logs for processing
- CSV - Spreadsheet-compatible logs
- Human Readable - Plain text logs for quick review
- Token Usage Estimator - Track token consumption per server and tool, with live TUI display and CSV export
Custom Plugins
When the built-in plugins aren't enough, write your own. Plugins intercept and modify tool calls and responses, enabling:
- Pruning responses to avoid context bloat
- Injecting credentials into tool calls without exposing them to the LLM
- Joining additional information from other data sources
- Human-in-the-loop approval for dangerous actions
- Response caching and deduplication
from gatekit.plugins.interfaces import MiddlewarePlugin, PluginResult
class MyPlugin(MiddlewarePlugin):
async def process_request(self, request, server_name):
# Your logic here
return PluginResult()
async def process_response(self, request, response, server_name):
# Your logic here
return PluginResult()
HANDLERS = {"my_plugin": MyPlugin}
See the plugin development guide for details.
Documentation
- Full Documentation - Guides, tutorials, and reference
- Getting Started - Installation, quick start, and tutorials
- Configuration Specification
- Plugin Development Guide
- Security Model
Roadmap and Limitations
Security plugins use regex-based pattern matching, not production-grade ML/NLP.
Planned features include:
- Enhanced detection - Support for best-in-class third-party security and privacy solutions like Microsoft Presidio, Yelp Secrets, etc.
- Response pruning - Built-in response trimming functionality to help reduce context bloat
Feedback
Have feedback on the roadmap? Join the discussion. Found a bug? Open an issue. For anything else: dbright@gatekit.ai
License
Apache License 2.0 - see LICENSE
Gatekit v0.3.0 - A hackable MCP gateway
Project details
Release history Release notifications | RSS feed
Download files
Download the file for your platform. If you're not sure which to choose, learn more about installing packages.
Source Distribution
Built Distribution
Filter files by name, interpreter, ABI, and platform.
If you're not sure about the file name format, learn more about wheel file names.
Copy a direct link to the current filters
File details
Details for the file gatekit-0.3.0.tar.gz.
File metadata
- Download URL: gatekit-0.3.0.tar.gz
- Upload date:
- Size: 26.9 MB
- Tags: Source
- Uploaded using Trusted Publishing? No
- Uploaded via: uv/0.7.21
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
8311a20371d20009efde7cd965c24fb6b34ebecd3c240e424d64c6dec8f32ae8
|
|
| MD5 |
3af31ea4fdad6e78c53998ed9dc33375
|
|
| BLAKE2b-256 |
7401706a31d6451ad73ffa5b1150ddc8d9c5ebd2f197eed379536b0c7d8058f4
|
File details
Details for the file gatekit-0.3.0-py3-none-any.whl.
File metadata
- Download URL: gatekit-0.3.0-py3-none-any.whl
- Upload date:
- Size: 497.4 kB
- Tags: Python 3
- Uploaded using Trusted Publishing? No
- Uploaded via: uv/0.7.21
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
c180f80f587f5811a0501646c5bec7d34e04bcc741a00f727b7deaa3ac668ab4
|
|
| MD5 |
836a2f2e10b5252175081c6dfa261541
|
|
| BLAKE2b-256 |
69466e7ff633e0b1e368b70b0cdbca76cde39e5180a402d9349540bbb22ffad4
|















