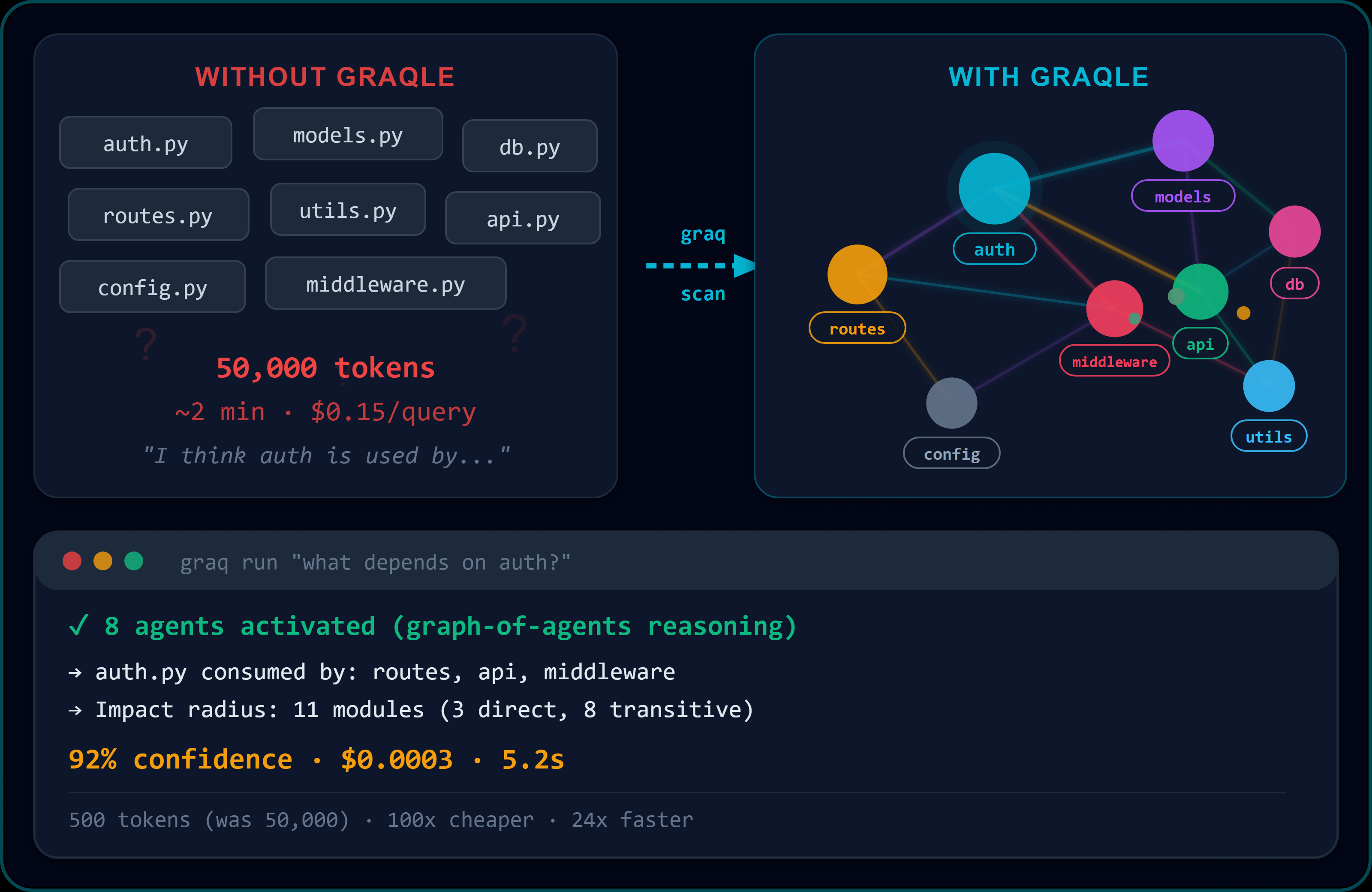
Give your AI tools architecture-aware reasoning. Build a knowledge graph from any codebase — dependency analysis, impact analysis, governed AI answers with confidence scores. Works with Claude Code, Cursor, VS Code Copilot. 14 LLM backends, fully offline capable.
Project description
Your codebase is a graph. Every node reasons. Every change is governed.
One command. 90 seconds. Your AI writes code with architectural awareness, governance gates, and multi-agent reasoning. Not a linter. Not a copilot. A knowledge graph where every module is an autonomous agent — now with a structured chat layer that picks the right tool for every task.
The world's first governance-led multi-agent reasoning system for code. Scan any codebase into a persistent knowledge graph. Every module becomes a reasoning agent. Multiple agents decompose, debate, and synthesize answers with clearance-level governance. Every change is impact-analysed, gate-checked, and taught back — automatically.
"AI assistants see files. GraQle sees architecture. That's why it catches the bugs they can't."
pip install graqle && graq scan repo . && graq run "find every security bug in this codebase"
Website · VS Code Extension · Dashboard · PyPI · Changelog
Governance Gate — Activate Full GraQle Autonomy
Optional. One command. Fully reversible. Turn any Claude Code session into a governed, architecture-aware reasoning pipeline.
pip install graqle
graq gate-install
That's it. Claude Code now routes every tool call through GraQle's governed equivalents — impact analysis, preflight checks, lesson memory, and architectural reasoning activate automatically. No workflow change. No configuration. Just governance.
- What it does: Installs
.claude/hooks/graqle-gate.pyand.claude/settings.jsonin your project - What changes: Claude Code's native tools (Read, Write, Edit, Bash) are routed through GraQle's graph-aware equivalents (
graq_read,graq_edit,graq_generate,graq_bash) - Why: Every file read gets architectural context. Every edit gets preflight governance. Every change gets impact analysis. Your AI stops guessing and starts knowing.
- Reversible: Delete
.claude/hooks/graqle-gate.pyto disable. Your project is unchanged.
Works with the free tier. No signup required. No API key needed if you use Ollama (fully local).
Learn more about Governance Gate · VS Code Extension
What's New in v0.50.0 — Structured Chat Agent
Your AI coding assistant now runs a structured chat loop with architectural awareness, durable pause/resume, and governed tool selection. The same quality you get from dedicated coding assistants — now inside any MCP client.
Structured chat agent layer
- Smart tool selection — the assistant picks the right tool for the job based on what your project already uses, your past successful workflows, and the specific intent of your question. No more cold-picking from a long tool list.
- Durable pause/resume — long-running tasks can pause for your approval and resume exactly where they left off. No lost work if you close the session.
- Structured second-opinion check — for sensitive actions, the assistant runs a quick internal check before touching anything, flagging safety concerns, missing prerequisites, or ambiguity.
- Bring-your-own-backend — mix and match LLM providers for different task types (triage, reasoning, formatting). Works with a single backend or multiple families.
- Hard-error continuation — when a tool fails, the assistant adapts and keeps going instead of freezing.
- Convention inference — when you say "write an ADR for this" or "add a test for that", the assistant finds existing examples in your project, matches the style, and writes in the right location — no clarifying questions.
Three new SDK capabilities
- Session-scoped permissions — approve a tool once for a scope, subsequent same-scope calls auto-proceed. Revocable mid-session.
- Append-only audit log — every turn is recorded at
.graqle/chat/ledger/turn_<id>.jsonlfor full historical transcript inspection. - Project-specific instructions — drop a
GRAQ.mdat your project root to customize how the assistant behaves for your codebase, similar toCLAUDE.md.
Governed by default
- Three-tier governance (auto / review / approval) with tiers pre-disclosed upfront — no surprise-blocks mid-flow
- Impact analysis and preflight checks on every change
- Destructive operations always require explicit confirmation
Three critical bug fixes rolled in
- Backend reliability — fixes a crash that affected reasoning calls after the first round on some backends
- Long-response handling — synthesis now correctly handles responses that hit the model's output token limit
- Batch reasoning — the batch reasoning path now works correctly when a query fails inside a batch
Key numbers
- 136 MCP tools exposed to Claude Code, Cursor, and VS Code Copilot
- 14 LLM backends — Anthropic, OpenAI, AWS Bedrock, Ollama (local), Gemini, Groq, DeepSeek, Together, Mistral, OpenRouter, Fireworks, Cohere, vLLM, and custom providers
- Fully offline capable with Ollama
Install VS Code Extension | Full Changelog
Why GraQle is different from everything else
| AI Assistants (Copilot, Cursor, Claude Code) | GraQle |
|---|---|
| See one file at a time | Sees the entire architecture as a graph |
| Generate code, hope it works | Generate, validate, self-correct, then write |
| No memory between sessions | Persistent knowledge graph that learns and grows |
| No governance on output | Every answer passes governance gates |
| Single model, single perspective | Multi-agent reasoning: decompose, debate, synthesize |
| Can't tell you what a change breaks | Impact analysis across the full dependency graph |
The problem with AI coding at scale
Copilot writes auth logic. Cursor generates your API layer. Claude Code refactors your service layer. All of it ships fast. None of it is checked at the architectural level.
Bugs don't live in files. They live between files.
In a 6-file dental appointment system we built as a demo, every single tool — pylint, mypy, flake8, Copilot — missed 4 of the 8 bugs. Because those bugs only exist in the relationship between files:
app.pyassumedservices.pychecks auth on the cancel endpointservices.pyassumedapp.pyalready checked it- Neither did
- Any unauthenticated HTTP client could cancel any patient's appointment
That is a HIPAA violation. That is what vibe coding at scale produces. That is what Graqle catches.
The 90-second proof
# 1. Scan any codebase into a knowledge graph
graq scan repo .
# → 5,579 nodes, 19,916 edges — full architecture mapped in seconds
# 2. Ask Graqle to audit it
graq run "find every security vulnerability in this codebase"
# → Graph-of-agents activates across 50 nodes
# → Traces cross-file attack chain: MD5 (models.py) → expired tokens
# never checked (auth.py) → cancel endpoint with zero auth (app.py)
# → Confidence: 89% | Evidence: 3-file chain | Cost: ~$0.001
# 3. Fix it — Graqle shows exact before/after for each file
# 4. Teach it back — the graph never forgets
graq learn "cancel endpoint must always require auth token"
# → Lesson persists. Every future audit knows this rule.
# → Copilot forgot. Graqle remembered.
Dental audit results (live, AWS Bedrock, 2026-03-28):
| Metric | Result |
|---|---|
| Files scanned | 6 (410 lines) |
| Bugs found | 8 (2 CRITICAL, 3 HIGH, 3 MEDIUM) |
| Cross-file bugs (invisible to linters) | 4 |
| Reasoning confidence | 89–90% |
| Fixes applied | 8/8 |
| Verification checks | 12/12 PASSED |
| Total cost | ~$0.001 |
What makes Graqle structurally different
Every other AI tool works at the file level. Graqle works at the relationship level.
The graph IS the reasoning architectureEvery node is simultaneously a knowledge entity AND a reasoning agent. The graph topology determines who reasons. Edge weights encode what was learned. Ontological constraints govern what reasoning is permitted. Results mutate the same graph that governs future reasoning. This is a closed developmental loop. No stateless tool can replicate it without rebuilding the entire persistent typed graph layer from scratch. |
Cross-file bugs. Found automatically.The assumption gap between |
Persistent architectural memorygraq learn "auth must be in services layer"
# Written to graph as weighted LESSON edge
# Survives git ops, session resets, team changes
# Every future audit activates this lesson
Lessons compound. The longer your team uses Graqle, the more it knows about your specific architecture, your specific past mistakes, your specific safety rules. That compounding is the moat. |
Governance gates before code is writtengraq preflight "refactor the auth layer"
# → 12 modules depend on auth
# → 3 have no tests
# → 2 past lessons activated
# → LESSON: cancel endpoint must require auth
# → Risk: HIGH — proceed with plan
The gate runs before a single line changes. Not a linter rule. The graph reasoning about the specific change in the context of your specific architecture. |
How it works
Your Code Knowledge Graph AI Reasoning
┌──────────────┐ ┌───────────────────┐ ┌──────────────────────┐
│ Python │ graq scan │ 13 node types │ query │ Graph-of-Agents │
│ TypeScript │ ─────────> │ 10 edge types │ ──────> │ PCST activation │
│ Config │ │ Weighted lessons │ │ Multi-round reasoning │
│ Docs / APIs │ │ Dependency chains │ │ Confidence-scored │
└──────────────┘ └───────────────────┘ │ Audit-trailed │
│ └──────────────────────┘
graq learn / graq grow │
│ ▼
Graph evolves with every graq preflight / graq impact
interaction and lesson Gate every change before it ships
6-gate validation pipeline — every scanned node passes: parse integrity → completeness repair → chunk quality → edge deduplication → relationship inference → compilation verification. Hollow nodes are auto-repaired, never silently dropped.
Model agnostic. Works everywhere.
Graqle is not tied to any AI provider. The knowledge graph and reasoning architecture are completely decoupled from the backend. One line in graqle.yaml switches providers.
| Backend | Best For | Cost |
|---|---|---|
| Ollama | Fully offline, air-gapped, zero cost | $0 |
| AWS Bedrock | Enterprise IAM, your own account | AWS pricing |
| Anthropic | Deepest reasoning, Claude Opus | ~$0.001/q |
| OpenAI | Broad compatibility | ~$0.001/q |
| Groq | Sub-second responses | ~$0.0005/q |
| DeepSeek / Mistral / Gemini / Together / Fireworks / Cohere / OpenRouter / vLLM / Custom | Various | Various |
# graqle.yaml — smart task routing
model:
backend: bedrock
model: eu.anthropic.claude-sonnet-4-6
region: eu-north-1
routing:
rules:
- task: reason
provider: bedrock
model: eu.anthropic.claude-opus-4-6-v1
profile: your-aws-profile # uses your existing AWS credentials
- task: context
provider: groq # fast lookups on cheap model
Works with every AI IDE: Claude Code, Cursor, VS Code + Copilot, Windsurf, JetBrains — zero workflow change. Graqle adds 74 architecture-aware MCP tools your AI uses automatically.
What Graqle does that competitors cannot
| Copilot / Cursor | LangChain / CrewAI | LlamaIndex | Graqle | |
|---|---|---|---|---|
| Sees cross-file relationships | No | No | No | Yes — typed graph |
| Finds cross-file bugs | No | No | No | Yes — 4/8 dental bugs |
| Persistent architectural memory | No — resets | No — stateless | No — stateless | Yes — compounds |
| Blast radius before change | No | No | No | Yes — BFS traversal |
| Governance gate | No | Prompt rules | No | Yes — graph-enforced |
| Learns from every audit | No | No | No | Yes — edge weights |
| Works offline / air-gapped | No | No | No | Yes — Ollama |
| Self-improves over time | No | No | No | Yes — closed loop |
The structural reason competitors cannot copy this: They are stateless. Graqle's moat is a persistent typed knowledge graph where topology governs agent activation, ontological constraints bound reasoning, edge weights encode institutional memory, and results mutate the same structure that governs future cognition. You cannot replicate this with prompt engineering. You have to rebuild the entire layer.
Use cases
Auditing an existing production application
Point Graqle at any codebase. It scans in minutes. You get:
- Full blast radius for every file — what breaks if this changes
- Cross-file vulnerability chains traced across auth, business logic, data layers
- Architectural coupling violations and assumption gaps between modules
- Security issues: auth bypass, injection vectors, insecure crypto, data exposure
- All findings with confidence scores and file-level evidence
No prior knowledge of the codebase required. The graph maps it for you.
graq scan repo .
graq run "find every security vulnerability"
graq run "what are the highest-risk files to change?"
graq impact auth.py # blast radius: what breaks if auth changes
Building a new application with AI
Every function you add gets mapped to the graph immediately. Before writing the next function, run preflight: the graph tells you what this will affect, whether something similar already exists, whether this introduces a circular dependency.
graq preflight "add payment processing to checkout service"
# → 6 modules will be affected
# → LESSON: payment module must never call user service directly
# → Similar function exists in billing.py — consider reusing
You build with architectural awareness that accumulates as you build. By the time you ship, the graph is a complete living specification.
Maintaining a legacy codebase
Legacy systems are where Graqle is most valuable. No single developer has the full picture. Assumptions are buried across dozens of files. A change to one module silently breaks five others.
The graph maps hidden dependencies explicitly. A new engineer gets full architectural context for any module in seconds. A senior engineer validates that a refactor is safe before touching a single line.
graq context legacy_payments.py # 500-token focused context
graq impact legacy_payments.py # what depends on this
graq lessons payment # what went wrong here before
CI/CD governance gate
Every PR runs graq preflight. The gate produces a confidence score. Below threshold: blocked.
# .github/workflows/graqle-gate.yml
- name: Graqle governance gate
run: |
graq predict "$(git diff HEAD~1 --stat | head -20)" \
--confidence-threshold 0.80 \
--fail-below-threshold
Architecture-aware quality control that scales across teams without requiring every reviewer to understand every subsystem.
PR Guardian — governance checks on every pull request
Automated blast radius analysis for PRs. PR Guardian analyses your diff against the project knowledge graph and reports blast radius, a governance verdict, and a status badge — directly on the PR.
GitHub Action
# .github/workflows/graq-guardian.yml
name: PR Guardian
on: [pull_request]
permissions:
contents: read
pull-requests: write
jobs:
guardian:
runs-on: ubuntu-latest
steps:
- uses: actions/checkout@v4
with:
fetch-depth: 0
- uses: graqle/pr-guardian@v1
with:
github-token: ${{ secrets.GITHUB_TOKEN }}
CLI
# Analyse a diff locally
graq pr-guardian --diff <(git diff main...HEAD)
# JSON output for CI integration
graq pr-guardian --diff <(git diff main...HEAD) --output-format json
What it shows
- Blast radius — how many downstream modules are affected by the change
- Governance verdict — pass or block, with actionable reasoning
- PR badge — shields.io-compatible SVG posted as a PR comment
- SARIF output — optional integration with GitHub Code Scanning
PR Guardian runs the same analysis locally and in CI, so developers catch governance issues before review.
75 MCP tools — your AI uses them automatically
graq init # Claude Code — auto-wires all 75 tools
graq init --ide cursor
graq init --ide vscode
graq init --ide windsurf
Core reasoning tools (free):
| Tool | What it does |
|---|---|
graq_reason |
Graph-of-agents reasoning — 50 nodes, multi-round, confidence-scored |
graq_impact |
Blast radius — BFS traversal through dependency graph |
graq_preflight |
Pre-change gate — lessons + safety boundaries + risk level |
graq_context |
500-token focused context for any module |
graq_learn |
Teach the graph — lesson persists across sessions and teams |
graq_lessons |
Surface relevant past mistakes for current query |
graq_predict |
Confidence-gated prediction — writes back if threshold met |
graq_gate |
Binary governance gate — PASS / FAIL with evidence |
graq_inspect |
Graph stats, node details, health status |
graq_auto |
Autonomous loop — plan, generate, write, test, fix, retry until GREEN |
SCORCH — UX audit engine (12 dimensions):
| Tool | What it does |
|---|---|
graq_scorch_audit |
Full 12-dimension UX friction audit with Claude Vision |
graq_scorch_behavioral |
12 behavioral UX tests — zero AI cost |
graq_scorch_security |
CSP, XSS, exposed API keys, auth flow |
graq_scorch_a11y |
WCAG 2.1 accessibility |
graq_scorch_perf |
Core Web Vitals |
graq_scorch_conversion |
CTA + trust signals |
graq_scorch_mobile |
Touch targets + viewport |
| + 5 more | seo, brand, i18n, diff, report |
Phantom — browser computer skills (8 tools):
| Tool | What it does |
|---|---|
graq_phantom_browse |
Open any URL, screenshot + full DOM summary |
graq_phantom_click |
Click elements by text, selector, or coordinates |
graq_phantom_type |
Type into forms, inputs, search boxes |
graq_phantom_audit |
Run 10 audit dimensions on any live page |
graq_phantom_flow |
Execute multi-step user journeys with assertions |
graq_phantom_discover |
Auto-crawl all pages from a starting URL |
graq_phantom_screenshot |
Capture + optional Claude Vision analysis |
graq_phantom_session |
Session + auth profile management |
graq_* tools have kogni_* aliases for backwards compatibility. All 75 tools, zero license checks.
Real results
Dental appointment system — 8 bugs in 90 seconds (live demo, 2026-03-28)
A 6-file, 410-line Flask dental appointment system. Bugs planted as a realistic "vibe coded" application would produce them.
What every standard tool missed:
- BUG-001 CRITICAL:
cancel()inapp.py— no auth. Traces throughapp.py → services.py. Neither file checks auth. Only visible as a relationship. - BUG-002 CRITICAL:
search()— unauthenticated. Empty query returns all patients. HIPAA violation. - BUG-005 HIGH: Double-booking not prevented.
services.pyassumesmodels.pychecks overlap.models.pyassumesservices.pydoes. Neither does. Only visible as a cross-file assumption gap. - BUG-006 MEDIUM:
notifications.pybypasses service layer entirely. Schema change inmodels.pysilently breaks it.
Graqle found all 8. 89–90% confidence. AWS Bedrock. 3 minutes.
17,418 nodes, 8 audits, $0.30
Three repos merged into one knowledge graph. 8 parallel SCORCH audits across the entire surface. Found a CTA button that was 20px tall (44px minimum for mobile touch targets). Fixed before a single prospect saw it.
Scale: 17,418 nodes | 70,545 edges | 8 audits | Total cost: $0.30
Graqle scores itself — from 6.4 to 8.5 across 5 releases
Graqle uses Graqle to manage its own development. From v0.12.3 (6.4/10) to v0.29.9 (8.5/10) — every improvement guided by the knowledge graph's own intelligence layer. 1,569+ tests. 5,579 compiled nodes. Graph-powered development, by the graph.
This is not a demo feature. This is proof the tool works at the scale and complexity of real software.
Full CLI reference
Scan & Build
| Command | Description |
|---|---|
graq init |
Scan repo, build graph, auto-wire IDE |
graq scan repo . |
Scan codebase — 13 node types, 10 edge types, AST-level |
graq scan docs ./docs |
Ingest PDF, DOCX, PPTX, Markdown into graph |
graq compile |
Risk scores, insights, CLAUDE.md auto-injection |
graq verify |
Run all governance gate checks |
graq doctor |
Health check — graph integrity, backend, config |
Reason & Audit
| Command | Description |
|---|---|
graq auto "task" |
Autonomous loop — plan, generate, write, test, fix, retry |
graq run "question" |
Natural language query — auto-routed to best tool |
graq reason "question" |
Multi-agent graph reasoning — confidence + evidence |
graq context module |
500-token focused context for any module |
graq impact module |
BFS blast radius — what breaks if this changes |
graq preflight "change" |
Pre-change gate — lessons + risk + safety boundaries |
graq predict "query" |
Confidence-gated prediction with optional write-back |
graq lessons topic |
Past mistakes relevant to current query |
Teach & Learn
| Command | Description |
|---|---|
graq learn "fact" |
Teach the graph — persists across sessions and teams |
graq learn node "name" |
Add a named node |
graq learn edge "A" "B" |
Add a typed relationship |
graq learned |
List everything the graph has been taught |
graq grow |
Incremental rescan (runs on git commit via hook) |
Cloud & Sync
| Command | Description |
|---|---|
graq login --api-key <YOUR_API_KEY> |
Authenticate with Graqle cloud |
graq cloud push |
Push graph to S3 — team sync |
graq cloud pull --merge |
Pull graph from S3 — preserves local lessons |
graq studio |
Visual dashboard |
graq serve |
REST API server |
graq mcp serve |
MCP server — auto-discovered by Claude Code, Cursor, Windsurf |
SCORCH — UX Friction Auditing
| Command | Description |
|---|---|
graq scorch run |
Full 12-dimension audit with Claude Vision |
graq scorch behavioral |
12 behavioral UX tests — zero AI cost |
graq scorch a11y |
WCAG 2.1 accessibility |
graq scorch perf |
Core Web Vitals |
graq scorch security |
CSP, XSS, exposed keys |
graq scorch mobile |
Touch targets + viewport |
graq scorch conversion |
CTA + trust signals |
graq scorch seo |
SEO + Open Graph |
graq scorch brand |
Visual consistency |
graq scorch diff |
Before/after regression detection |
Phantom — Browser Automation
pip install graqle[phantom] && python -m playwright install chromium
| Command | Description |
|---|---|
graq phantom browse URL |
Open browser, screenshot + DOM summary |
graq phantom audit URL |
10-dimension audit on any live page |
graq phantom discover URL |
Auto-crawl all navigable pages |
graq phantom flow file.json |
Execute multi-step user journey |
Works on any website. Results feed back into the knowledge graph automatically.
Pricing
| Free ($0) | Pro ($19/mo) | Team ($29/dev/mo) | Enterprise (Custom) | |
|---|---|---|---|---|
| CLI + SDK + MCP | Unlimited | Unlimited | Unlimited | Unlimited |
| All 14 backends | ✅ | ✅ | ✅ | ✅ |
| Graph nodes | 500 | 25,000 | Unlimited | Unlimited |
| Cloud projects | 1 | 3 | Unlimited | Unlimited |
| SCORCH Vision | — | ✅ | ✅ | ✅ |
| Phantom Computer Skills | — | ✅ | ✅ | ✅ |
| Cross-project graphs | — | ✅ | ✅ | ✅ |
| Team shared graphs | — | — | ✅ | ✅ |
| SSO + audit logs | — | — | — | ✅ |
| On-premise deployment | — | — | — | ✅ |
Security & Privacy
- Local by default. All processing runs on your machine. No telemetry.
- Your API keys. LLM calls go directly to your provider — never proxied.
- Cloud is opt-in. Uploads graph structure only — never source code.
- Air-gapped mode.
GRAQLE_OFFLINE=1— full functionality, zero network calls.
Supply-chain integrity (v0.35.0+)
| Protection | What it does |
|---|---|
| PyPI Trusted Publishing | No long-lived API tokens — GitHub Actions OIDC only |
| Sigstore signatures | Every wheel signed; bundle on every GitHub Release |
| CycloneDX SBOM | Full bill of materials for every release |
| pip-audit in CI | CVE scan on every PR — blocks on CRITICAL/HIGH |
| .pth file guard | Blocks publish if wheel contains .pth files |
| Reproducible builds | SOURCE_DATE_EPOCH pinned — rebuild and compare checksums |
pip install "graqle[security]"
graq trustctl verify # verify installed version against Sigstore
FAQ
How is this different from Copilot / Cursor?
Copilot and Cursor are file-level tools. They see what is written in one file. Graqle sees the relationships between files — the dependency graph, the assumption chains, the blast radius of every change. They generate code. Graqle makes generated code safe to ship. They are not competitors. Graqle is the layer beneath them.
How is this different from LangChain or CrewAI?
LangChain and CrewAI are orchestration frameworks — they chain agents and prompts. They are stateless: no persistent graph, no accumulated institutional memory, no topology-governed agent activation. Graqle is the persistent typed knowledge substrate that agentic frameworks are missing. If you are building agents that write code, Graqle is the memory and governance layer your agents need underneath.
Does my code leave my machine?
Never. All graph processing is local. Cloud sync uploads graph structure only — never source code. Use GRAQLE_OFFLINE=1 for fully air-gapped operation.
Can I use my own LLM / AWS account?
Yes. 14 backends. One line in graqle.yaml switches providers. AWS Bedrock uses your existing IAM profile — no new credentials needed. Ollama runs fully offline on your own GPU at zero cost.
How long does scanning take?
Under 30 seconds for most codebases. 10K+ file monorepos take 1–2 minutes. The graph persists — subsequent scans are incremental.
Why not just use static analysis?
Static analysis tells you what code exists. Graqle tells you how it connects, what breaks when it changes, what your team has learned about it, and what the blast radius of the next change will be. Static analysis is a search tool. Graqle is a reasoning architecture.
Patent & License
European Patent Applications EP26162901.8 and EP26166054.2 — Quantamix Solutions B.V. Phantom browser automation plugin: Copyright 2026 Quantamix Solutions B.V. Free to use under the license terms. See SECURITY.md for supply-chain documentation.
@article{kumar2026graqle,
title = {GraQle: Governed Intelligence through Graph-of-Agents Reasoning},
author = {Kumar, Harish},
year = {2026},
institution = {Quantamix Solutions B.V.},
url = {https://github.com/quantamixsol/graqle}
}
Your AI generates code at 10x speed. Graqle makes sure it's safe to ship.
pip install graqle && graq init
⭐ Star this repo — it helps other developers find it.
Built by Quantamix Solutions B.V. · Uithoorn, The Netherlands 🇳🇱
Copilot forgot. Graqle remembered.
Project details
Release history Release notifications | RSS feed
Download files
Download the file for your platform. If you're not sure which to choose, learn more about installing packages.
Source Distribution
Built Distribution
Filter files by name, interpreter, ABI, and platform.
If you're not sure about the file name format, learn more about wheel file names.
Copy a direct link to the current filters
File details
Details for the file graqle-0.51.0.tar.gz.
File metadata
- Download URL: graqle-0.51.0.tar.gz
- Upload date:
- Size: 3.9 MB
- Tags: Source
- Uploaded using Trusted Publishing? Yes
- Uploaded via: twine/6.1.0 CPython/3.13.12
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
8ae7e63015fe79d30234af98924d47e9b3d14bd5c09fd642a223d2e7f5e8a858
|
|
| MD5 |
2c98af0329a0e63a470e8ab93ad2f907
|
|
| BLAKE2b-256 |
d6565144479bd27b69c21501cfa8c4519f34f73bbfb077d02021794f9b0e8596
|
Provenance
The following attestation bundles were made for graqle-0.51.0.tar.gz:
Publisher:
ci.yml on quantamixsol/graqle
-
Statement:
-
Statement type:
https://in-toto.io/Statement/v1 -
Predicate type:
https://docs.pypi.org/attestations/publish/v1 -
Subject name:
graqle-0.51.0.tar.gz -
Subject digest:
8ae7e63015fe79d30234af98924d47e9b3d14bd5c09fd642a223d2e7f5e8a858 - Sigstore transparency entry: 1280632987
- Sigstore integration time:
-
Permalink:
quantamixsol/graqle@1c1f364f6a72022c45571cb61f93db8f1513c1f7 -
Branch / Tag:
refs/tags/v0.51.0 - Owner: https://github.com/quantamixsol
-
Access:
public
-
Token Issuer:
https://token.actions.githubusercontent.com -
Runner Environment:
github-hosted -
Publication workflow:
ci.yml@1c1f364f6a72022c45571cb61f93db8f1513c1f7 -
Trigger Event:
push
-
Statement type:
File details
Details for the file graqle-0.51.0-py3-none-any.whl.
File metadata
- Download URL: graqle-0.51.0-py3-none-any.whl
- Upload date:
- Size: 1.7 MB
- Tags: Python 3
- Uploaded using Trusted Publishing? Yes
- Uploaded via: twine/6.1.0 CPython/3.13.12
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
a49b8952ab2a1504f931abfe25e10733ab550915c94d48ab5e847d53070fd4cb
|
|
| MD5 |
01d0f5fadb7ac11ab567d4ff73a4c0ff
|
|
| BLAKE2b-256 |
69dad0001014a6b113bcfd7d0705d51a8d09b3e380d1e1b3928b3b238b768874
|
Provenance
The following attestation bundles were made for graqle-0.51.0-py3-none-any.whl:
Publisher:
ci.yml on quantamixsol/graqle
-
Statement:
-
Statement type:
https://in-toto.io/Statement/v1 -
Predicate type:
https://docs.pypi.org/attestations/publish/v1 -
Subject name:
graqle-0.51.0-py3-none-any.whl -
Subject digest:
a49b8952ab2a1504f931abfe25e10733ab550915c94d48ab5e847d53070fd4cb - Sigstore transparency entry: 1280633003
- Sigstore integration time:
-
Permalink:
quantamixsol/graqle@1c1f364f6a72022c45571cb61f93db8f1513c1f7 -
Branch / Tag:
refs/tags/v0.51.0 - Owner: https://github.com/quantamixsol
-
Access:
public
-
Token Issuer:
https://token.actions.githubusercontent.com -
Runner Environment:
github-hosted -
Publication workflow:
ci.yml@1c1f364f6a72022c45571cb61f93db8f1513c1f7 -
Trigger Event:
push
-
Statement type:




















