Kestrel Threat Hunting Language
Project description







[News] Kestrel session at Black Hat USA 2023
Kestrel is a threat hunting language aiming to make cyber threat hunting fast by providing a layer of abstraction to build reusable, composable, and shareable hunt-flow. Starting with:
The Goal
Software developers write Python or Swift than machine code to quickly turn business logic into applications. Threat hunters write Kestrel to quickly turn threat hypotheses into hunt-flow. We see threat hunting as an interactive procedure to create customized intrusion detection systems on the fly, and hunt-flow is to hunts as control-flow is to ordinary programs.
What does it mean by hunt fast?
Do NOT write the same TTP pattern in different data source queries.
Do NOT write one-time-use adapaters to connect hunt steps.
Do NOT waste your existing analytic scripts/programs in future hunts.
Do construct your hunt-flow from smaller reuseable hunt-flow.
Do share your huntbook with your future self and your colleagues.
Do get interactive feedback and revise hunt-flow on the fly.
Kestrel in a Nutshell
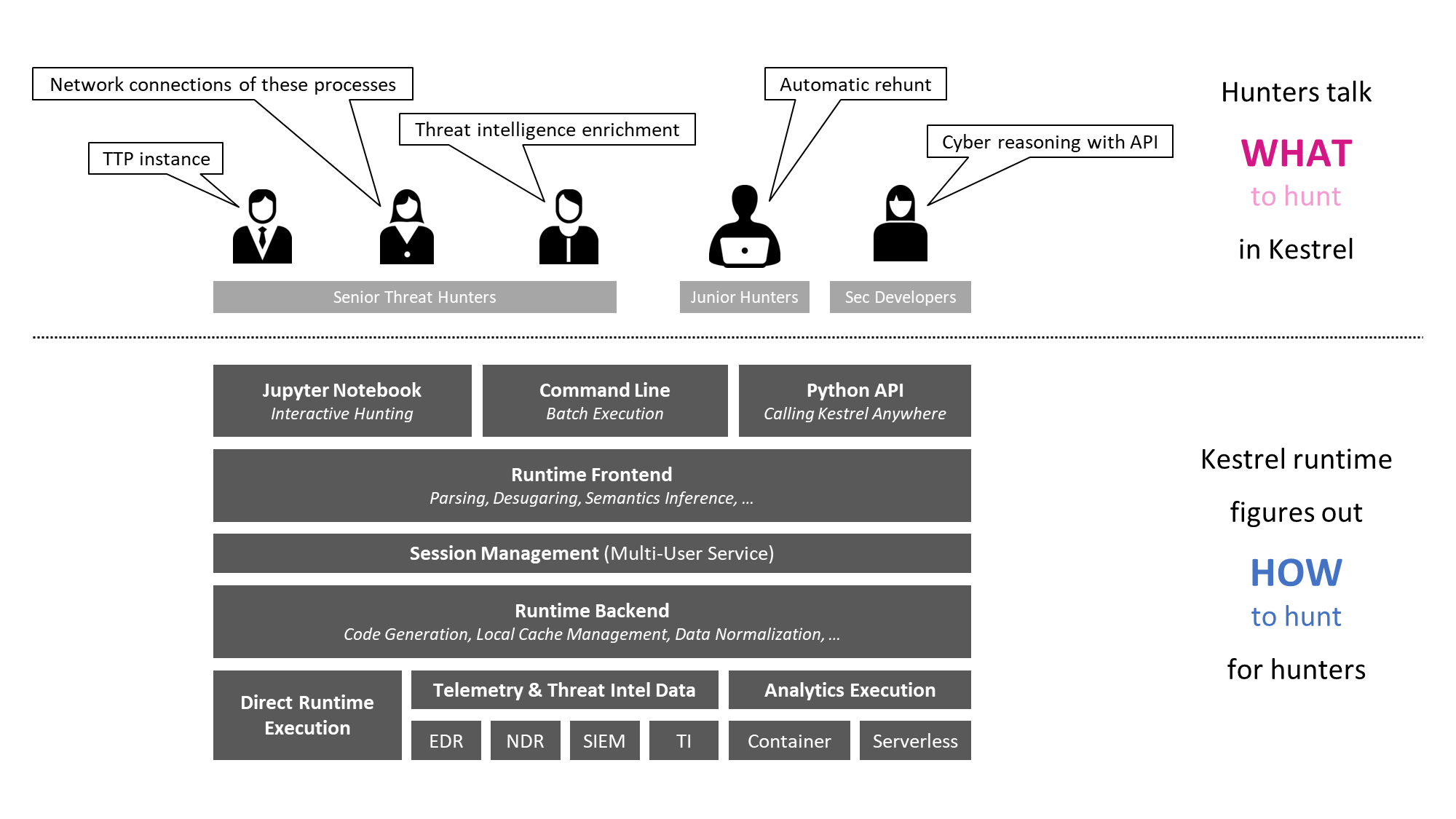
Kestrel language: a threat hunting language for a human to express what to hunt.
expressing the knowledge of what in patterns, analytics, and hunt flows.
composing reusable hunting flows from individual hunting steps.
reasoning with human-friendly entity-based data representation abstraction.
thinking across heterogeneous data and threat intelligence sources.
applying existing public and proprietary detection logic as analytic hunt steps.
reusing and sharing individual hunting steps, hunt-flow, and entire huntbooks.
Kestrel runtime: a machine interpreter that deals with how to hunt.
compiling the what against specific hunting platform instructions.
executing the compiled code locally and remotely.
assembling raw logs and records into entities for entity-based reasoning.
caching intermediate data and related records for fast response.
prefetching related logs and records for link construction between entities.
defining extensible interfaces for data sources and analytics execution.
Basic Concepts and Howto
Visit Kestrel documentation to learn Kestrel:
Learn concepts and syntax:
Hunt in your environment:
Kestrel Huntbooks And Analytics
Kestrel huntbook: community-contributed Kestrel huntbooks
Kestrel analytics: community-contributed Kestrel analytics
Kestrel Hunting Blogs
Building a Huntbook to Discover Persistent Threats from Scheduled Windows Tasks
Practicing Backward And Forward Tracking Hunts on A Windows Host
Building Your Own Kestrel Analytics and Sharing With the Community
Setting Up The Open Hunting Stack in Hybrid Cloud With Kestrel and SysFlow
Fun with securitydatasets.com and the Kestrel PowerShell Deobfuscator
Talks And Demos
Talk summary (visit Kestrel documentation on talks to learn details):
2023/08 Black Hat USA 2023
2022/12 Infosec Jupyterthon 2022 [IJ’22 live hunt recording]
2022/08 Black Hat USA 2022 [BH’22 recording | BH’22 hunting lab]
2022/04 SC eSummit on Threat Hunting & Offense Security (free to register/playback)
2021/12 Infosec Jupyterthon 2021 [IJ’21 live hunt recording]
2021/11 BlackHat Europe 2021
2021/10 SANS Threat Hunting Summit 2021: [SANS’21 session recording]
2021/05 RSA Conference 2021: [RSA’21 session recording]
Connecting With The Community
Join Kestrel slack channel:
Get a slack invitation to join Open Cybersecurity Alliance workspace
Join the kestrel channel to ask questions and connect with other hunters
Contribute to the language development (Apache License 2.0):
Create a GitHub Issue to report bugs and suggest new features
Follow the contributing guideline to submit your pull request
Refer to the governance documentation regarding PR merge, release, and vulnerability disclosure
Share your huntbook and analytics:
Project details
Release history Release notifications | RSS feed
Download files
Download the file for your platform. If you're not sure which to choose, learn more about installing packages.
Source Distribution
Built Distribution
Filter files by name, interpreter, ABI, and platform.
If you're not sure about the file name format, learn more about wheel file names.
Copy a direct link to the current filters
File details
Details for the file kestrel-lang-1.7.6.tar.gz.
File metadata
- Download URL: kestrel-lang-1.7.6.tar.gz
- Upload date:
- Size: 98.9 kB
- Tags: Source
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/4.0.2 CPython/3.10.13
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
55489271073edf5ac345969c80ef4fcdbc8965f1e46014d35754fd7509736410
|
|
| MD5 |
c7cc1ee9986426281b35be246761ec20
|
|
| BLAKE2b-256 |
496f81123f61f1d5f0da97c3e60ae7047dae3a04592e5ff073300b5dbf182586
|
File details
Details for the file kestrel_lang-1.7.6-py3-none-any.whl.
File metadata
- Download URL: kestrel_lang-1.7.6-py3-none-any.whl
- Upload date:
- Size: 92.7 kB
- Tags: Python 3
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/4.0.2 CPython/3.10.13
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
129bb31931e17463ee2f49510dc2fb6703f9cd87a9829b29b515fa0a4ece8fc2
|
|
| MD5 |
7a077b3a73e8423da04d2a98ef675cd6
|
|
| BLAKE2b-256 |
efd729fd43cf900d5dc6cf26cf1489df6e9246108dea27f79c70107646500897
|