This package enable to use the computer as a Rogue AP in a MitM Channel-Based attack
Project description
mitm-channel-based-package
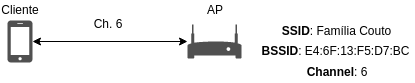
This is a Python Package to help you to create a MitM (Man-in-the-Middle) channel-based attack in a 802.11 network.
Configure Interfaces and Create Sockets
The package needs two wireless cards to work. It configures the 2 interfaces on them and more 2 virtual interfaces (the interfaces names may vary according to the system):
- nic_real_mon (wlan1) - monitor interface that listen packets on the real channel
- nic_real_clientack (wlan1sta1) - managed interface to ACK frames sent by the real AP
- nic_rogue_ap (wlan0) - managed interface on which the Rogue AP works (hostapd_rogue)
- nic_rogue_mon (wlan0mon) - monitor interface that listen packet on the rogue channel
Then, it is created sockets on monitor interfaces.
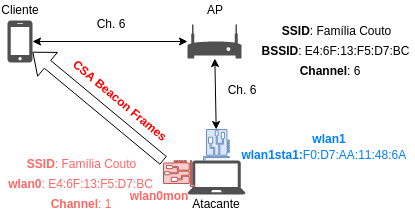
Copy the Real AP configuration, initiate hostapd_rogue.conf and send CSA beacons
-
The package tries to capture one beacon sent by the Real AP, then copies it's network configuration to create a
hostapd_rogue.conffile. -
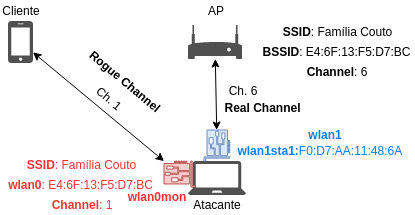
From that, a Rogue AP is created on a different (rogue) channel.
-
After this, the Rogue AP starts to send CSA (Channel Switch Announcement) beacons frames with the new channel on it, to try the clients to connect to the rogue channel.
Project details
Download files
Download the file for your platform. If you're not sure which to choose, learn more about installing packages.
Source Distribution
Built Distribution
Filter files by name, interpreter, ABI, and platform.
If you're not sure about the file name format, learn more about wheel file names.
Copy a direct link to the current filters
File details
Details for the file mitm_channel_based-0.0.5.tar.gz.
File metadata
- Download URL: mitm_channel_based-0.0.5.tar.gz
- Upload date:
- Size: 11.7 kB
- Tags: Source
- Uploaded using Trusted Publishing? No
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
84da9fb242efbc3e0ea285dc703a30ea5b0a5f8a4606267a585bca37d4f054fc
|
|
| MD5 |
df994e959a7555c2eda232c4d58a209d
|
|
| BLAKE2b-256 |
c2f762fd3a1d98027e4b56ef9c54a99db87a805b42d9d9eace97e1afdfbe16e5
|
File details
Details for the file mitm_channel_based-0.0.5-py2-none-any.whl.
File metadata
- Download URL: mitm_channel_based-0.0.5-py2-none-any.whl
- Upload date:
- Size: 13.8 kB
- Tags: Python 2
- Uploaded using Trusted Publishing? No
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
ae19bbac43a25ccd16bf96599a86971f5daaaf3bd2625aa4d495161deaf4380e
|
|
| MD5 |
5a6a0abbf1383a8008190e3e383b2af8
|
|
| BLAKE2b-256 |
839009bd4987bdbd4b120d55eb94c01e5f44680cfbe6f3a2d3d18a18797275c9
|











