OpenID Connect provider server for testing authentication
Project description
OpenID Provider Mock
A mock OpenID Provider server to test and develop OpenID Connect authentication.
You can find the full documentation here.
Usage
The simplest method to run the server is
pipx:
$ pipx run oidc-provider-mock
Started OpenID provider http://localhost:9400
Alternatively, you can run the server as a container:
docker run -p 9400:9400 ghcr.io/geigerzaehler/oidc-provider-mock
See the “Usage” documentation for details.
Now, configure your OpenID Connect client library in your app to use
http://localhost:9400 as the issuer URL. By default, you can use any client ID
and client secret with the provider.
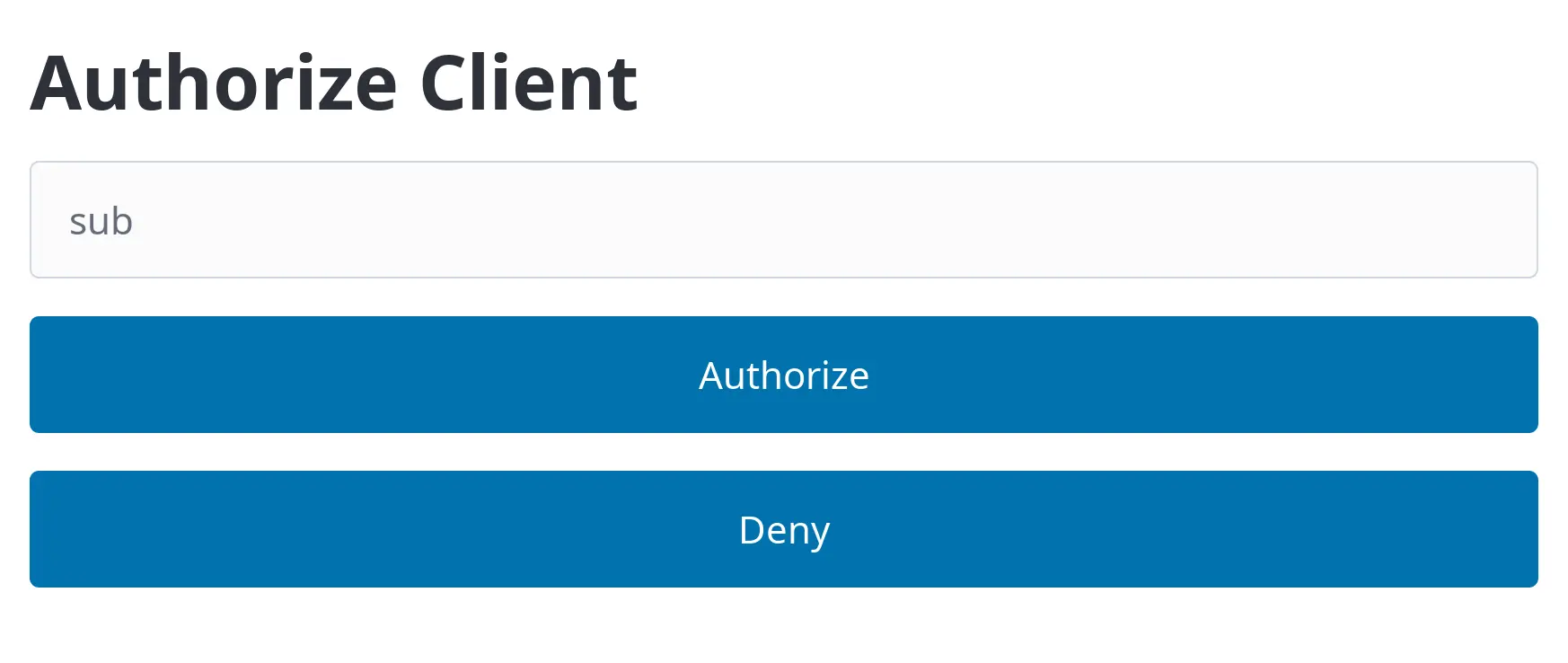
Finally, you can authenticate against the app (the Relying Party) through the mock provider’s login form:
Take a look at the following example that uses the server in a test for a Flask-OIDC app.
@pytest.fixture
def oidc_server():
with oidc_provider_mock.run_server_in_thread() as server:
yield f"http://localhost:{server.server_port}"
def test_auth_code_login(client: flask.testing.FlaskClient, oidc_server: str):
# Add OIDC claims for the user we want to authenticate
response = httpx.put(
f"{oidc_server}/users/{quote('alice@example.com')}",
json={"email": "alice@example.com", "name": "Alice", "custom": ["foo", "bar"]},
)
assert response.status_code == 204
# Start login on the client and get the authorization URL
response = client.get("/login")
assert response.location
# Authorize the client by POSTing to the authorization URL.
response = httpx.post(response.location, data={"sub": "alice@example.com"})
# Go back to the client with the authorization code
assert response.has_redirect_location
response = client.get(response.headers["location"], follow_redirects=True)
# Check that we have been authenticated
assert response.text == "Welcome Alice (alice@example.com)"
For all full testing example, see
examples/flask_oidc_example.py. You can find
more advanced tests in
tests/flask_advanced_test.py.
If you’re using Playwright for end-to-end tests, a login test looks like this:
def test_auth_code_login_playwright(
live_server: LiveServer, oidc_server: str, page: Page
):
# Let the OIDC provider know about the user’s email and name
response = httpx.put(
f"{oidc_server}/users/{quote('alice@example.com')}",
json={"email": "alice@example.com", "name": "Alice"},
)
assert response.status_code == 204
# Start login and be redirected to the provider
page.goto(live_server.url("/login"))
# Authorize with the provider
page.get_by_label("Subject").fill("alice@example.com")
page.get_by_role("button", name="Authorize", exact=True).click()
# Verify that we’re logged in
expect(page.locator("body")).to_contain_text("Welcome Alice (alice@example.com)")
You can find a full example at
examples/flask_oidc_example.py, too.
Alternatives
There already exist a couple of OpendID provider servers for testing. This is how they differ from this project (to the best of my knowledge):
- Does not offer a HTML login form where the subject can be input or authorization denied.
- Behavior can only be customized through the JavaScript API.
- Identities (users) and clients must be statically configured.
- Requires a non-trivial amount of configuration before it can be used.
- Does not have a CLI, only available as a Go library
https://oauth.wiremockapi.cloud/
- Only a hosted version exists
- Claims and user info cannot be customized
- Cannot simulate errors
Project details
Release history Release notifications | RSS feed
Download files
Download the file for your platform. If you're not sure which to choose, learn more about installing packages.
Source Distribution
Built Distribution
Filter files by name, interpreter, ABI, and platform.
If you're not sure about the file name format, learn more about wheel file names.
Copy a direct link to the current filters
File details
Details for the file oidc_provider_mock-0.4.4.tar.gz.
File metadata
- Download URL: oidc_provider_mock-0.4.4.tar.gz
- Upload date:
- Size: 150.3 kB
- Tags: Source
- Uploaded using Trusted Publishing? Yes
- Uploaded via: twine/6.1.0 CPython/3.13.13
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
0c51ec59704184f9b741a4078af6ebc8e839b58b16a9ba9abfaaac7e426ed9c7
|
|
| MD5 |
ac8d07dd49e8ee3528e40274084f6ff0
|
|
| BLAKE2b-256 |
5e5483897b73c1dd7fbdbd364df46b6728ab0536807dea90e7eb3bdb4b102d8b
|
Provenance
The following attestation bundles were made for oidc_provider_mock-0.4.4.tar.gz:
Publisher:
release.yaml on geigerzaehler/oidc-provider-mock
-
Statement:
-
Statement type:
https://in-toto.io/Statement/v1 -
Predicate type:
https://docs.pypi.org/attestations/publish/v1 -
Subject name:
oidc_provider_mock-0.4.4.tar.gz -
Subject digest:
0c51ec59704184f9b741a4078af6ebc8e839b58b16a9ba9abfaaac7e426ed9c7 - Sigstore transparency entry: 1653451317
- Sigstore integration time:
-
Permalink:
geigerzaehler/oidc-provider-mock@ab6827651c071b0b1fbd1592b369dd30e5719a42 -
Branch / Tag:
refs/heads/main - Owner: https://github.com/geigerzaehler
-
Access:
public
-
Token Issuer:
https://token.actions.githubusercontent.com -
Runner Environment:
github-hosted -
Publication workflow:
release.yaml@ab6827651c071b0b1fbd1592b369dd30e5719a42 -
Trigger Event:
workflow_run
-
Statement type:
File details
Details for the file oidc_provider_mock-0.4.4-py3-none-any.whl.
File metadata
- Download URL: oidc_provider_mock-0.4.4-py3-none-any.whl
- Upload date:
- Size: 26.1 kB
- Tags: Python 3
- Uploaded using Trusted Publishing? Yes
- Uploaded via: twine/6.1.0 CPython/3.13.13
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
a5ab6c85acdf379831b2fcd1ce02bf636492c61e5c22b2a6ab4ede739b4760e6
|
|
| MD5 |
a7685a567e4e785292d53360ca650ba8
|
|
| BLAKE2b-256 |
ff21d5e13df6820284725dfc5bdf1512d0f14703e9fe7aba18e30a75fc3fe3a4
|
Provenance
The following attestation bundles were made for oidc_provider_mock-0.4.4-py3-none-any.whl:
Publisher:
release.yaml on geigerzaehler/oidc-provider-mock
-
Statement:
-
Statement type:
https://in-toto.io/Statement/v1 -
Predicate type:
https://docs.pypi.org/attestations/publish/v1 -
Subject name:
oidc_provider_mock-0.4.4-py3-none-any.whl -
Subject digest:
a5ab6c85acdf379831b2fcd1ce02bf636492c61e5c22b2a6ab4ede739b4760e6 - Sigstore transparency entry: 1653451564
- Sigstore integration time:
-
Permalink:
geigerzaehler/oidc-provider-mock@ab6827651c071b0b1fbd1592b369dd30e5719a42 -
Branch / Tag:
refs/heads/main - Owner: https://github.com/geigerzaehler
-
Access:
public
-
Token Issuer:
https://token.actions.githubusercontent.com -
Runner Environment:
github-hosted -
Publication workflow:
release.yaml@ab6827651c071b0b1fbd1592b369dd30e5719a42 -
Trigger Event:
workflow_run
-
Statement type: