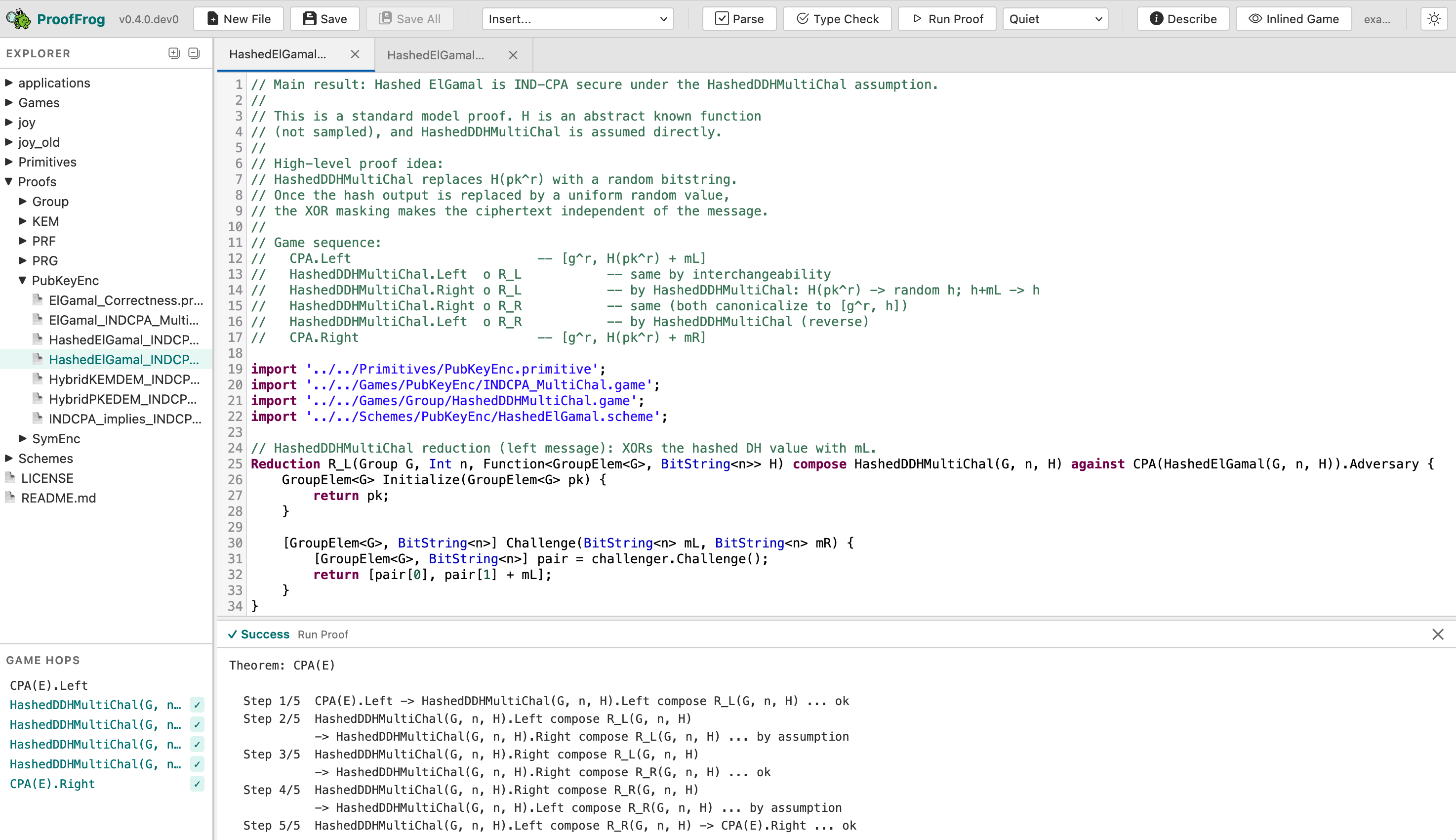
A tool for checking transitions in cryptographic game-hopping proofs
Project description

ProofFrog
A tool for checking transitions in cryptographic game-hopping proofs.
ProofFrog checks the validity of game hops for cryptographic game-hopping proofs in the reduction-based security paradigm: it checks that the starting and ending games match the security definition, and that each adjacent pair of games is either interchangeable (by code equivalence) or justified by a stated assumption. Proofs are written in FrogLang, a small C/Java-style domain-specific language designed to look like a pen-and-paper proof. ProofFrog can be used from the command line, a browser-based editor, or an MCP server for integration with AI coding assistants. ProofFrog is suitable for introductory level proofs, but is not as expressive for advanced concepts as other verification tools like EasyCrypt.
Installation
Requires Python 3.11+.
From PyPI
python3 -m venv .venv
source .venv/bin/activate
pip install proof_frog
After installing, download the examples repository:
proof_frog download-examples
From source
git clone https://github.com/ProofFrog/ProofFrog
cd ProofFrog
git submodule update --init
python3 -m venv .venv
source .venv/bin/activate
pip install -e ".[dev]"
Documentation
Full documentation is available at prooffrog.github.io, including:
- Tutorial — hands-on introduction to writing and checking proofs, and additional worked examples
- Language reference — complete FrogLang reference
- Examples — catalogue of example proofs, largely adapted from The Joy of Cryptography
- CLI reference — command-line usage
- Web editor — browser-based editing and proof checking
- Information about editor plugins and proving with AI assistants
License
ProofFrog is released under the MIT License.
Acknowledgements
ProofFrog was created by Ross Evans and Douglas Stebila, building on the pygamehop tool created by Douglas Stebila and Matthew McKague. For more information about ProofFrog's design, see Ross Evans' master's thesis and eprint 2025/418.
ProofFrog's syntax and approach to modelling is heavily inspired by Mike Rosulek's excellent book The Joy of Cryptography.
We acknowledge the support of the Natural Sciences and Engineering Research Council of Canada (NSERC).
Includes icons from the vscode-codicons project.
Project details
Download files
Download the file for your platform. If you're not sure which to choose, learn more about installing packages.
Source Distribution
Built Distribution
Filter files by name, interpreter, ABI, and platform.
If you're not sure about the file name format, learn more about wheel file names.
Copy a direct link to the current filters
File details
Details for the file proof_frog-0.4.0.tar.gz.
File metadata
- Download URL: proof_frog-0.4.0.tar.gz
- Upload date:
- Size: 1.5 MB
- Tags: Source
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/6.2.0 CPython/3.14.3
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
5a91797e111456e6ad0a831e90a025a1fe686e623f56877ab2f9760bd2efca38
|
|
| MD5 |
26f30ddb62d547706143172225254990
|
|
| BLAKE2b-256 |
23d21d3e734458490fdbf80fdda1de7e167cba09309f92ff9de872c33d21a615
|
File details
Details for the file proof_frog-0.4.0-py3-none-any.whl.
File metadata
- Download URL: proof_frog-0.4.0-py3-none-any.whl
- Upload date:
- Size: 581.3 kB
- Tags: Python 3
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/6.2.0 CPython/3.14.3
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
df1e4454525f8a3787fe9afca6e095354b6b9bd4f35efc717235391afb71e5b0
|
|
| MD5 |
697586edebabc749844752071e13858d
|
|
| BLAKE2b-256 |
7ec23effad8a74778477fec1697f23c88218da3189a16eedeaab733ef2131226
|