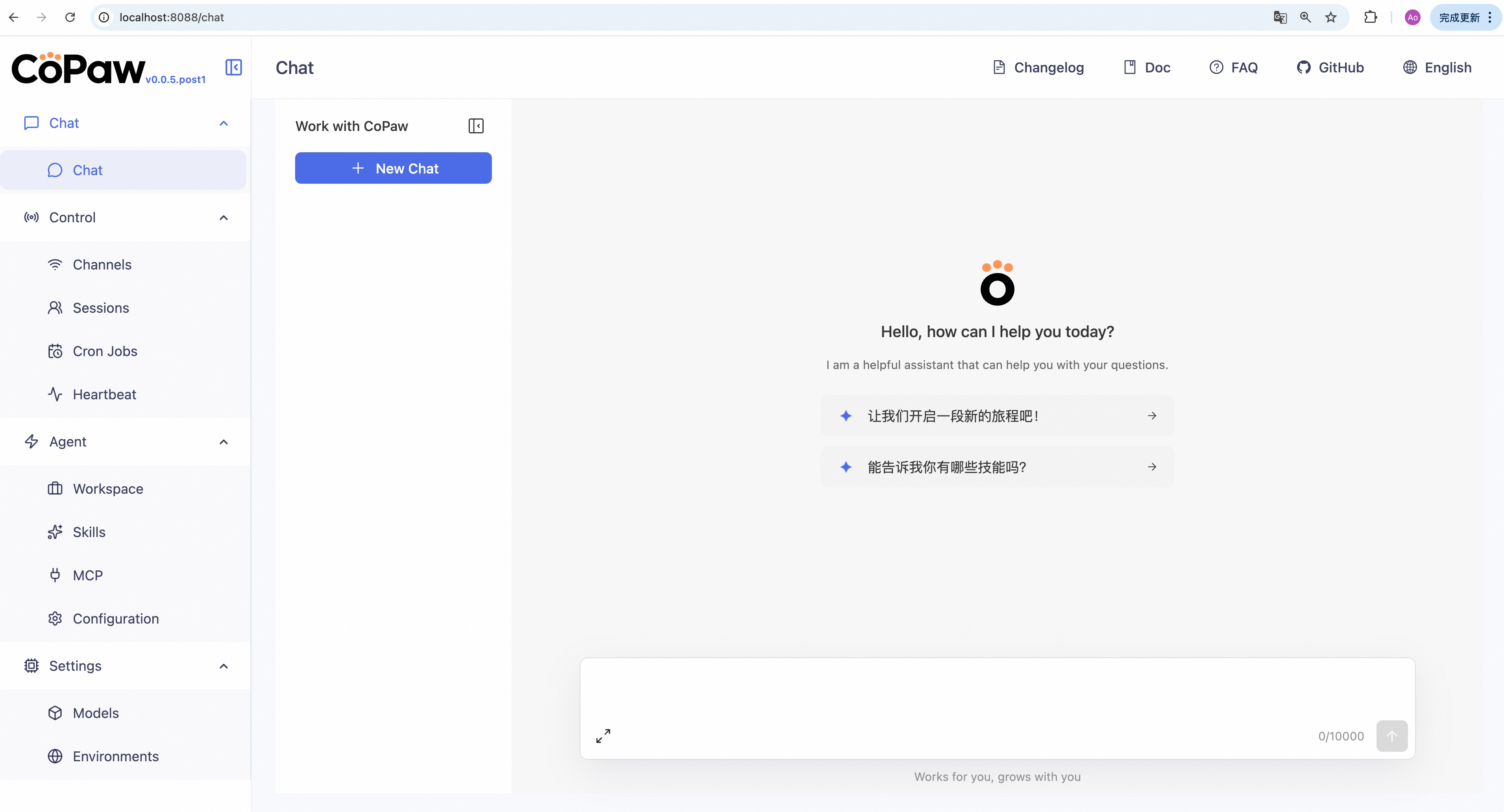
SealClaw is a **personal assistant** that runs in your own environment. It talks to you over multiple channels (DingTalk, Feishu, QQ, Discord, iMessage, etc.) and runs scheduled tasks according to your configuration. **What it can do is driven by Skills — the possibilities are open-ended.** Built-in skills include cron, PDF/Office handling, news digest, file reading, and more; you can add custom skills. All data and tasks run on your machine; no third-party hosting.
Project description
Your Personal AI Assistant; easy to install, deploy on your own machine or on the cloud; supports multiple chat apps with easily extensible capabilities.
Core capabilities:
Every channel — DingTalk, Feishu, QQ, Discord, iMessage, and more. One assistant, connect as you need.
Under your control — Memory and personalization under your control. Deploy locally or in the cloud; scheduled reminders to any channel.
Skills — Built-in cron; custom skills in your workspace, auto-loaded. No lock-in.
What you can do
- Social: daily digest of hot posts (Xiaohongshu, Zhihu, Reddit), Bilibili/YouTube summaries.
- Productivity: newsletter digests to DingTalk/Feishu/QQ, contacts from email/calendar.
- Creative: describe your goal, run overnight, get a draft next day.
- Research: track tech/AI news, personal knowledge base.
- Desktop: organize files, read/summarize docs, request files in chat.
- Explore: combine Skills and cron into your own agentic app.
News
[2026-03-12] We released v0.0.7! See the v0.0.7 Release Notes for the full changelog.
- [v0.0.7] Added: Tool Guard security layer — blocks risky tool calls until user approval; Mattermost and Matrix channel integrations; @mention-only group filtering for Discord/DingTalk/Feishu/Telegram; Telegram Markdown rendering; Feishu emoji reactions and rich text media; QQ image sending; LLM call auto-retry with exponential backoff; LM Studio provider; token usage tracking with dashboard; provider
generate_kwargseditor; workspace file drag-and-drop; chat model switching; agent language selector; context management UI; chat state preservation across navigation; AI skill optimization with streaming; skill card description display; auto PyPI mirror for China. - [v0.0.7] Improved: Provider connection test messages; async workspace zip and session load; provider ID conflict auto-resolution; on-demand model discovery; token recording centralization; built-in skill docs and shell
PATHhandling; Himalaya email skill; memory docs reorganization; Config & Security page refactor. - [v0.0.7] Fixed: DingTalk auth failure cleanup; Discord 2000-char message splitting; channel config type alignment for Matrix/Mattermost/MQTT; Windows shell encoding and process tree cleanup; desktop SSL certificates, IME input, and external URL navigation; magic command session state protection; Ollama modal re-renders; chat request deduplication.
- [v0.0.7] Contributors: Thanks to new contributors: @2catycm, @2niuhe, @yingdachen, @Atletico1999, @buecker, @Cirilla-zmh, @gnipping, @Nufe-muzi, @FuKunZ, @JasonBuildAI, @StarMoonCity, @walker83, @lllcy.
[2026-03-09] We released v0.0.6! See the v0.0.6 Release Notes for the full changelog.
[2026-03-06] We released v0.0.5! See the v0.0.5 Release Notes for the full changelog.
[2026-03-02] We released v0.0.4! See the v0.0.4 Release Notes for the full changelog.
Table of Contents
Recommended reading:
- I want to run SealClaw in 3 commands: Quick Start → open Console in browser.
- I want to chat in DingTalk / Feishu / QQ: Configure channels in the Console.
- I don’t want to install Python: Script install handles Python automatically, or use ModelScope one-click for cloud deployment.
- News
- Quick Start
- API Key
- Local Models
- Documentation
- FAQ
- Roadmap
- Contributing
- Install from source
- Why SealClaw?
- Built by
- License
Quick Start
pip install
If you prefer managing Python yourself:
pip install sealclaw
sealclaw init --defaults
sealclaw app
Then open http://127.0.0.1:8088/ in your browser for the Console (chat with SealClaw, configure the agent). To talk in DingTalk, Feishu, QQ, etc., add a channel in the docs.
Script install
No Python setup required, one command installs everything. The script will automatically download uv (Python package manager), create a virtual environment, and install SealClaw with all dependencies (including Node.js and frontend assets). Note: May not work in restricted network environments or corporate firewalls.
macOS / Linux:
curl -fsSL https://sealclaw.io/install.sh | bash
To install with Ollama support:
curl -fsSL https://sealclaw.io/install.sh | bash -s -- --extras ollama
To install with multiple extras (e.g., Ollama + llama.cpp):
curl -fsSL https://sealclaw.io/install.sh | bash -s -- --extras ollama,llamacpp
Windows (CMD):
curl -fsSL https://sealclaw.io/install.bat -o install.bat && install.bat
Windows (PowerShell):
irm https://sealclaw.io/install.ps1 | iex
Note: The installer will automatically check the status of uv. If it is not installed, it will attempt to download and configure it automatically. If the automatic installation fails, please follow the on-screen prompts or execute
python -m pip install -U uv, then rerun the installer.
⚠️ Special Notice for Windows Enterprise LTSC Users
If you are using Windows LTSC or an enterprise environment governed by strict security policies, PowerShell may run in Constrained Language Mode, potentially causing the following issue:
If using CMD (.bat): Script executes successfully but fails to write to
PathThe script completes file installation. Due to Constrained Language Mode, it cannot automatically update environment variables. Manually configure as follows:
- Locate the installation directory:
- Check if
uvis available: Enteruv --versionin CMD. If a version number appears, only configure the SealClaw path. If you receive the prompt'uv' is not recognized as an internal or external command, operable program or batch file,configure both paths.- uv path (choose one based on installation location; use if
uvfails): Typically%USERPROFILE%\.local\bin,%USERPROFILE%\AppData\Local\uv, or theScriptsfolder within your Python installation directory- SealClaw path: Typically located at
%USERPROFILE%\.sealseek\bin.- Manually add to the system's Path environment variable:
- Press
Win + R, typesysdm.cpland press Enter to open System Properties.- Click “Advanced” -> “Environment Variables”.
- Under “System variables”, locate and select
Path, then click “Edit”.- Click “New”, enter both directory paths sequentially, then click OK to save.
If using PowerShell (.ps1): Script execution interrupted
Due to Constrained Language Mode, the script may fail to automatically download
uv.
- Manually install uv: Refer to the GitHub Release to download
uv.exeand place it in%USERPROFILE%\.local\binor%USERPROFILE%\AppData\Local\uv; or ensure Python is installed and runpython -m pip install -U uv.- Configure
uvenvironment variables: Add theuvdirectory and%USERPROFILE%\.sealseek\binto your system'sPathvariable.- Re-run the installation: Open a new terminal and execute the installation script again to complete the
SealClawinstallation.- Configure the
SealClawenvironment variable: Add%USERPROFILE%\.sealseek\binto your system'sPathvariable.
Once installed, open a new terminal and run:
sealclaw init --defaults # or: sealclaw init (interactive)
sealclaw app
Install options
macOS / Linux:
# Install a specific version
curl -fsSL ... | bash -s -- --version 0.0.2
# Install from source (dev/testing)
curl -fsSL ... | bash -s -- --from-source
# With local model support
bash install.sh --extras llamacpp # llama.cpp (cross-platform)
bash install.sh --extras mlx # MLX (Apple Silicon)
bash install.sh --extras llamacpp,mlx
# Upgrade — just re-run the installer
curl -fsSL ... | bash
# Uninstall
sealclaw uninstall # keeps config and data
sealclaw uninstall --purge # removes everything
Windows (PowerShell):
# Install a specific version
irm ... | iex; .\install.ps1 -Version 0.0.2
# Install from source (dev/testing)
.\install.ps1 -FromSource
# With local model support
.\install.ps1 -Extras llamacpp # llama.cpp (cross-platform)
.\install.ps1 -Extras mlx # MLX
.\install.ps1 -Extras llamacpp,mlx
# Upgrade — just re-run the installer
irm ... | iex
# Uninstall
sealclaw uninstall # keeps config and data
sealclaw uninstall --purge # removes everything
Desktop Application (Beta)
Beta Notice: The desktop application is currently in Beta testing phase with the following known limitations:
- Incomplete compatibility testing: Not fully tested across all system versions and hardware configurations
- Potential performance issues: Startup time, memory usage, and other performance aspects may need further optimization
- Features under development: Some features may be unstable or missing
If you're not comfortable with command-line tools, you can download and use SealClaw's desktop application without manually configuring Python environments or running commands.
Download
Download the desktop app from GitHub Releases:
- Windows:
SealClaw-Setup-<version>.exe - macOS:
SealClaw-<version>-macOS.zip(Apple Silicon recommended)
Features
- ✅ Zero configuration: Download and double-click to run, no need to install Python or configure environment variables
- ✅ Cross-platform: Supports Windows 10+ and macOS 14+
- ✅ Visual interface: Automatically opens browser interface, no need to manually enter addresses
- ⚠️ Beta stage: Features are continuously being improved, feedback welcome
First Launch
Important: The first launch may take 10-60 seconds (depending on your system configuration). The application needs to initialize the Python environment and load dependencies. Please wait patiently for the browser window to open automatically.
macOS: Bypass System Security Restrictions
When you download the SealClaw macOS app from Releases, macOS may show: "Apple cannot verify that 'SealClaw' contains no malicious software". This happens because the app is not notarized. You can still open it as follows:
-
Right-click to open (recommended) Right-click (or Control+click) the SealClaw app → Open → in the dialog click Open again. This tells Gatekeeper you trust the app; after that you can double-click to launch as usual.
-
Allow in System Settings If it is still blocked, go to System Settings → Privacy & Security, scroll to the message like "SealClaw was blocked because it is from an unidentified developer", and click Open Anyway or Allow.
-
Remove quarantine attribute (not recommended for most users) In Terminal run:
xattr -cr /Applications/SealClaw.app(or use the path to the.appafter unzipping). This clears the "downloaded from the internet" quarantine flag so the warning usually does not appear, but is less safe and controllable than using Right-click → Open.
For detailed usage instructions, troubleshooting, and common issues, see the Desktop Application Guide.
Using Docker
Images are on Docker Hub (agentscope/sealclaw). Image tags: latest (stable); pre (PyPI pre-release).
docker pull agentscope/sealclaw:latest
docker run -p 127.0.0.1:8088:8088 \
-v sealclaw-data:/app/working \
-v sealclaw-secrets:/app/working.secret \
agentscope/sealclaw:latest
Also available on Alibaba Cloud Container Registry (ACR) for users in China: agentscope-registry.ap-southeast-1.cr.aliyuncs.com/agentscope/sealclaw (same tags).
Then open http://127.0.0.1:8088/ for the Console. Config, memory, and skills are stored in the sealclaw-data volume; model provider settings and API keys are in the sealclaw-secrets volume. To pass API keys (e.g. DASHSCOPE_API_KEY), add -e VAR=value or --env-file .env to docker run.
Connecting to Ollama or other services on the host machine
Inside a Docker container,
localhostrefers to the container itself, not your host machine. If you run Ollama (or other model services) on the host and want SealClaw in Docker to reach them, use one of these approaches:Option A — Explicit host binding (all platforms):
docker run -p 127.0.0.1:8088:8088 \ --add-host=host.docker.internal:host-gateway \ -v sealclaw-data:/app/working \ -v sealclaw-secrets:/app/working.secret \ agentscope/sealclaw:latestThen in SealClaw Settings → Models, change the Base URL to
http://host.docker.internal:<port>— for example,http://host.docker.internal:11434for Ollama, orhttp://host.docker.internal:1234/v1for LM Studio.Option B — Host networking (Linux only):
docker run --network=host \ -v sealclaw-data:/app/working \ -v sealclaw-secrets:/app/working.secret \ agentscope/sealclaw:latestNo port mapping (
-p) is needed; the container shares the host network directly. Note that all container ports are exposed on the host, which may cause conflicts if the port is already in use.Note: If you only mount
/app/workingwithout a separate volume for/app/working.secret, the entrypoint will automatically redirect secrets into/app/working/.secretso they persist on the same volume.
The image is built from scratch. To build the image yourself, please refer to the Build Docker image section in scripts/README.md, and then push to your registry.
Using ModelScope
No local install? ModelScope Studio one-click cloud setup. Set your Studio to non-public so others cannot control your SealClaw.
Deploy on Alibaba Cloud ECS
To run SealClaw on Alibaba Cloud (ECS), use the one-click deployment: open the SealClaw on Alibaba Cloud (ECS) deployment link and follow the prompts. For step-by-step instructions, see Alibaba Cloud Developer: Deploy your AI assistant in 3 minutes.
API Key
If you use a cloud LLM (e.g. DashScope, ModelScope), you must configure an API key before chatting. SealClaw will not work until a valid key is set. See the official docs for details.
How to configure:
- Console (recommended) — After running
sealclaw app, open http://127.0.0.1:8088/ → Settings → Models. Choose a provider, enter the API Key, and enable that provider and model. sealclaw init— When you runsealclaw init, it will guide you through configuring the LLM provider and API key. Follow the prompts to choose a provider and enter your key.- Environment variable — For DashScope you can set
DASHSCOPE_API_KEYin your shell or in a.envfile in the working directory.
Tools that need extra keys (e.g. TAVILY_API_KEY for web search) can be set in Console Settings → Environment variables, or see Config for details.
Using local models only? If you use Local Models (llama.cpp or MLX), you do not need any API key.
Local Models
SealClaw can run LLMs entirely on your machine — no API keys or cloud services required. See the official docs for details.
| Backend | Best for | Install |
|---|---|---|
| llama.cpp | Cross-platform (macOS / Linux / Windows) | pip install 'sealclaw[llamacpp]' or bash install.sh --extras llamacpp |
| MLX | Apple Silicon Macs (M1/M2/M3/M4) | pip install 'sealclaw[mlx]' or bash install.sh --extras mlx |
| Ollama | Cross-platform (requires Ollama service) | pip install 'sealclaw[ollama]' or bash install.sh --extras ollama |
After installing, you can download and manage local models in the Console UI. You can also use the command line:
sealclaw models download Qwen/Qwen3-4B-GGUF
sealclaw models # select the downloaded model
sealclaw app # start the server
Documentation
| Topic | Description |
|---|---|
| Introduction | What SealClaw is and how to use it |
| Quick start | Install and run (local or ModelScope Studio) |
| Console | Web UI: chat and agent configuration |
| Models | Configure cloud, local, and custom providers |
| Channels | DingTalk, Feishu, QQ, Discord, iMessage, and more |
| Skills | Extend and customize capabilities |
| MCP | Manage MCP clients |
| Memory | Long-term memory |
| Context | Context management mechanism |
| Magic commands | Control conversation state without waiting for the AI |
| Heartbeat | Scheduled check-in and digest |
| Config & working dir | Working directory and config file |
| CLI | Init, cron jobs, skills, clean |
| FAQ | Common questions and troubleshooting |
Full docs in this repo: website/public/docs/.
FAQ
For common questions, troubleshooting tips, and known issues, please visit the FAQ page.
Roadmap
| Area | Item | Status |
|---|---|---|
| Horizontal Expansion | More channels, models, skills, MCPs — community contributions welcome | Seeking Contributors |
| Existing Feature Extension | Display optimization, download hints, Windows path compatibility, etc. — community contributions welcome | Seeking Contributors |
| Console Web UI | Expose more info/config in the Console | In Progress |
| Self-healing | Magic commands and daemon capabilities (CLI, status, restart, logs) | In Progress |
| DaemonAgent: autonomous diagnostics, self-healing, and recovery | Planned | |
| Multi-agent | Background task support | In Progress |
| Multi-agent isolation | Planned | |
| Inter-agent contention resolution | Planned | |
| Multi-agent communication | Planned | |
| Multimodal | Voice/video calls and real-time interaction | In Progress |
| Small + Large Model Collaboration | Train/fine-tune local small LLMs for SealClaw workflows and sensitive-data use cases | In Progress |
| Multi-model routing. Local LLMs for sensitive data; cloud LLMs for planning and coding; balance of privacy, performance, and capability | Planned | |
| Memory System | Experience distillation & skill extraction | In Progress |
| Multimodal memory fusion | Planned | |
| Context-aware proactive delivery | Planned | |
| Security | Shell execution confirmation | Planned |
| Tool/skills security | Planned | |
| Configurable security levels (user-configurable) | Planned | |
| Release & Contributing | Contributing guidance for vibe coding agents | Planned |
| Sandbox | Deeper integration with AgentScope Runtime sandboxes | Long-term Planned |
| Cloud-native | Deeper integration with AgentScope Runtime; leverage cloud compute, storage, and tooling | Long-term Planned |
| Skills Hub | Enrich the AgentScope Skills repository and improve discoverability of high-quality skills | Long-term Planned |
Status: In Progress — actively being worked on; Planned — queued or under design, also welcome contributions; Seeking Contributors — we strongly encourage community contributions; Long-term Planned — longer-horizon roadmap.
Get involved
We are building SealClaw in the open and welcome contributions of all kinds! Check the Roadmap above (especially items marked Seeking Contributors) to find areas that interest you, and read CONTRIBUTING to get started. We particularly welcome:
- Horizontal expansion — new channels, model providers, skills, MCPs.
- Existing feature extension — display and UX improvements, download hints, Windows path compatibility, and the like.
Join the conversation on GitHub Discussions to suggest or pick up work.
Install from source
git clone https://github.com/agentscope-ai/SealClaw.git
cd SealClaw
# Build console frontend first (required for web UI)
cd console && npm ci && npm run build
cd ..
# Copy console build output to package directory
mkdir -p src/sealclaw/console
cp -R console/dist/. src/sealclaw/console/
# Install Python package
pip install -e .
- Dev (tests, formatting):
pip install -e ".[dev,full]" - Then: Run
sealclaw init --defaults, thensealclaw app.
发布到 PyPI
SealClaw 通过 PyPI 分发,桌面端(xc-sealseek-desktop-mainapp)通过 .sealclaw-version 锁定版本号,构建时自动从 PyPI 下载 wheel。
CI 自动发布(推荐)
在 GitHub 上创建 Release(tag 格式 v*),CI 自动触发 publish-pypi.yml:
- 构建 console 前端
python -m build生成 wheel- 推送到 PyPI
前提: 仓库 Secrets 中需配置 PYPI_API_TOKEN。
也可通过 workflow_dispatch 手动触发。
手动本地发布
# 1. 构建 wheel(含 console 前端,如果 console/ 目录存在)
bash scripts/wheel_build.sh
# 2. 上传到 PyPI
pip install twine
twine upload dist/sealclaw-*.whl
# Username: __token__
# Password: pypi-xxxxxxxx(PyPI API Token)
版本号规范
版本号在 src/sealclaw/__version__.py 中维护,遵循 PEP 440:
| 版本号格式 | 用途 | pip 行为 |
|---|---|---|
0.1.9 |
正式发版 | pip install sealclaw==0.1.9 |
0.1.9.dev1 |
开发快照 | pip install --pre sealclaw==0.1.9.dev1 |
0.1.9rc1 |
发版候选 | pip install --pre sealclaw==0.1.9rc1 |
桌面端构建脚本会自动检测版本号中的 dev/rc/a/b 并加上 --pre 参数。
发版流程
修改 __version__.py 为 0.1.9.dev1
│
▼
发布预发布版到 PyPI → 桌面端测试环境验证
│
测试通过
│
▼
修改 __version__.py 为 0.1.9
│
▼
发布正式版到 PyPI → 桌面端更新 .sealclaw-version 为 0.1.9
PyPI API Token 获取
- 注册/登录 https://pypi.org
- Account Settings → API tokens → Add API token
- Scope 选
Project: sealclaw - 复制
pypi-开头的 token - 配置到 GitHub Secrets 的
PYPI_API_TOKEN,或本地~/.pypirc:[pypi] username = __token__ password = pypi-xxxxxxxx
Why SealClaw?
SealClaw represents both a Co Personal Agent Workstation and a "co-paw"—a partner always by your side. More than just a cold tool, SealClaw is a warm "little paw" always ready to lend a hand (or a paw!). It is the ultimate teammate for your digital life.
Built by
AgentScope team · AgentScope · AgentScope Runtime · ReMe
Contact us
| Discord | X (Twitter) | DingTalk |
|---|---|---|
 |
 |
 |
Telemetry
SealClaw collects anonymous usage data during sealclaw init to help us understand our user base and prioritize improvements. Data is sent once per version — when you upgrade SealClaw, telemetry is re-collected so we can track version adoption.
What we collect:
- SealClaw version (e.g., 0.0.7)
- Install method (pip, Docker, or desktop app)
- OS and version (e.g., macOS 14.0, Ubuntu 22.04)
- Python version (e.g., 3.13)
- CPU architecture (e.g., x86_64, arm64)
- GPU availability (yes/no)
What we do NOT collect: No personal data, no files, no credentials, no IP addresses, no identifiable information.
When running sealclaw init interactively, you will be asked whether to opt in. If you choose --defaults, telemetry is accepted automatically. The prompt appears once per version and never affects SealClaw's functionality.
License
SealClaw is released under the Apache License 2.0.
Contributors
All thanks to our contributors:

Project details
Release history Release notifications | RSS feed
Download files
Download the file for your platform. If you're not sure which to choose, learn more about installing packages.
Source Distribution
Built Distribution
Filter files by name, interpreter, ABI, and platform.
If you're not sure about the file name format, learn more about wheel file names.
Copy a direct link to the current filters
File details
Details for the file sealclaw-0.1.12.tar.gz.
File metadata
- Download URL: sealclaw-0.1.12.tar.gz
- Upload date:
- Size: 4.8 MB
- Tags: Source
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/6.2.0 CPython/3.12.13
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
7ba90dc162f0d2d7b836351aedcbaabe9dcb7bc68681adf0055ce6e9364294b8
|
|
| MD5 |
54f4fb656c3d2cc241ff185b5f7b0cff
|
|
| BLAKE2b-256 |
9ab5f7f07dd4d9ac53278e9ab0b89796facb8daceae220f94eb4a9904235106a
|
File details
Details for the file sealclaw-0.1.12-py3-none-any.whl.
File metadata
- Download URL: sealclaw-0.1.12-py3-none-any.whl
- Upload date:
- Size: 5.0 MB
- Tags: Python 3
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/6.2.0 CPython/3.12.13
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
046552ded5bd9ea924f412413b480d0702b4ef9d04696bed558a93b1cedb51b9
|
|
| MD5 |
4c6500abf6780f402a09f0d64a851cb2
|
|
| BLAKE2b-256 |
c195e50bad87c4e1b50fb3514b9bb040025586af42bf37901fa54b1fdbde50ce
|