A super-easy way to record, search and compare AI experiments.
Project description
| Drop a star to support Aim ⭐ |
Join Aim discord community
|

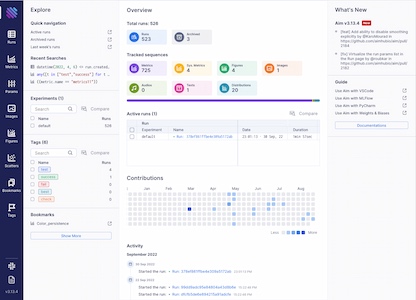
An easy-to-use & supercharged open-source experiment tracker
Aim logs your training runs and any AI Metadata, enables a beautiful UI to compare, observe them and an API to query them programmatically.






















AimStack offers enterprise support that's beyond core Aim. Contact via hello@aimstack.io e-mail.
About • Demos • Ecosystem • Quick Start • Examples • Documentation • Community • Blog
ℹ️ About
Aim is an open-source, self-hosted ML experiment tracking tool designed to handle 10,000s of training runs.
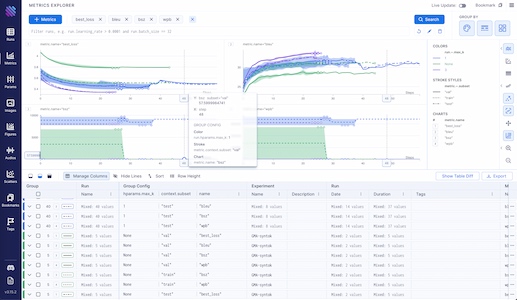
Aim provides a performant and beautiful UI for exploring and comparing training runs. Additionally, its SDK enables programmatic access to tracked metadata — perfect for automations and Jupyter Notebook analysis.
Aim's mission is to democratize AI dev tools 🎯
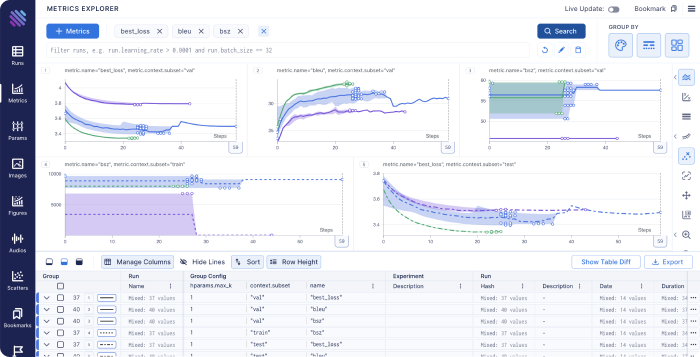
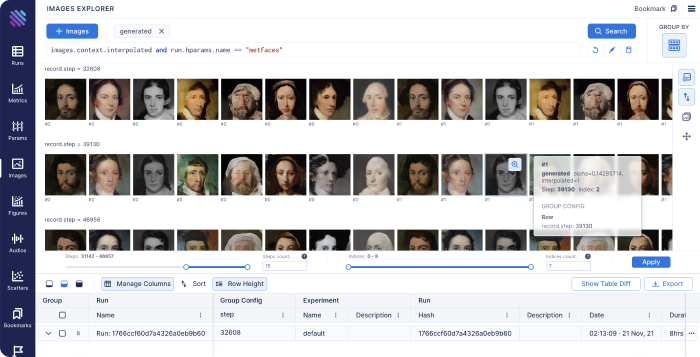
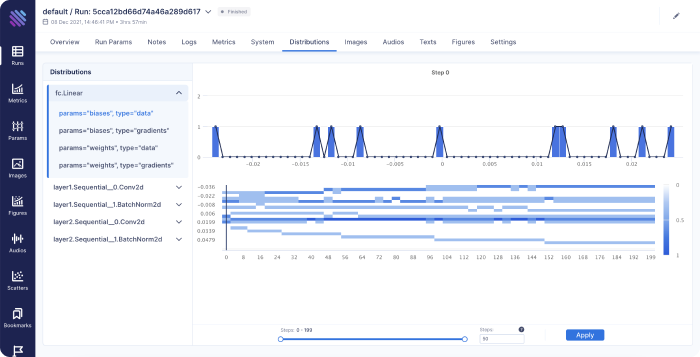
| Log Metadata Across Your ML Pipeline 💾 | Visualize & Compare Metadata via UI 📊 |
|---|---|
|
|
| Run ML Trainings Effectively ⚡ | Organize Your Experiments 🗂️ |
|
|
🎬 Demos
Check out live Aim demos NOW to see it in action.
| Machine translation experiments | lightweight-GAN experiments |
|---|---|
 |
 |
| Training logs of a neural translation model(from WMT'19 competition). | Training logs of 'lightweight' GAN, proposed in ICLR 2021. |
| FastSpeech 2 experiments | Simple MNIST |
|---|---|
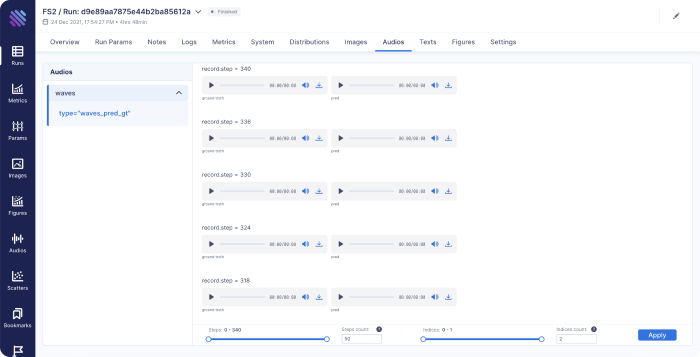 |
 |
| Training logs of Microsoft's "FastSpeech 2: Fast and High-Quality End-to-End Text to Speech". | Simple MNIST training logs. |
🌍 Ecosystem
Aim is not just an experiment tracker. It's a groundwork for an ecosystem. Check out the two most famous Aim-based tools.
| aimlflow | Aim-spaCy |
|---|---|
 |
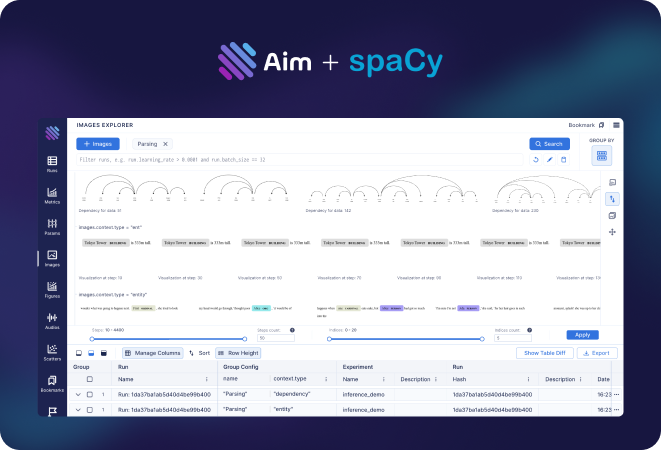 |
| Exploring MLflow experiments with a powerful UI | an Aim-based spaCy experiment tracker |
🏁 Quick start
Follow the steps below to get started with Aim.
1. Install Aim on your training environment
pip3 install aim
2. Integrate Aim with your code
from aim import Run
# Initialize a new run
run = Run()
# Log run parameters
run["hparams"] = {
"learning_rate": 0.001,
"batch_size": 32,
}
# Log metrics
for i in range(10):
run.track(i, name='loss', step=i, context={ "subset":"train" })
run.track(i, name='acc', step=i, context={ "subset":"train" })
See the full list of supported trackable objects(e.g. images, text, etc) here.
3. Run the training as usual and start Aim UI
aim up
Learn more
Migrate from other tools
Aim has built-in converters to easily migrate logs from other tools. These migrations cover the most common usage scenarios. In case of custom and complex scenarios you can use Aim SDK to implement your own conversion script.
Integrate Aim into an existing project
Aim easily integrates with a wide range of ML frameworks, providing built-in callbacks for most of them.
- Integration with Pytorch Ignite
- Integration with Pytorch Lightning
- Integration with Hugging Face
- Integration with Keras & tf.Keras
- Integration with Keras Tuner
- Integration with XGboost
- Integration with CatBoost
- Integration with LightGBM
- Integration with fastai
- Integration with MXNet
- Integration with Optuna
- Integration with PaddlePaddle
- Integration with Stable-Baselines3
- Integration with Acme
- Integration with Prophet
Query runs programmatically via SDK
Aim Python SDK empowers you to query and access any piece of tracked metadata with ease.
from aim import Repo
my_repo = Repo('/path/to/aim/repo')
query = "metric.name == 'loss'" # Example query
# Get collection of metrics
for run_metrics_collection in my_repo.query_metrics(query).iter_runs():
for metric in run_metrics_collection:
# Get run params
params = metric.run[...]
# Get metric values
steps, metric_values = metric.values.sparse_numpy()
Set up a centralized tracking server
Aim remote tracking server allows running experiments in a multi-host environment and collect tracked data in a centralized location.
See the docs on how to set up the remote server.
Deploy Aim on kubernetes
- The official Aim docker image: https://hub.docker.com/r/aimstack/aim
- A guide on how to deploy Aim on kubernetes: https://aimstack.readthedocs.io/en/latest/using/k8s_deployment.html
Read the full documentation on aimstack.readthedocs.io 📖
🆚 Comparisons to familiar tools
TensorBoard vs Aim
Training run comparison
Order of magnitude faster training run comparison with Aim
- The tracked params are first class citizens at Aim. You can search, group, aggregate via params - deeply explore all the tracked data (metrics, params, images) on the UI.
- With tensorboard the users are forced to record those parameters in the training run name to be able to search and compare. This causes a super-tedius comparison experience and usability issues on the UI when there are many experiments and params. TensorBoard doesn't have features to group, aggregate the metrics
Scalability
- Aim is built to handle 1000s of training runs - both on the backend and on the UI.
- TensorBoard becomes really slow and hard to use when a few hundred training runs are queried / compared.
Beloved TB visualizations to be added on Aim
- Embedding projector.
- Neural network visualization.
MLflow vs Aim
MLFlow is an end-to-end ML Lifecycle tool. Aim is focused on training tracking. The main differences of Aim and MLflow are around the UI scalability and run comparison features.
Aim and MLflow are a perfect match - check out the aimlflow - the tool that enables Aim superpowers on Mlflow.
Run comparison
- Aim treats tracked parameters as first-class citizens. Users can query runs, metrics, images and filter using the params.
- MLFlow does have a search by tracked config, but there are no grouping, aggregation, subplotting by hyparparams and other comparison features available.
UI Scalability
- Aim UI can handle several thousands of metrics at the same time smoothly with 1000s of steps. It may get shaky when you explore 1000s of metrics with 10000s of steps each. But we are constantly optimizing!
- MLflow UI becomes slow to use when there are a few hundreds of runs.
Weights and Biases vs Aim
Hosted vs self-hosted
- Weights and Biases is a hosted closed-source MLOps platform.
- Aim is self-hosted, free and open-source experiment tracking tool.
🛣️ Roadmap
Detailed milestones
The Aim product roadmap :sparkle:
- The
Backlogcontains the issues we are going to choose from and prioritize weekly - The issues are mainly prioritized by the highly-requested features
High-level roadmap
The high-level features we are going to work on the next few months:
In progress
- Aim SDK low-level interface
- Dashboards – customizable layouts with embedded explorers
- Ergonomic UI kit
- Text Explorer
Next-up
Aim UI
- Runs management
- Runs explorer – query and visualize runs data(images, audio, distributions, ...) in a central dashboard
- Explorers
- Distributions Explorer
SDK and Storage
- Scalability
- Smooth UI and SDK experience with over 10.000 runs
- Runs management
- CLI commands
- Reporting - runs summary and run details in a CLI compatible format
- Manipulations – copy, move, delete runs, params and sequences
- CLI commands
- Cloud storage support – store runs blob(e.g. images) data on the cloud
- Artifact storage – store files, model checkpoints, and beyond
Integrations
- ML Frameworks:
- Shortlist: scikit-learn
- Resource management tools
- Shortlist: Kubeflow, Slurm
- Workflow orchestration tools
Done
- Live updates (Shipped: Oct 18 2021)
- Images tracking and visualization (Start: Oct 18 2021, Shipped: Nov 19 2021)
- Distributions tracking and visualization (Start: Nov 10 2021, Shipped: Dec 3 2021)
- Jupyter integration (Start: Nov 18 2021, Shipped: Dec 3 2021)
- Audio tracking and visualization (Start: Dec 6 2021, Shipped: Dec 17 2021)
- Transcripts tracking and visualization (Start: Dec 6 2021, Shipped: Dec 17 2021)
- Plotly integration (Start: Dec 1 2021, Shipped: Dec 17 2021)
- Colab integration (Start: Nov 18 2021, Shipped: Dec 17 2021)
- Centralized tracking server (Start: Oct 18 2021, Shipped: Jan 22 2022)
- Tensorboard adaptor - visualize TensorBoard logs with Aim (Start: Dec 17 2021, Shipped: Feb 3 2022)
- Track git info, env vars, CLI arguments, dependencies (Start: Jan 17 2022, Shipped: Feb 3 2022)
- MLFlow adaptor (visualize MLflow logs with Aim) (Start: Feb 14 2022, Shipped: Feb 22 2022)
- Activeloop Hub integration (Start: Feb 14 2022, Shipped: Feb 22 2022)
- PyTorch-Ignite integration (Start: Feb 14 2022, Shipped: Feb 22 2022)
- Run summary and overview info(system params, CLI args, git info, ...) (Start: Feb 14 2022, Shipped: Mar 9 2022)
- Add DVC related metadata into aim run (Start: Mar 7 2022, Shipped: Mar 26 2022)
- Ability to attach notes to Run from UI (Start: Mar 7 2022, Shipped: Apr 29 2022)
- Fairseq integration (Start: Mar 27 2022, Shipped: Mar 29 2022)
- LightGBM integration (Start: Apr 14 2022, Shipped: May 17 2022)
- CatBoost integration (Start: Apr 20 2022, Shipped: May 17 2022)
- Run execution details(display stdout/stderr logs) (Start: Apr 25 2022, Shipped: May 17 2022)
- Long sequences(up to 5M of steps) support (Start: Apr 25 2022, Shipped: Jun 22 2022)
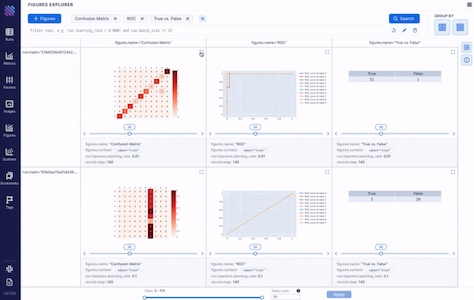
- Figures Explorer (Start: Mar 1 2022, Shipped: Aug 21 2022)
- Notify on stuck runs (Start: Jul 22 2022, Shipped: Aug 21 2022)
- Integration with KerasTuner (Start: Aug 10 2022, Shipped: Aug 21 2022)
- Integration with WandB (Start: Aug 15 2022, Shipped: Aug 21 2022)
- Stable remote tracking server (Start: Jun 15 2022, Shipped: Aug 21 2022)
- Integration with fast.ai (Start: Aug 22 2022, Shipped: Oct 6 2022)
- Integration with MXNet (Start: Sep 20 2022, Shipped: Oct 6 2022)
- Project overview page (Start: Sep 1 2022, Shipped: Oct 6 2022)
- Remote tracking server scaling (Start: Sep 11 2022, Shipped: Nov 26 2022)
- Integration with PaddlePaddle (Start: Oct 2 2022, Shipped: Nov 26 2022)
- Integration with Optuna (Start: Oct 2 2022, Shipped: Nov 26 2022)
- Audios Explorer (Start: Oct 30 2022, Shipped: Nov 26 2022)
- Experiment page (Start: Nov 9 2022, Shipped: Nov 26 2022)
- HuggingFace datasets (Start: Dec 29 2022, Feb 3 2023)
👥 Community
Aim README badge
Add Aim badge to your README, if you've enjoyed using Aim in your work:
[](https://github.com/aimhubio/aim)
Cite Aim in your papers
In case you've found Aim helpful in your research journey, we'd be thrilled if you could acknowledge Aim's contribution:
@software{Arakelyan_Aim_2020,
author = {Arakelyan, Gor and Soghomonyan, Gevorg and {The Aim team}},
doi = {10.5281/zenodo.6536395},
license = {Apache-2.0},
month = {6},
title = {{Aim}},
url = {https://github.com/aimhubio/aim},
version = {3.9.3},
year = {2020}
}
Contributing to Aim
Considering contibuting to Aim? To get started, please take a moment to read the CONTRIBUTING.md guide.
Join Aim contributors by submitting your first pull request. Happy coding! 😊

Made with contrib.rocks.
More questions?
Project details
Release history Release notifications | RSS feed
Download files
Download the file for your platform. If you're not sure which to choose, learn more about installing packages.
Source Distribution
Built Distributions
Filter files by name, interpreter, ABI, and platform.
If you're not sure about the file name format, learn more about wheel file names.
Copy a direct link to the current filters
File details
Details for the file aim-3.29.1.tar.gz.
File metadata
- Download URL: aim-3.29.1.tar.gz
- Upload date:
- Size: 1.7 MB
- Tags: Source
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/6.1.0 CPython/3.10.4
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
30fb70f983844eebd270049206c839e6dc09ce9de500048dc97a7a8b22ed83fb
|
|
| MD5 |
7dd1ed586f01e20ecff04522b3394845
|
|
| BLAKE2b-256 |
da25c825c73ec2f48c93324f631dba6e4cdac3bb60a7fde36e0b916820ae62a5
|
File details
Details for the file aim-3.29.1-cp312-cp312-manylinux_2_28_x86_64.whl.
File metadata
- Download URL: aim-3.29.1-cp312-cp312-manylinux_2_28_x86_64.whl
- Upload date:
- Size: 7.6 MB
- Tags: CPython 3.12, manylinux: glibc 2.28+ x86-64
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/6.1.0 CPython/3.9.22
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
15cea0c63d9a61812229d7140cec04f02117626d1724e10bebe410554f3f7561
|
|
| MD5 |
a72131e736abdab80adedbf9244f5d56
|
|
| BLAKE2b-256 |
bc05a55a86258f3505e0ab53ee81afcc0057d805a1de8d5a66390f75e32aa777
|
File details
Details for the file aim-3.29.1-cp312-cp312-macosx_11_0_arm64.whl.
File metadata
- Download URL: aim-3.29.1-cp312-cp312-macosx_11_0_arm64.whl
- Upload date:
- Size: 2.5 MB
- Tags: CPython 3.12, macOS 11.0+ ARM64
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/6.1.0 CPython/3.12.3
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
8fbb9a7f441721cd4999174d0d6fa1e18470c01dddf2f193e7c3d054543a4ca6
|
|
| MD5 |
659fe7078ab352d07f411f30ea44044c
|
|
| BLAKE2b-256 |
a1a5da5e0de60a8d32ab8b2d725eec2ade3303117697cd714fb1b00134d01a64
|
File details
Details for the file aim-3.29.1-cp312-cp312-macosx_10_14_x86_64.whl.
File metadata
- Download URL: aim-3.29.1-cp312-cp312-macosx_10_14_x86_64.whl
- Upload date:
- Size: 2.5 MB
- Tags: CPython 3.12, macOS 10.14+ x86-64
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/6.1.0 CPython/3.12.3
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
301afdf3e80b3ccac4cdc786a73f81656bd3b1ec73836de19a67a77a0b3d3379
|
|
| MD5 |
5a7e93aa95e6c3fcac0d32cf47db2d3c
|
|
| BLAKE2b-256 |
70074b6c4bda0469fad31a902ff1205ed010b3459be9565a8ffa2bfdcbb1e2bd
|
File details
Details for the file aim-3.29.1-cp311-cp311-manylinux_2_28_x86_64.whl.
File metadata
- Download URL: aim-3.29.1-cp311-cp311-manylinux_2_28_x86_64.whl
- Upload date:
- Size: 7.5 MB
- Tags: CPython 3.11, manylinux: glibc 2.28+ x86-64
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/6.1.0 CPython/3.9.22
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
350e640c3c6bc532e0ad6d5cf6479f82f309a38bf05f84d30947d00a36f94523
|
|
| MD5 |
374cda0b779388f1ebda8c63549ce877
|
|
| BLAKE2b-256 |
8c1906cac7b4d200f337ee451482090cf02553e361595733ba5ee5e701a926fe
|
File details
Details for the file aim-3.29.1-cp311-cp311-manylinux_2_24_x86_64.whl.
File metadata
- Download URL: aim-3.29.1-cp311-cp311-manylinux_2_24_x86_64.whl
- Upload date:
- Size: 5.9 MB
- Tags: CPython 3.11, manylinux: glibc 2.24+ x86-64
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/6.1.0 CPython/3.9.22
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
165dc403cb4f9f04b83977e9fc40c86689e3a3f3bb61341cbe03591a16ec041d
|
|
| MD5 |
ac15074c1454168781349e86cc7e2281
|
|
| BLAKE2b-256 |
b9020bd5126aad71bf0f789cb3c28f534aaef6d92be90f1925e6f5cb63438daf
|
File details
Details for the file aim-3.29.1-cp311-cp311-manylinux_2_17_x86_64.manylinux2014_x86_64.whl.
File metadata
- Download URL: aim-3.29.1-cp311-cp311-manylinux_2_17_x86_64.manylinux2014_x86_64.whl
- Upload date:
- Size: 7.3 MB
- Tags: CPython 3.11, manylinux: glibc 2.17+ x86-64
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/6.1.0 CPython/3.9.22
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
10bb79928b0017043428c227e33ee592b0f34f1f72e65ea94b74eddcc4038fc8
|
|
| MD5 |
2e80c4380b975ce88bf90297a7044ebf
|
|
| BLAKE2b-256 |
96044d523b4c6c19a521558aba8145ff49ab43d6663c95b4bf9905be0e18e2bf
|
File details
Details for the file aim-3.29.1-cp311-cp311-macosx_11_0_arm64.whl.
File metadata
- Download URL: aim-3.29.1-cp311-cp311-macosx_11_0_arm64.whl
- Upload date:
- Size: 2.5 MB
- Tags: CPython 3.11, macOS 11.0+ ARM64
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/6.1.0 CPython/3.11.0
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
ee164cfd5fceda2d751da2b10697e9bb3f64798d928596ee970e2b0891a1e0d0
|
|
| MD5 |
b64430bc4714f4e1643ce40b95aaeef0
|
|
| BLAKE2b-256 |
7a5bf4d949cbd13ccdc8f5ede254d44155fbad1fe05a4cb9d517740439b87efd
|
File details
Details for the file aim-3.29.1-cp311-cp311-macosx_10_14_x86_64.whl.
File metadata
- Download URL: aim-3.29.1-cp311-cp311-macosx_10_14_x86_64.whl
- Upload date:
- Size: 2.5 MB
- Tags: CPython 3.11, macOS 10.14+ x86-64
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/6.1.0 CPython/3.11.0
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
a3fc8557dfb910c3aec784017c00ead65e1aeb5b994f7954de4679d83165d1ab
|
|
| MD5 |
ff4b8688a6b2cefe6098d8f39edad45e
|
|
| BLAKE2b-256 |
d9f4e9a5d8fdb31d61c450492553e18f7aae6a5d5baf266747d99135c53b95c1
|
File details
Details for the file aim-3.29.1-cp310-cp310-manylinux_2_28_x86_64.whl.
File metadata
- Download URL: aim-3.29.1-cp310-cp310-manylinux_2_28_x86_64.whl
- Upload date:
- Size: 7.1 MB
- Tags: CPython 3.10, manylinux: glibc 2.28+ x86-64
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/6.1.0 CPython/3.9.22
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
5d050fb30ac23547d00d505350a805886aee9109d0273231ab8beead8caad22a
|
|
| MD5 |
cfc367667347959f87544c967fb9b647
|
|
| BLAKE2b-256 |
184ec2d570bce3ef83cf3d302dc0694a1167b228c1db03842559ebc5acfae096
|
File details
Details for the file aim-3.29.1-cp310-cp310-manylinux_2_24_x86_64.whl.
File metadata
- Download URL: aim-3.29.1-cp310-cp310-manylinux_2_24_x86_64.whl
- Upload date:
- Size: 5.8 MB
- Tags: CPython 3.10, manylinux: glibc 2.24+ x86-64
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/6.1.0 CPython/3.9.22
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
550b353c1859b7a731a38244775fd5e351c0e42f70e0ced2dbf82e4183197f98
|
|
| MD5 |
3764820bec6077fa0e11a4eb7150b94f
|
|
| BLAKE2b-256 |
934d36193c1149528f25798f4da5616e1b2b2e713ad69eff3958fb0c6decc29b
|
File details
Details for the file aim-3.29.1-cp310-cp310-manylinux_2_17_x86_64.manylinux2014_x86_64.whl.
File metadata
- Download URL: aim-3.29.1-cp310-cp310-manylinux_2_17_x86_64.manylinux2014_x86_64.whl
- Upload date:
- Size: 6.9 MB
- Tags: CPython 3.10, manylinux: glibc 2.17+ x86-64
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/6.1.0 CPython/3.9.22
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
a23bea6db70715246032ba6048f481e9316b9e0a0cfecce718ed6b17773a12e6
|
|
| MD5 |
2f2cc4f05dadee1caa975b7749df0ba9
|
|
| BLAKE2b-256 |
926b17069dd96c51696407c4458dfb29997f9e42649d23f48c8ba9589821d815
|
File details
Details for the file aim-3.29.1-cp310-cp310-macosx_11_0_arm64.whl.
File metadata
- Download URL: aim-3.29.1-cp310-cp310-macosx_11_0_arm64.whl
- Upload date:
- Size: 2.5 MB
- Tags: CPython 3.10, macOS 11.0+ ARM64
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/6.1.0 CPython/3.10.4
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
a7021e85c60549e9cff2b7c8e3642aaa3c7995c8778151c45fac021933277b68
|
|
| MD5 |
13944fc2dd08e69edc264a8a554acbe3
|
|
| BLAKE2b-256 |
d866d8490874059a2d909a0f9a8aaad18dcda483283ca87e76c797b0910830ee
|
File details
Details for the file aim-3.29.1-cp310-cp310-macosx_10_14_x86_64.whl.
File metadata
- Download URL: aim-3.29.1-cp310-cp310-macosx_10_14_x86_64.whl
- Upload date:
- Size: 2.6 MB
- Tags: CPython 3.10, macOS 10.14+ x86-64
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/6.1.0 CPython/3.10.4
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
2604793a69c2ec17aa915a5fe0fecb526923c3a2f056c9ba5ab6a482272abb49
|
|
| MD5 |
a480a0c5b295bc921cbd02c0e1b25dbe
|
|
| BLAKE2b-256 |
c982a8959bbea98dd94831e17f7845ea0487c371b0d51a6609bd291dea6988d6
|
File details
Details for the file aim-3.29.1-cp39-cp39-manylinux_2_28_x86_64.whl.
File metadata
- Download URL: aim-3.29.1-cp39-cp39-manylinux_2_28_x86_64.whl
- Upload date:
- Size: 7.1 MB
- Tags: CPython 3.9, manylinux: glibc 2.28+ x86-64
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/6.1.0 CPython/3.9.22
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
523aeece8230be931dafdb204e1e7205e8b6669aa116a4964102b55dd526ef0e
|
|
| MD5 |
f3f486b146bd3ae0f82c64bb13fa889d
|
|
| BLAKE2b-256 |
a0427c9f642e17bde1f8437d930198d03b8dd5c8176187a3acbbc8e70606f32b
|
File details
Details for the file aim-3.29.1-cp39-cp39-manylinux_2_24_x86_64.whl.
File metadata
- Download URL: aim-3.29.1-cp39-cp39-manylinux_2_24_x86_64.whl
- Upload date:
- Size: 5.8 MB
- Tags: CPython 3.9, manylinux: glibc 2.24+ x86-64
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/6.1.0 CPython/3.9.22
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
865302bf14ad3a37df6c6221580bb8d766e3ddedc54980e94ffc1726d47a1dd3
|
|
| MD5 |
945e28a72338eb898557e1f0cfd0f2bc
|
|
| BLAKE2b-256 |
0171510e483a16692aaec5438fc1b8823fe609e5210b1e1240ed8d18a58755ff
|
File details
Details for the file aim-3.29.1-cp39-cp39-manylinux_2_17_x86_64.manylinux2014_x86_64.whl.
File metadata
- Download URL: aim-3.29.1-cp39-cp39-manylinux_2_17_x86_64.manylinux2014_x86_64.whl
- Upload date:
- Size: 6.9 MB
- Tags: CPython 3.9, manylinux: glibc 2.17+ x86-64
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/6.1.0 CPython/3.9.22
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
8d0d5e93ed240f177e4662a03c121748e6b0002b012121c472fb7b157dff439b
|
|
| MD5 |
781eab95762177ae19283871f69855e3
|
|
| BLAKE2b-256 |
f881f148ddbc671fd8babd763caa476e517aeacc6d11b5ce063aa4e635bd682d
|
File details
Details for the file aim-3.29.1-cp39-cp39-macosx_11_0_arm64.whl.
File metadata
- Download URL: aim-3.29.1-cp39-cp39-macosx_11_0_arm64.whl
- Upload date:
- Size: 2.5 MB
- Tags: CPython 3.9, macOS 11.0+ ARM64
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/6.1.0 CPython/3.9.12
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
d641aec8f4f6660b77e6f43a4f4ded9c4a05220644ca5583ad66835c291c50a6
|
|
| MD5 |
36b56bec105f557639a4bfb1caad7ee3
|
|
| BLAKE2b-256 |
2193f433de267bdfbc3dd9dac34a6de39b71ea3954b4efff6ec105bc5119a415
|
File details
Details for the file aim-3.29.1-cp39-cp39-macosx_10_14_x86_64.whl.
File metadata
- Download URL: aim-3.29.1-cp39-cp39-macosx_10_14_x86_64.whl
- Upload date:
- Size: 2.5 MB
- Tags: CPython 3.9, macOS 10.14+ x86-64
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/6.1.0 CPython/3.9.12
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
173b3bae573775c9ab9e582ca4a08d5292d0f1709725e0e12c1e4d443a280df0
|
|
| MD5 |
91cd8435cddaed42a289e1b7624cb331
|
|
| BLAKE2b-256 |
96de71cb6614ec407238ae88635a03ebc058ab4262171f494f002cdf13c0bc56
|
File details
Details for the file aim-3.29.1-cp38-cp38-manylinux_2_28_x86_64.whl.
File metadata
- Download URL: aim-3.29.1-cp38-cp38-manylinux_2_28_x86_64.whl
- Upload date:
- Size: 7.2 MB
- Tags: CPython 3.8, manylinux: glibc 2.28+ x86-64
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/6.1.0 CPython/3.9.22
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
54cff7964a699bd717c2fd011991388acdb7bd5e0b4e749e9e81fed08191c345
|
|
| MD5 |
3aa8e623ce5cc1b9edced972bd48cddf
|
|
| BLAKE2b-256 |
a75b7a4ad95fc10a5455812f5a2225dbbe7a8b0590075ea0a28f3c80bf5978bf
|
File details
Details for the file aim-3.29.1-cp38-cp38-manylinux_2_24_x86_64.whl.
File metadata
- Download URL: aim-3.29.1-cp38-cp38-manylinux_2_24_x86_64.whl
- Upload date:
- Size: 6.1 MB
- Tags: CPython 3.8, manylinux: glibc 2.24+ x86-64
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/6.1.0 CPython/3.9.22
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
8316b82f95ac0fc6e2ef11b96e981315c2ffc48e0dda2b42088edbfe56a31ad3
|
|
| MD5 |
06a0c3a5b4ea9edafd56dd0fb872ccd8
|
|
| BLAKE2b-256 |
d92578f67da743a119f4a552364ce808d7b10c50af7a1868eaaa1483f73bc68a
|
File details
Details for the file aim-3.29.1-cp38-cp38-manylinux_2_17_x86_64.manylinux2014_x86_64.whl.
File metadata
- Download URL: aim-3.29.1-cp38-cp38-manylinux_2_17_x86_64.manylinux2014_x86_64.whl
- Upload date:
- Size: 7.0 MB
- Tags: CPython 3.8, manylinux: glibc 2.17+ x86-64
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/6.1.0 CPython/3.9.22
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
20ae069d2d86785c28a2a29c6bf2c0d9233adb2e61d0c286dead72b66a549035
|
|
| MD5 |
d47f713a2b4f140b76e9a0ef40c50afa
|
|
| BLAKE2b-256 |
9558df5f18e9603975155d287baeeabb2e15ce30a13565848745063f15b88a8b
|
File details
Details for the file aim-3.29.1-cp38-cp38-macosx_11_0_arm64.whl.
File metadata
- Download URL: aim-3.29.1-cp38-cp38-macosx_11_0_arm64.whl
- Upload date:
- Size: 2.5 MB
- Tags: CPython 3.8, macOS 11.0+ ARM64
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/4.0.0 CPython/3.8.13
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
d66ad784482d9830b83f4b1b63b8cac34cf783c8c2d283bf3508b502820edd21
|
|
| MD5 |
88ec6ecd7a3c6e2277693f1e1c382123
|
|
| BLAKE2b-256 |
5d0cd2e568304daa0eacf2b7c227d5f559fd1ed20c5f70ff707a9e5840b9ad36
|
File details
Details for the file aim-3.29.1-cp38-cp38-macosx_10_14_x86_64.whl.
File metadata
- Download URL: aim-3.29.1-cp38-cp38-macosx_10_14_x86_64.whl
- Upload date:
- Size: 2.6 MB
- Tags: CPython 3.8, macOS 10.14+ x86-64
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/4.0.0 CPython/3.8.13
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
4c094bace9baa961baa455714a69efe3bc2b64bb52c4510ff9ab3f52621c3442
|
|
| MD5 |
9031d02adca556a7499aaffc6ddb8bce
|
|
| BLAKE2b-256 |
9b2c145fdd5d3f798a73899971d16cc8aa3e718eaa698d7f397edcd9161f335a
|
File details
Details for the file aim-3.29.1-cp37-cp37m-manylinux_2_24_x86_64.whl.
File metadata
- Download URL: aim-3.29.1-cp37-cp37m-manylinux_2_24_x86_64.whl
- Upload date:
- Size: 5.7 MB
- Tags: CPython 3.7m, manylinux: glibc 2.24+ x86-64
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/6.1.0 CPython/3.9.22
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
b9deb6565ab4da74ba398ae0fc593a95ca4a73b07f0683873ee017b1b6ee5612
|
|
| MD5 |
b697185ce9929d8bf474e9db287d5da7
|
|
| BLAKE2b-256 |
17b95880b7dcd40ff76efef8f8513ac1b17bd99323db290c54fa10bde80a01e0
|
File details
Details for the file aim-3.29.1-cp37-cp37m-macosx_10_14_x86_64.whl.
File metadata
- Download URL: aim-3.29.1-cp37-cp37m-macosx_10_14_x86_64.whl
- Upload date:
- Size: 2.6 MB
- Tags: CPython 3.7m, macOS 10.14+ x86-64
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/4.0.0 CPython/3.7.13
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
1ad020bccec43c597e8137b4766d0289c4acbc19118e85b0ba39c0d0c0e740b3
|
|
| MD5 |
c04e8322ebe34bbab6773ea7a68495a3
|
|
| BLAKE2b-256 |
1a15abd52bd51d2fc458e618f5c6709ed58efca60b9e45b15987744a83618adc
|























