Execute commands interactively on remote Windows machines using the WinRM protocol
Project description
evil-winrm-py
evil-winrm-py is a python-based tool for executing commands on remote Windows machines using the WinRM (Windows Remote Management) protocol. It provides an interactive shell.
[!NOTE] This tool is designed strictly for educational, ethical use, and authorized penetration testing. Always ensure you have explicit authorization before accessing any system. Unauthorized access or misuse of this tool is both illegal and unethical.
Motivation
The original evil-winrm is written in Ruby, which can be a hurdle for some users. Rewriting it in Python makes it more accessible and easier to use, while also allowing us to leverage Python’s rich ecosystem for added features and flexibility.
I also wanted to learn more about winrm and its internals, so this project will also serve as a learning experience for me.
Features
- Execute commands on remote Windows machines via an interactive shell.
- Support for NTLM authentication.
- Support for Pass-the-Hash authentication.
- Support for Certificate authentication.
- Support for Kerberos authentication with SPN (Service Principal Name) prefix and hostname options.
- Support for SSL to secure communication with the remote host.
- Support for custom WSMan URIs.
- Download files from the remote host to the local machine.
- Auto-complete remote file and directory paths.
- Enable logging and debugging for better traceability.
- Navigate command history using up/down arrow keys.
- Display colorized output for improved readability..
- Lightweight and Python-based for ease of use.
- Keyboard Interrupt (Ctrl+C) support to terminate long-running commands gracefully.
Installation (Windows/Linux)
Installation of Kerberos prerequisites on Linux
sudo apt install gcc python3-dev libkrb5-dev
# Optional: krb5-user
Install evil-winrm-py
You may use pipx or uv instead of pip to install evil-winrm-py.
pipx/uvis a tool to install and run Python applications in isolated environments, which helps prevent dependency conflicts by keeping the tool's dependencies separate from your system's Python packages.
pip install evil-winrm-py
pip install evil-winrm-py[kerberos] # for kerberos support on Linux
or if you want to install with latest commit from the main branch you can do so by cloning the repository and installing it with pip/pipx/uv:
git clone https://github.com/adityatelange/evil-winrm-py
cd evil-winrm-py
pip install .
Update
pip install --upgrade evil-winrm-py
Uninstall
pip uninstall evil-winrm-py
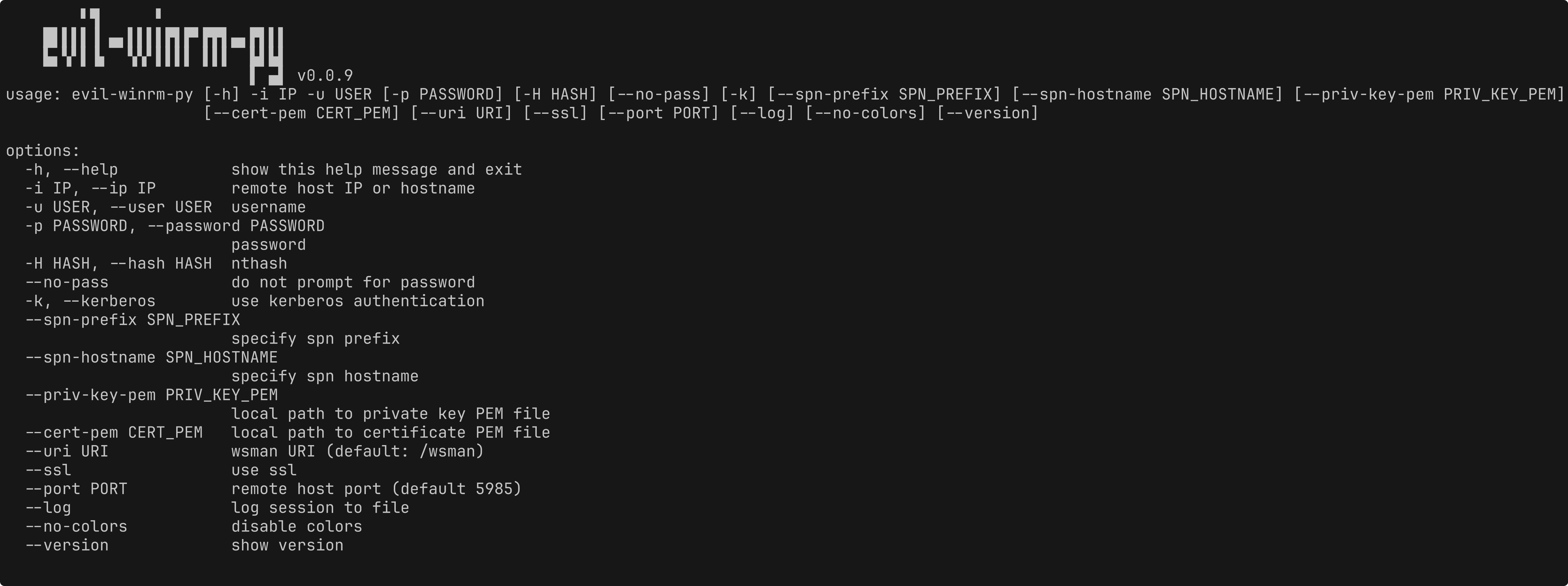
Usage
usage: evil-winrm-py [-h] -i IP -u USER [-p PASSWORD] [-H HASH] [--no-pass] [-k] [--spn-prefix SPN_PREFIX] [--spn-hostname SPN_HOSTNAME] [--priv-key-pem PRIV_KEY_PEM]
[--cert-pem CERT_PEM] [--uri URI] [--ssl] [--port PORT] [--log] [--no-colors] [--version]
options:
-h, --help show this help message and exit
-i IP, --ip IP remote host IP or hostname
-u USER, --user USER username
-p PASSWORD, --password PASSWORD
password
-H HASH, --hash HASH nthash
--no-pass do not prompt for password
-k, --kerberos use kerberos authentication
--spn-prefix SPN_PREFIX
specify spn prefix
--spn-hostname SPN_HOSTNAME
specify spn hostname
--priv-key-pem PRIV_KEY_PEM
local path to private key PEM file
--cert-pem CERT_PEM local path to certificate PEM file
--uri URI wsman URI (default: /wsman)
--ssl use ssl
--port PORT remote host port (default 5985)
--log log session to file
--no-colors disable colors
--version show version
Example:
evil-winrm-py -i 192.168.1.100 -u Administrator -p P@ssw0rd --ssl
Credits
- Original evil-winrm project - https://github.com/Hackplayers/evil-winrm
- PowerShell Remoting Protocol for Python - https://github.com/jborean93/pypsrp
- Prompt Toolkit - https://github.com/prompt-toolkit/python-prompt-toolkit
- tqdm - https://github.com/tqdm/tqdm
- Thanks to Github Coplilot and Google Gemini for code suggestions and improvements.
Project details
Release history Release notifications | RSS feed
Download files
Download the file for your platform. If you're not sure which to choose, learn more about installing packages.
Source Distribution
Built Distribution
Filter files by name, interpreter, ABI, and platform.
If you're not sure about the file name format, learn more about wheel file names.
Copy a direct link to the current filters
File details
Details for the file evil_winrm_py-0.0.9.tar.gz.
File metadata
- Download URL: evil_winrm_py-0.0.9.tar.gz
- Upload date:
- Size: 14.9 kB
- Tags: Source
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/6.1.0 CPython/3.12.3
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
a48966b649b9771a4f3cf4599666aa6cfefff0f19504df7b9809e876fbed5f8c
|
|
| MD5 |
36d95bad2dd8d4ea2ee7450767c5b67c
|
|
| BLAKE2b-256 |
a04d3faf728b2ca14bd70af6718bc5e957cb331bfec94bde301cca076ac9fa1b
|
File details
Details for the file evil_winrm_py-0.0.9-py3-none-any.whl.
File metadata
- Download URL: evil_winrm_py-0.0.9-py3-none-any.whl
- Upload date:
- Size: 13.5 kB
- Tags: Python 3
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/6.1.0 CPython/3.12.3
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
abf08f7ece0b7b52b196278bb2db6087b288e0e52d944e56956d8e1a1b712a7a
|
|
| MD5 |
c43c08fb170cc3a00818bf4600fcf7fb
|
|
| BLAKE2b-256 |
f0a3dd05c2bb559f5208d593d18ca197bd19c407fa2b9e5f5d2c16491760998b
|