Fast elliptic curve digital signatures
Project description



About
This is a python package for doing fast elliptic curve cryptography, specifically digital signatures.
Security
I am not aware of any current issues. There is no nonce reuse, no branching on secret material, and all points are validated before any operations are performed on them. Timing side challenges are mitigated via Montgomery point multiplication. Nonces are generated per RFC6979. That being said crypto is tricky and I’m not beyond making mistakes. Please use a more established and reviewed library for security critical applications. Open an issue or email me if you see any seurity issue or risk with this library.
Python Versions Supported
The initial release of this package was targeted at python2.7. Earlier versions may work but have no guarantee of correctness or stability. As of release 1.2.1+ python3 is now supported as well.
Supported Primitives
Curves over Prime Fields
P192 (
fastecdsa.curve.P192)P224 (
fastecdsa.curve.P224)P256 (
fastecdsa.curve.P256)P384 (
fastecdsa.curve.P384)P521 (
fastecdsa.curve.P521)secp256k1 (bitcoin curve) (
fastecdsa.curve.secp256k1)
Curves over Binary Fields
K163 (
fastecdsa.curve.K163)K233 (
fastecdsa.curve.K233)K283 (
fastecdsa.curve.K283)K409 (
fastecdsa.curve.K409)K571 (
fastecdsa.curve.K571)
Hash Functions
Any hash function in the hashlib module (md5, sha1, sha224, sha256, sha384, sha512)
will work, as will any hash function that implements the same interface / core functionality as the
those in hashlib. For instance, if you wish to use SHA3 as the hash function the
pysha3 package will work with this library as long as it is at version >=1.0b1 (as previous
versions didn’t work with the hmac module which is used in nonce generation).
Performance
Curves over Prime Fields
Currently it does basic point multiplication significantly faster than the ecdsa
package. You can see the times for 1,000 signature and verification operations below,
fast.py corresponding to this package and regular.py corresponding
to ecdsa package.
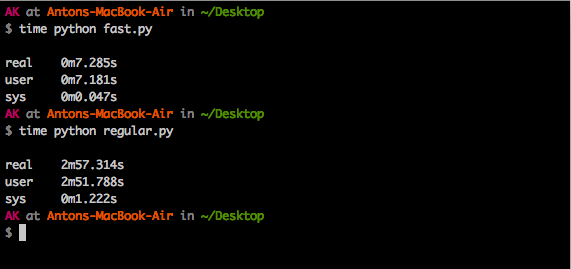
As you can see, this package in this case is ~25x faster.
Curves over Binary Fields
Curves over binary fields are slower. This is mainly because there are no good C libraries that I could find optimized for binary fields (e.g. FLINT only supports polynomials in a field of arbitrary characteristic, which means no optimizations and more cases than we need for binary fields). So the binary field C code is written by me. Finding the inverse of a polynomial is the main bottleneck currently taking about 50ms (for comparison, signature generation and verification in prime fields are both <5ms). This will be improved when I have time to optimize (or feel free to fork and optimize the code).
Installing
You can use pip: $ pip install fastecdsa or clone the repo and use
$ python setup.py install. Note that you need to have a C compiler.
You also need to have GMP on your system as the underlying
C code in this package includes the gmp.h header (and links against gmp
via the -lgmp flag). On debian you can install all dependencies as follows:
$ sudo apt-get install python-dev libgmp3-devUsage
Generating Keys
You can use this package to generate keys if you like. Recall that private keys on elliptic curves are integers, and public keys are points i.e. integer pairs.
from fastecdsa import keys, curve
# generate a private key for curve P256
priv_key = keys.gen_private_key(curve.P256)
# get the public key corresponding to the private key we just generated
pub_key = keys.get_public_key(priv_key, curve.P256)
(Qx, Qy) = pub_key # recall that pub_key is simply an integer pairSigning and Verifying
Some basic usage is shown below:
from fastecdsa import curve, ecdsa, keys
from hashlib import sha384
m = "a message to sign via ECDSA" # some message
''' use default curve and hash function (P256 and SHA2) '''
private_key = keys.gen_private_key(curve.P256)
public_key = keys.get_public_key(private_key, curve.P256)
# standard signature, returns two integers
r, s = ecdsa.sign(m, private_key)
# should return True as the signature we just generated is valid.
valid = ecdsa.verify((r, s), m, public_key)
''' specify a different hash function to use with ECDSA '''
r, s = ecdsa.sign(m, private_key, hashfunc=sha384)
valid = ecdsa.verify((r, s), m, public_key, hashfunc=sha384)
''' specify a different curve to use with ECDSA '''
private_key = keys.gen_private_key(curve.P224)
public_key = keys.get_public_key(private_key, curve.P224)
r, s = ecdsa.sign(m, private_key, curve=curve.P224)
valid = ecdsa.verify((r, s), m, public_key, curve=curve.P224)
''' using SHA3 via pysha3>=1.0b1 package '''
import sha3 # pip install [--user] pysha3==1.0b1
from hashlib import sha3_256
private_key, public_key = keys.gen_keypair(curve.P256)
r, s = ecdsa.sign(m, private_key, hashfunc=sha3_256)
valid = ecdsa.verify((r, s), m, public_key, hashfunc=sha3_256)Project details
Release history Release notifications | RSS feed
Download files
Download the file for your platform. If you're not sure which to choose, learn more about installing packages.
Source Distribution
File details
Details for the file fastecdsa-1.3.2.tar.gz.
File metadata
- Download URL: fastecdsa-1.3.2.tar.gz
- Upload date:
- Size: 24.9 kB
- Tags: Source
- Uploaded using Trusted Publishing? No
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
7230ae3787184c5ffcbb4be3879aa5dfe0d74435e9f0506a0940146ca3f88cd6
|
|
| MD5 |
84dfb79a5f1758169b6678be0671fe84
|
|
| BLAKE2b-256 |
6f71ec11ac5b3333453da0610201b5bce082f7a0d1c822b170bc6a1c91fa895a
|











