Kekkai monorepo (local-first AppSec orchestration + compliance checker)
Project description

Security orchestration at developer speed.
One tool for the entire AppSec lifecycle: Predict, Detect, Triage, Manage.



Kekkai
Stop juggling security tools. Kekkai orchestrates your entire AppSec lifecycle — from AI-powered threat modeling to vulnerability management — in a single CLI.
The Five Pillars
| Pillar | Feature | Command | Description |
|---|---|---|---|
| 🔮 Predict | AI Threat Modeling | kekkai threatflow |
Generate STRIDE threat models before writing code |
| 🔍 Detect | Unified Scanning | kekkai scan |
Run Trivy, Semgrep, Gitleaks in isolated containers |
| ✅ Triage | Interactive Review | kekkai triage |
Review findings in a terminal UI, mark false positives |
| 🚦 Gate | CI/CD Policy | kekkai scan --ci |
Break builds on severity thresholds |
| 📊 Manage | DefectDojo | kekkai dojo up |
Spin up vulnerability management in 60 seconds |
Quick Start (60 Seconds)
1. Install
pipx install kekkai-cli
2. Predict (Threat Model)
kekkai threatflow --repo . --model-mode local
# Generates THREATS.md with STRIDE analysis and Data Flow Diagram
3. Detect (Scan)
kekkai scan
# Runs Trivy (CVEs), Semgrep (code), Gitleaks (secrets)
# Outputs unified kekkai-report.json
4. Triage (Review)
kekkai triage
# Interactive TUI to accept, reject, or ignore findings
5. Manage (DefectDojo)
kekkai dojo up --wait
kekkai upload
# Full vulnerability management platform + automated import
Why Kekkai?
| Capability | Manual Approach | Kekkai |
|---|---|---|
| Tooling | Install/update 5+ tools individually | One binary, auto-pulls scanner containers |
| Output | Parse 5 different JSON formats | Unified kekkai-report.json |
| Threat Modeling | Expensive consultants or whiteboarding | AI-generated THREATS.md locally |
| DefectDojo | 200-line docker-compose + debugging | kekkai dojo up (one command) |
| Triage | Read JSON files manually | Interactive terminal UI |
| CI/CD | Complex bash scripts | kekkai scan --ci --fail-on high |
| PR Feedback | Manual security review comments | Auto-comments on GitHub PRs |
Feature Deep Dives
🔮 ThreatFlow — AI-Powered Threat Modeling
Generate STRIDE-aligned threat models and Mermaid.js Data Flow Diagrams from your codebase.
# Ollama (recommended - easy setup, privacy-preserving)
ollama pull mistral
kekkai threatflow --repo . --model-mode ollama --model-name mistral
# Local GGUF model (requires llama-cpp-python)
kekkai threatflow --repo . --model-mode local --model-path ./mistral-7b.gguf
# Remote API (faster, requires API key)
export KEKKAI_THREATFLOW_API_KEY="sk-..."
kekkai threatflow --repo . --model-mode openai
Output: THREATS.md containing:
- Attack surface analysis
- STRIDE threat classification
- Mermaid.js architecture diagram
- Recommended mitigations
Full ThreatFlow Documentation →
🔍 Unified Scanning
Run industry-standard scanners without installing them individually. Each scanner runs in an isolated Docker container with security hardening.
kekkai scan # Scan current directory
kekkai scan --repo /path/to/project # Scan specific path
kekkai scan --output results.json # Custom output path
Scanners Included:
| Scanner | Finds | Image |
|---|---|---|
| Trivy | CVEs in dependencies | aquasec/trivy:latest |
| Semgrep | Code vulnerabilities | semgrep/semgrep:latest |
| Gitleaks | Hardcoded secrets | zricethezav/gitleaks:latest |
Container Security:
- Read-only filesystem
- No network access
- Memory limited (2GB)
- No privilege escalation
✅ Interactive Triage TUI
Stop reading JSON. Review security findings in your terminal.
kekkai triage
Features:
- Navigate findings with keyboard
- Mark as: Accept, Reject, False Positive, Ignore
- Filter by severity, scanner, or status
- Persist decisions in
.kekkai-ignore - Export triaged results
🚦 CI/CD Policy Gate
Automate security enforcement in your pipelines.
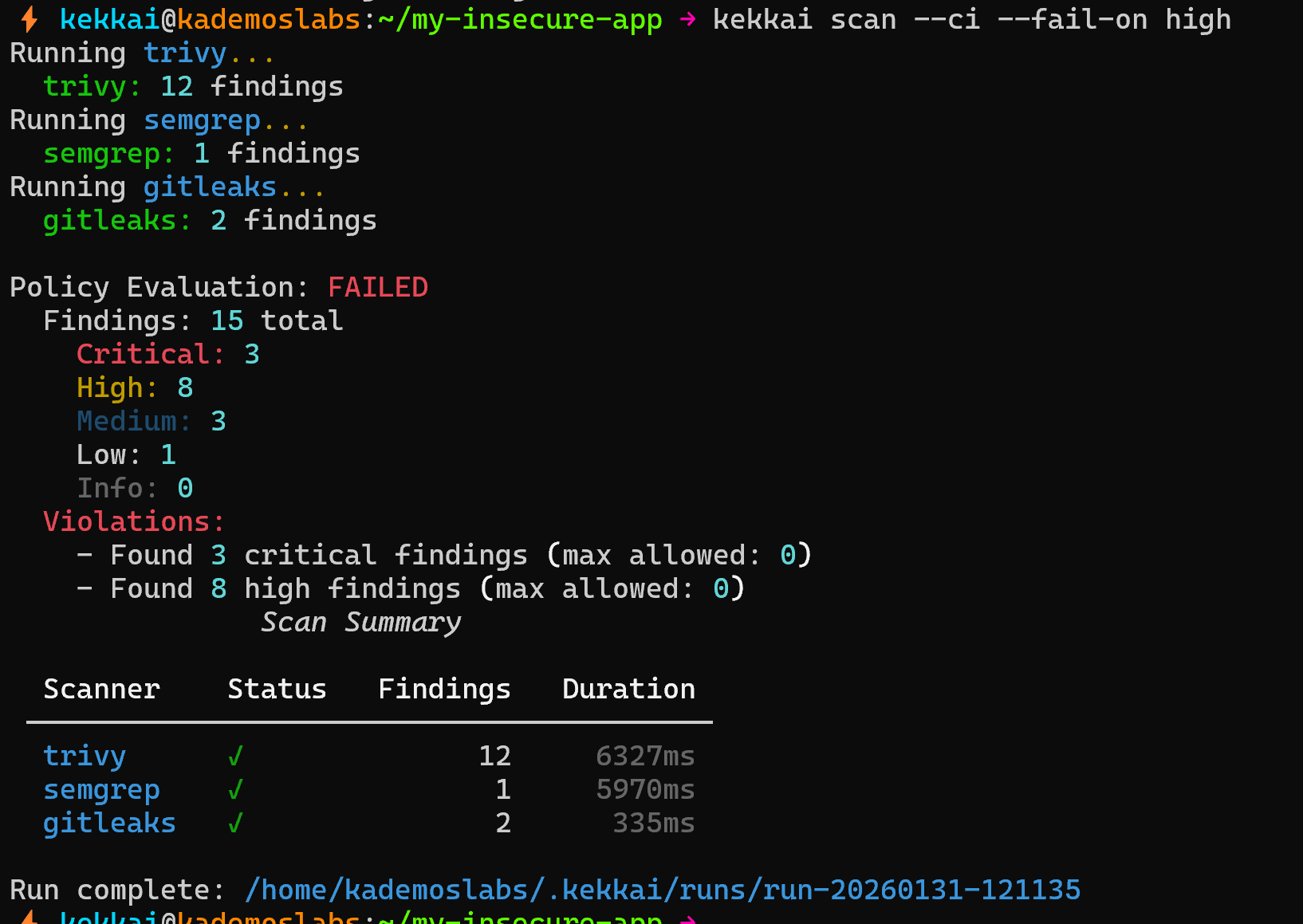
# Fail on any critical or high findings
kekkai scan --ci --fail-on high
# Fail only on critical
kekkai scan --ci --fail-on critical
# Custom threshold: fail on 5+ medium findings
kekkai scan --ci --fail-on medium --max-findings 5
Exit Codes:
| Code | Meaning |
|---|---|
| 0 | No findings above threshold |
| 1 | Findings exceed threshold |
| 2 | Scanner error |
GitHub Actions Example:
- name: Security Scan
run: |
pipx install kekkai-cli
kekkai scan --ci --fail-on high
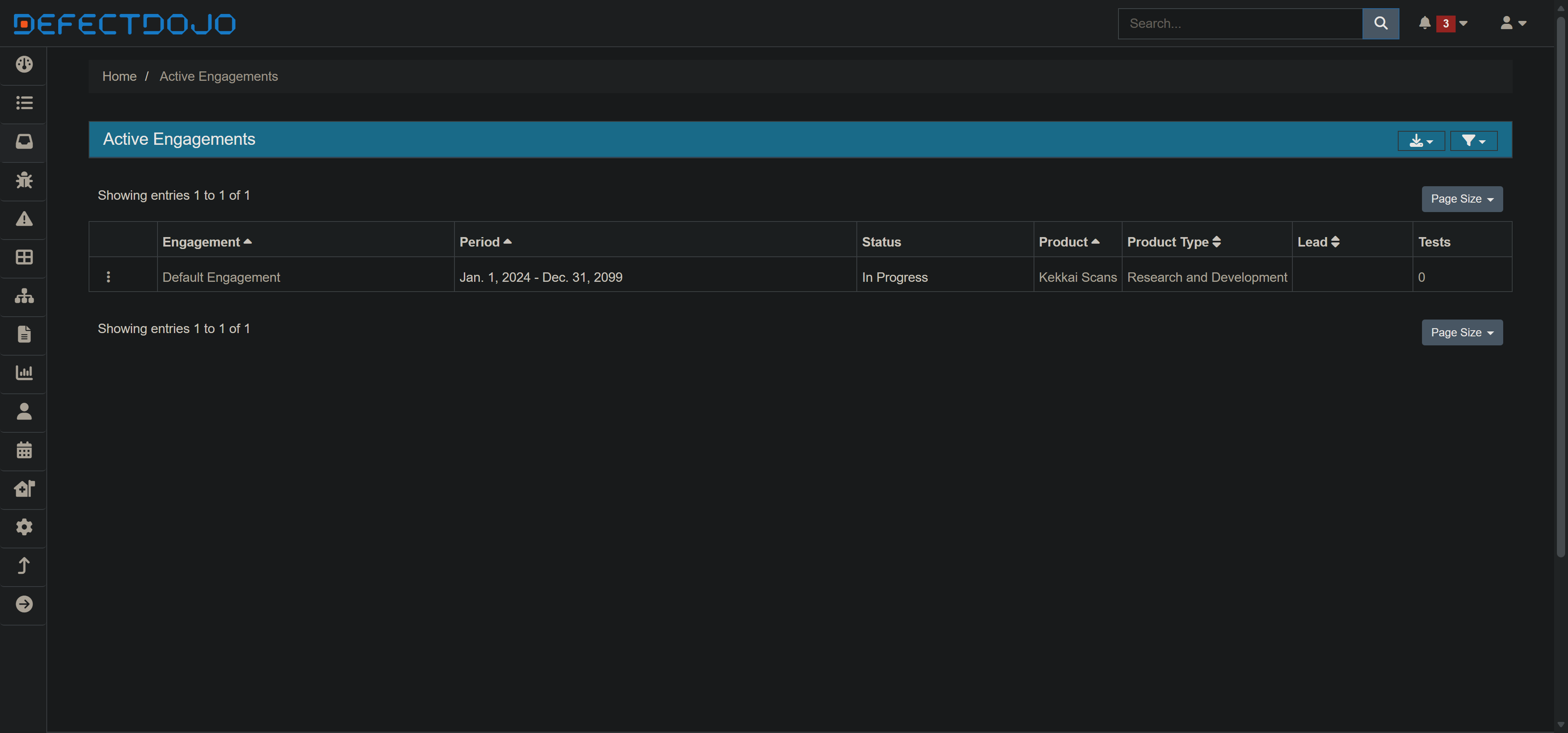
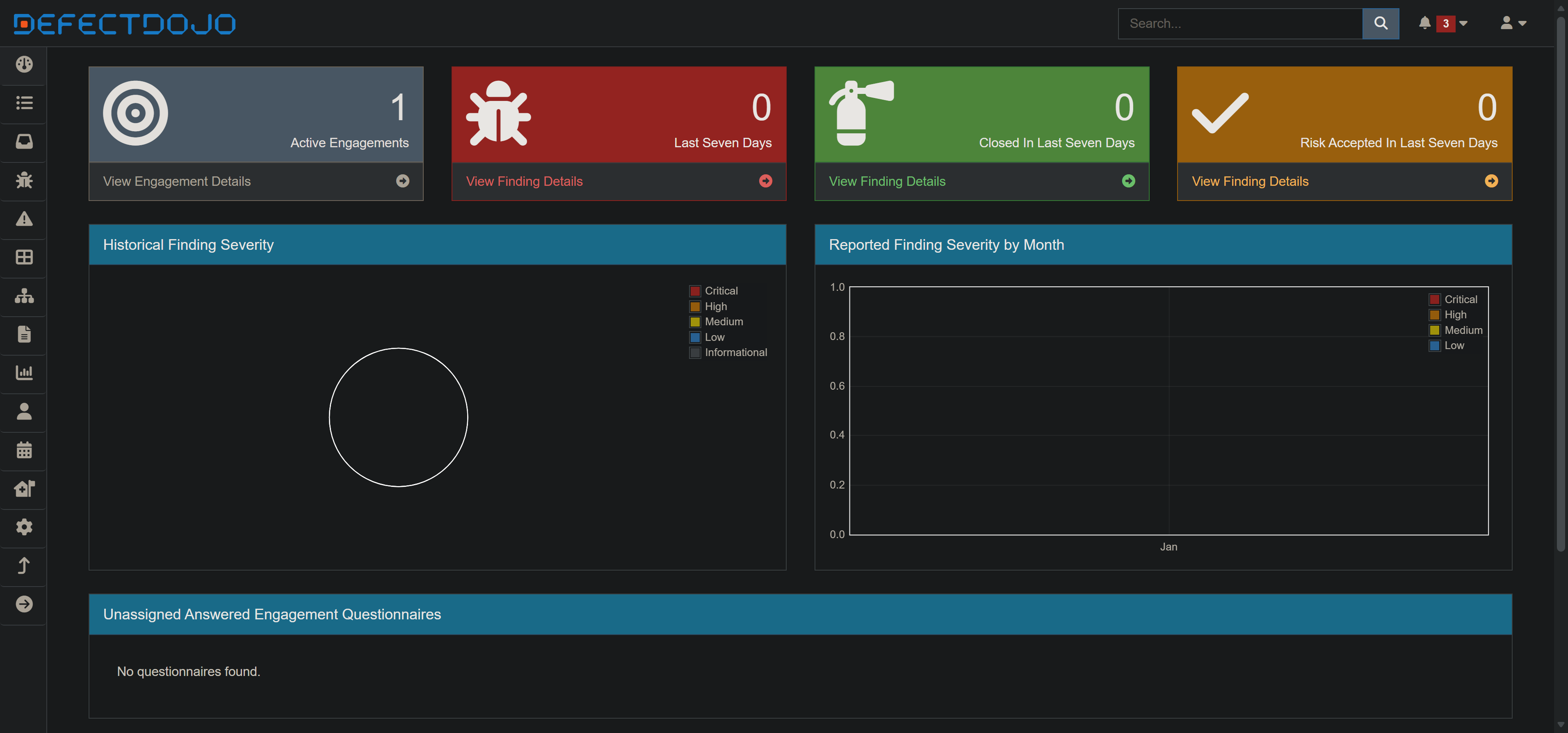
📊 DefectDojo Integration
Spin up a complete vulnerability management platform locally.
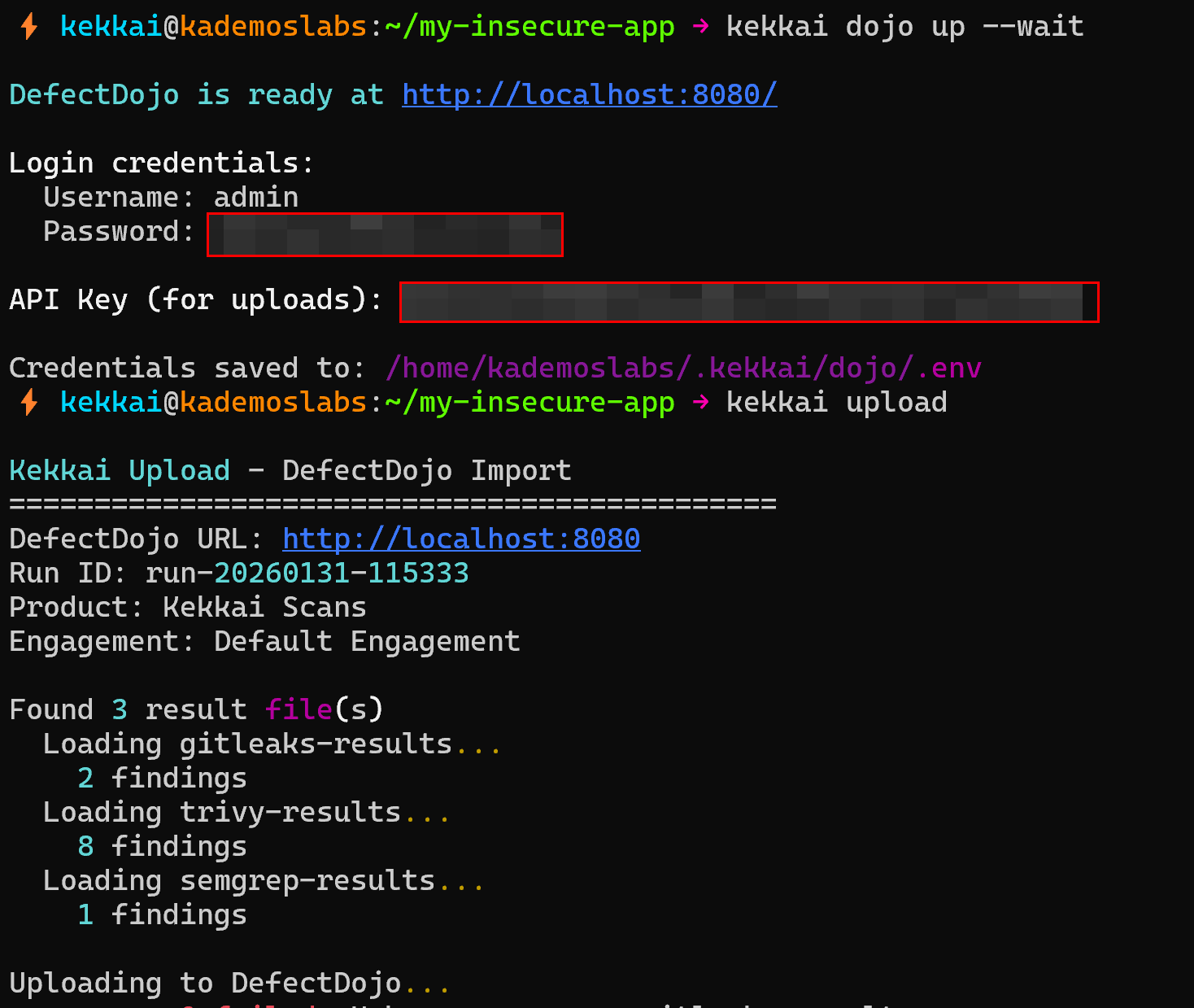
kekkai dojo up --wait # Start DefectDojo (Nginx, Postgres, Redis, Celery)
kekkai dojo status # Check service health
kekkai upload # Import scan results
kekkai dojo down # Stop and clean up (removes volumes)
What You Get:
- DefectDojo web UI at
http://localhost:8080 - Automatic credential generation
- Pre-configured for Kekkai imports
- Clean teardown (no orphaned volumes)
🔔 GitHub PR Comments
Get security feedback directly in pull requests.
export GITHUB_TOKEN="ghp_..."
kekkai scan --github-comment
Kekkai will:
- Run all scanners
- Post findings as PR review comments
- Annotate specific lines with inline comments
Installation
pipx (Recommended)
Isolated environment, no conflicts with system Python.
pipx install kekkai-cli
Homebrew (macOS/Linux)
brew install kademoslabs/tap/kekkai
Scoop (Windows)
scoop bucket add kademoslabs https://github.com/kademoslabs/scoop-bucket
scoop install kekkai
Docker (No Python Required)
docker pull kademoslabs/kekkai:latest
alias kekkai='docker run --rm -v "$(pwd):/repo" kademoslabs/kekkai:latest'
pip (Traditional)
pip install kekkai-cli
Enterprise Features
For organizations that need advanced capabilities, Kekkai Enterprise provides:
| Feature | Description |
|---|---|
| Multi-Tenant Portal | Web dashboard for managing multiple teams/projects (Learn More) |
| SAML 2.0 SSO | Integrate with Okta, Azure AD, Google Workspace |
| Role-Based Access Control | Fine-grained permissions per team/project |
| Advanced Operations | Automated backup/restore, monitoring, zero-downtime upgrades (Learn More) |
| Compliance Reporting | Map findings to OWASP, PCI-DSS, HIPAA, SOC 2 |
| Audit Logging | Cryptographically signed compliance trails |
Architecture:
- Open-source CLI remains fully functional standalone
- Enterprise features available in separate private repository for licensed customers
- Optional integration: CLI can sync results to enterprise portal
- Self-hosted or Kademos-managed deployment options
Contact us for enterprise access →
Security
Kekkai is designed with security as a core principle:
- Container Isolation: Scanners run in hardened Docker containers
- No Network Access: Containers cannot reach external networks
- Local-First AI: ThreatFlow can run entirely on your machine
- SLSA Level 3: Release artifacts include provenance attestations
- Signed Images: Docker images are Cosign-signed
For vulnerability reports, see SECURITY.md.
Documentation
| Guide | Description |
|---|---|
| Installation | All installation methods |
| ThreatFlow | AI threat modeling setup |
| Dojo Quick Start | DefectDojo in 5 minutes |
| CI Mode | Pipeline integration |
| Portal | Enterprise features overview |
| Portal SSO | SAML 2.0 SSO configuration |
| Portal RBAC | Role-based access control |
| Portal Deployment | Self-hosted deployment |
| Security | SLSA provenance verification |
CI/CD Status
Contributing
We welcome contributions! See CONTRIBUTING.md for guidelines.
License
Apache-2.0 — See LICENSE for details.
Built by Kademos Labs
Project details
Release history Release notifications | RSS feed
Download files
Download the file for your platform. If you're not sure which to choose, learn more about installing packages.
Source Distribution
Built Distribution
Filter files by name, interpreter, ABI, and platform.
If you're not sure about the file name format, learn more about wheel file names.
Copy a direct link to the current filters
File details
Details for the file kekkai_cli-1.1.1.tar.gz.
File metadata
- Download URL: kekkai_cli-1.1.1.tar.gz
- Upload date:
- Size: 201.7 kB
- Tags: Source
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/6.2.0 CPython/3.12.12
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
b7cbcd9d0cce9410319d83d83109fd61d4f661ee94f43fe25a686fa9f9791f4f
|
|
| MD5 |
68749b17e25208ba9aee9b9d7fe10db9
|
|
| BLAKE2b-256 |
7a5a1a4432762f48809b4f8be195db72ea64873233827d1074509021ad371d0b
|
File details
Details for the file kekkai_cli-1.1.1-py3-none-any.whl.
File metadata
- Download URL: kekkai_cli-1.1.1-py3-none-any.whl
- Upload date:
- Size: 186.2 kB
- Tags: Python 3
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/6.2.0 CPython/3.12.12
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
f954b9197445a690c72e8c4c04d78d36d62967ba6c62837bffc100d02bb3a508
|
|
| MD5 |
2bd99b18c040d7a37f37544ac34ecd94
|
|
| BLAKE2b-256 |
6ac6613c086697b3086c95872b44c45321e04884c63cc5c214506ce90664c1ad
|