Terminal UI for Trivy/Semgrep/Gitleaks. Local-first security triage.
Project description

Interactive security triage in the terminal.



Kekkai
Stop parsing JSON.
Kekkai is a small open-source CLI that wraps existing security scanners (Trivy, Semgrep, Gitleaks) and focuses on the part that tends to be slow and frustrating: reviewing and triaging results.
Running scanners is easy. Interpreting noisy output, dealing with false positives, and making CI usable is not. Kekkai exists to make that part tolerable..
What it does
- Runs Trivy (dependencies), Semgrep (code), and Gitleaks (secrets)
- Normalizes their outputs into a single report format
- Provides an interactive terminal UI for reviewing findings
- Lets you mark findings as false positives and persist decisions locally
- Supports CI mode with severity-based failure thresholds
Kekkai does not replace scanners or introduce proprietary detection logic. It sits on top of existing tools and focuses on workflow and UX.
Quick Start
Requires Docker and Python 3.12
1. Install
pipx install kekkai-cli
2. Scan
kekkai scan
# Runs Trivy (CVEs), Semgrep (code), Gitleaks (secrets)
# Outputs unified kekkai-report.json
3. Triage
kekkai triage
# Interactive TUI to review findings with keyboard navigation
⚡️ Auto-Install (Pre-commit)
Add this to your .pre-commit-config.yaml to scan on every commit:
- repo: [https://github.com/kademoslabs/kekkai](https://github.com/kademoslabs/kekkai)
rev: v2.0.1
hooks:
- id: kekkai-scan
No signup, no cloud service required.
Why Kekkai?
| Problem | Kekkai Solution |
|---|---|
| Juggling 3+ tools | One CLI for Trivy, Semgrep, Gitleaks |
| Reading JSON logs | Interactive terminal UI |
| Installing scanners | Auto-pulls Docker containers |
| Parsing different formats | Unified kekkai-report.json |
| False positives | Mark and ignore with .kekkaiignore |
| CI/CD integration | kekkai scan --ci --fail-on high |
Features
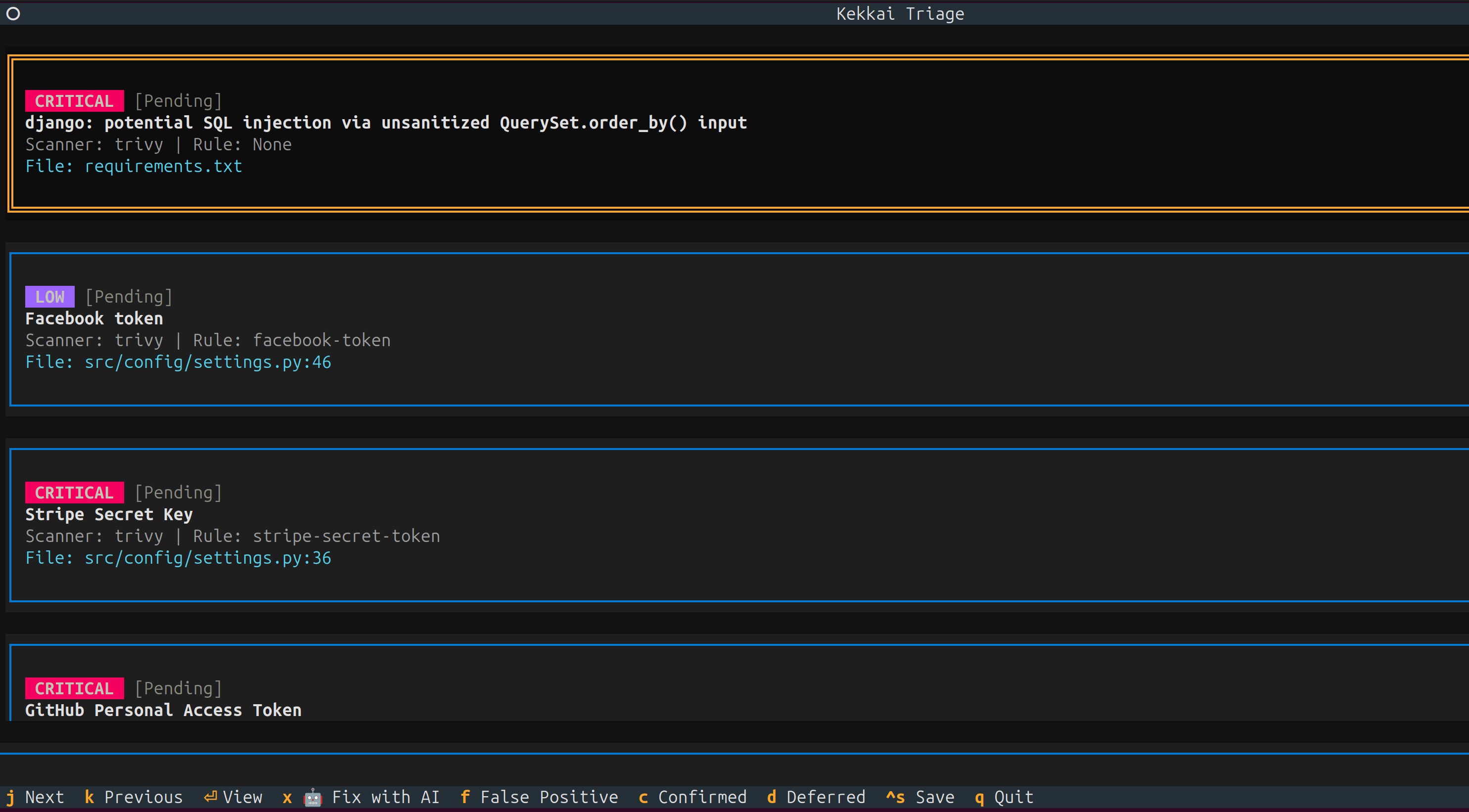
Interactive Triage TUI
Stop reading JSON. Use keyboard navigation to review findings, mark false positives, and generate ignore files.
kekkai triage
Controls:
j/kor↑/↓: Navigate findingsf: Mark as false positivec: Confirm findingd: Defer/ignoreCtrl+S: Save decisionsq: Quit
🚦 CI/CD in 1 Second
Don't write YAML. Run this in your repo:
kekkai init --ci
GitHub PR Comments
Get security feedback directly in pull requests.
export GITHUB_TOKEN="ghp_..."
kekkai scan --pr-comment
Unified Scanning
Run industry-standard scanners without installing them individually. Each scanner runs in an isolated Docker container.
kekkai scan # Scan current directory
kekkai scan --repo /path/to/project # Scan specific path
kekkai scan --output results.json # Custom output path
Scanners Included:
| Scanner | Finds | Image |
|---|---|---|
| Trivy | CVEs in dependencies | aquasec/trivy:latest |
| Semgrep | Code vulnerabilities | semgrep/semgrep:latest |
| Gitleaks | Hardcoded secrets | zricethezav/gitleaks:latest |
Container Security:
- Read-only filesystem
- No network access
- Memory limited (2GB)
- No privilege escalation
Design choices
- Local-first: no SaaS required, runs entirely on your machine or CI
- No network access for scanner containers
- Read-only filesystems, memory-limited containers
- Uses existing tools instead of reimplementing scanners
- Terminal-first UX instead of dashboards
Optional features
These are opt-in and not required for basic use:
Local-First AI Threat Modeling
Generate STRIDE threat models with AI that runs on your machine. No API keys. No cloud.
# Ollama (recommended - easy setup, privacy-preserving)
ollama pull mistral
kekkai threatflow --repo . --model-mode ollama --model-name mistral
# Output: THREATS.md with attack surface analysis and Mermaid.js diagrams
Supports:
- Ollama (recommended)
- Local GGUF models (llama.cpp)
- OpenAI/Anthropic (if you trust them with your code)
Full Local-First AI Threat Modeling Documentation →
DefectDojo Integration
Spin up a vulnerability management dashboard locally if you need it.
kekkai dojo up --wait # Start DefectDojo
kekkai upload # Import scan results
What You Get:
- DefectDojo web UI at
http://localhost:8080 - Automatic credential generation
- Pre-configured for Kekkai imports
AI-Powered Fix Engine
Generate code patches for findings (experimental).
kekkai fix --input scan-results.json --apply
Compliance Reporting
Map findings to PCI-DSS, OWASP, HIPAA, SOC 2.
kekkai report --input scan-results.json --format pdf --frameworks PCI-DSS,OWASP
What this is not
- Not a replacement for commercial AppSec platforms
- Not a new scanner or detection engine
- Not optimized for large enterprises (yet)
- Not a hosted service
Right now, Kekkai is aimed at individual developers and small teams who already run scanners but want better triage and less noise.
Security
Kekkai is designed with security as a core principle:
- Container Isolation: Scanners run in hardened Docker containers
- No Network Access: Containers cannot reach external networks
- Local-First AI: run entirely on your machine
- SLSA Level 3: Release artifacts include provenance attestations
- Signed Images: Docker images are Cosign-signed
For vulnerability reports, see SECURITY.md.
Documentation
| Guide | Description |
|---|---|
| Installation | All installation methods |
| ThreatFlow | AI threat modeling setup |
| Triage TUI | Interactive finding review |
| CI Mode | Pipeline integration |
| DefectDojo | Optional vulnerability management |
| Security | SLSA provenance verification |
Roadmap (short-term)
- Persistent triage state across runs (baselines)
- “New findings only” diffs
- Better PR-level workflows
- Cleaner reporting for small teams
Contributing
We welcome contributions! See CONTRIBUTING.md for guidelines.
License
Apache-2.0 — See LICENSE for details.
Built by Kademos Labs
Project details
Release history Release notifications | RSS feed
Download files
Download the file for your platform. If you're not sure which to choose, learn more about installing packages.
Source Distribution
Built Distribution
Filter files by name, interpreter, ABI, and platform.
If you're not sure about the file name format, learn more about wheel file names.
Copy a direct link to the current filters
File details
Details for the file kekkai_cli-2.2.1.tar.gz.
File metadata
- Download URL: kekkai_cli-2.2.1.tar.gz
- Upload date:
- Size: 218.1 kB
- Tags: Source
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/6.2.0 CPython/3.12.12
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
bd4cb4aff2483ec56c433f2e2e91d928ecf7afd4011039619dcb89788b256d89
|
|
| MD5 |
3ac18ed411fbe82c7b9b7aad0db8b6bf
|
|
| BLAKE2b-256 |
a54554ee05bb2095927552a0f3488f4e68b3e771145e1cd7bb670a78caf4b026
|
File details
Details for the file kekkai_cli-2.2.1-py3-none-any.whl.
File metadata
- Download URL: kekkai_cli-2.2.1-py3-none-any.whl
- Upload date:
- Size: 197.5 kB
- Tags: Python 3
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/6.2.0 CPython/3.12.12
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
96dcec4f4ca96626f7faf1a720342ebac261c128e5c814c5266d6d1c65a76164
|
|
| MD5 |
ef7955bc819c65462c1785738a2e0111
|
|
| BLAKE2b-256 |
74c09fd436eaa64a92f1eacccf4c4e3bee83674d006a7321976e8584b9dd10e8
|