Snaffler Impacket port - find credentials and sensitive data on SMB shares
Project description
snaffler-ng
Impacket port of Snaffler.
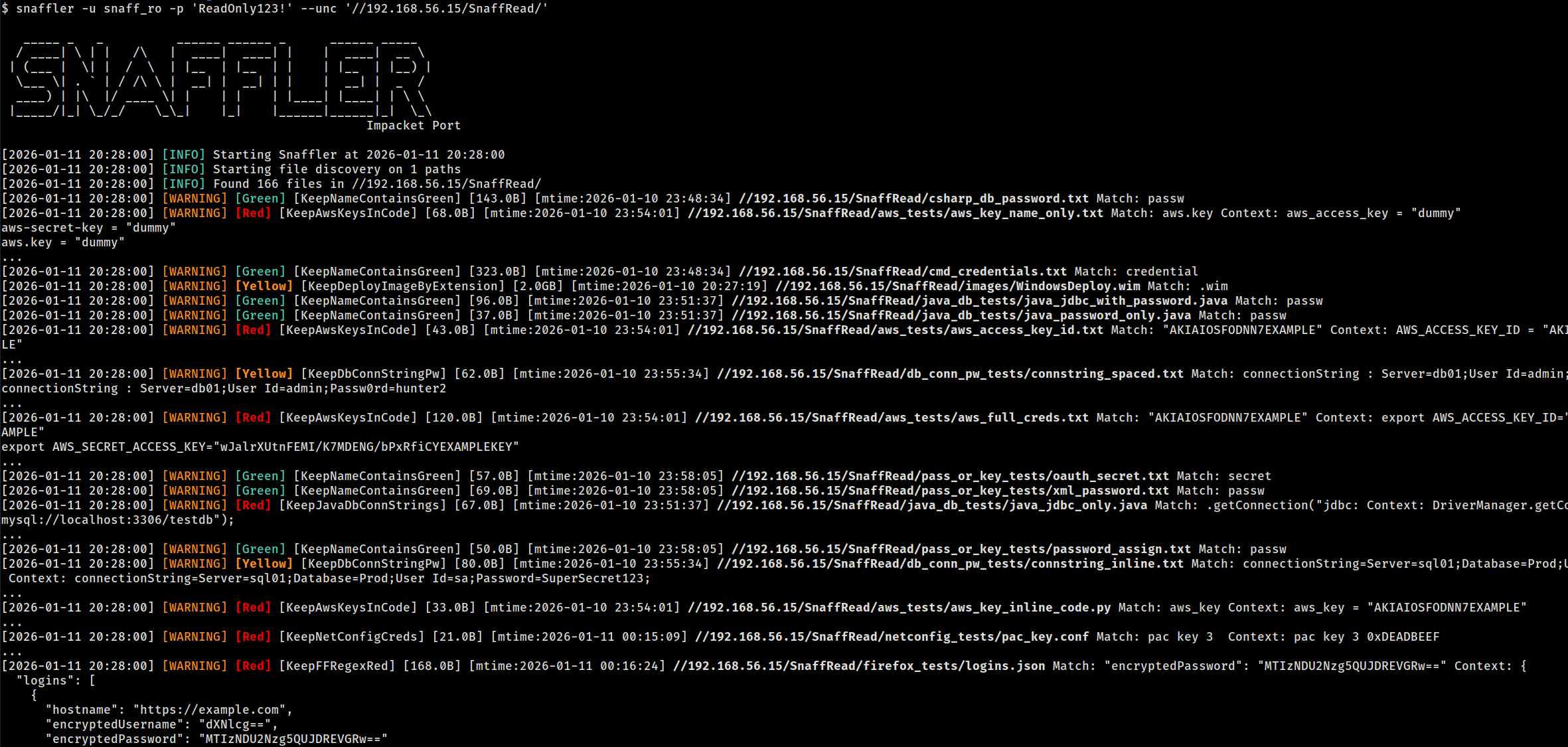
snaffler-ng is a post-exploitation / red teaming tool designed to discover readable SMB shares, walk directory trees, and identify credentials and sensitive data on Windows systems.
Features
- SMB share discovery via SRVSVC (NetShareEnum)
- DFS namespace discovery via LDAP (v1 + v2), merged and deduplicated with share enumeration
- Parallel directory tree walking with intra-share fan-out
- 103 built-in regex-based file and content classification rules
- NTLM authentication (password or pass-the-hash)
- Kerberos authentication (with ccache support)
- Multithreaded scanning (DNS / share / tree / file stages) with automatic thread rebalancing
- DNS pre-resolution with TCP port 445 probe to filter stale AD objects
- Optional file download ("snaffling")
- Resume support via SQLite state database (auto-resume on existing DB)
- Share and path filtering by glob pattern (
--share,--exclude-share,--exclude-unc) - Compatible with original and custom TOML rule sets
- Deterministic, ingestion-friendly logging (plain / JSON / TSV)
- Custom DNS resolution (
--nameserver) for internal AD hostname resolution through SOCKS tunnels - SOCKS proxy pivoting (
--socks) - OPSEC mode (
--stealth) — pads LDAP queries to break IDS signatures - Live web dashboard (
--web) for real-time scan monitoring snaffler resultssubcommand to query findings from a scan database (plain / JSON / HTML)- Runtime hotkeys: press
dfor DEBUG,ifor INFO during a scan - Pipe-friendly: accepts NetExec (nxc)
--sharesoutput via--stdin
Installation
pip / pipx
pip install snaffler-ng
# or
pipx install snaffler-ng
Optional extras:
pip install snaffler-ng[socks] # SOCKS proxy support
pip install snaffler-ng[web] # Live web dashboard
# pipx: use --pip-args
pipx install snaffler-ng --pip-args="[socks,web]"
Standalone Binary
Pre-built single-file executables (no Python required) are attached to each GitHub Release:
| Platform | File |
|---|---|
| Linux x86_64 | snaffler-linux-x86_64 |
| Windows x86_64 | snaffler-windows-x86_64.exe |
Kali / Debian
sudo dpkg -i snaffler-ng_*.deb
Quick Start
Full Domain Discovery
Providing only a domain triggers full domain discovery:
snaffler \
-u USERNAME \
-p PASSWORD \
-d DOMAIN.LOCAL
This will automatically:
- Query Active Directory for computer objects
- Discover DFS namespace targets via LDAP (v1
fTDfs+ v2msDFS-Linkv2) - Resolve hostnames and probe port 445 reachability
- Enumerate SMB shares on discovered hosts
- Merge and deduplicate DFS and SMB share paths
- Scan all readable shares
When using Kerberos, set KRB5CCNAME to a valid ticket cache and use hostnames/FQDNs:
snaffler \
-k \
--use-kcache \
-d DOMAIN.LOCAL \
--dc-host CORP-DC02
Targeted Scans
Scan a specific UNC path (no discovery):
snaffler \
-u USERNAME \
-p PASSWORD \
--unc //192.168.1.10/Share
Scan multiple computers (share discovery enabled):
snaffler \
-u USERNAME \
-p PASSWORD \
--computer 192.168.1.10 \
--computer 192.168.1.11
Load target computers from file:
snaffler \
-u USERNAME \
-p PASSWORD \
--computer-file targets.txt
Filtering Shares and Directories
Only scan specific shares:
snaffler -u USER -p PASS -d DOMAIN.LOCAL --share "SYSVOL" --share "IT*"
Exclude shares and paths by glob:
snaffler -u USER -p PASS -d DOMAIN.LOCAL \
--exclude-share "IPC$" --exclude-share "print$" \
--exclude-unc "*/Windows/*" --exclude-unc "*/.snapshot/*"
Pipe from NetExec (nxc)
Pipe nxc smb --shares output directly into snaffler-ng with --stdin:
nxc smb 10.8.50.20 -u user -p pass --shares | snaffler -u user -p pass --stdin
This parses NXC's share output, extracts UNC paths, and feeds them into the file scanner. Snaffler's existing share/directory rules handle filtering.
Custom DNS Server
Use --nameserver (or --ns) to resolve hostnames through a specific DNS server instead of the system resolver. Useful for lab environments, split DNS, or any setup where the system resolver can't reach the target domain:
# Point at the DC for name resolution
snaffler -u USER -p PASS -d DOMAIN.LOCAL --dc-host 192.168.201.11 --ns 192.168.201.11
# Combine with SOCKS — DNS queries use TCP and route through the tunnel automatically
snaffler -u USER -p PASS -d DOMAIN.LOCAL --dc-host 192.168.201.11 \
--socks socks5://127.0.0.1:1080 --ns 192.168.201.11
Web Dashboard
Launch a live web dashboard to monitor scan progress and findings in a browser:
snaffler -u USER -p PASS -d DOMAIN.LOCAL --web --web-port 8080
Requires the web extra (pip install snaffler-ng[web]).
Logging & Output Formats
snaffler-ng supports three output formats, each with a distinct purpose:
Plain(default, human-readable)JSON(structured, SIEM-friendly)TSV(flat, ingestion-friendly)
When using -o/--output, the format is auto-detected from the file extension (.json → JSON, .tsv → TSV). Use --log-type to override.
Resume Support
Large environments are expected. Scan state is tracked in a SQLite database (snaffler.db by default).
Scans auto-resume when the state database exists:
# First run — creates snaffler.db
snaffler -u USER -p PASS --computer-file targets.txt
# Interrupted? Just re-run the same command — it picks up where it left off
snaffler -u USER -p PASS --computer-file targets.txt
Use --state to specify a custom database path, or --fresh to ignore existing state and start clean:
snaffler -u USER -p PASS -d DOMAIN.LOCAL --state /tmp/scan1.db
snaffler -u USER -p PASS -d DOMAIN.LOCAL --fresh
Querying Results
After a scan, use snaffler results to query findings from the state database:
snaffler results # plain text summary
snaffler results -f json # JSON output
snaffler results -f html > report.html # HTML report with search bar
snaffler results -b 2 # Red+ severity only
snaffler results -s /path/to/snaffler.db # custom DB path
Authentication Options
- NTLM username/password
- NTLM pass-the-hash (
--hash) - Kerberos (
-k) - Kerberos via existing ccache (
--use-kcache) - SOCKS proxy pivoting (
--socks) - Custom DNS server (
--nameserver/--ns)
Project details
Release history Release notifications | RSS feed
Download files
Download the file for your platform. If you're not sure which to choose, learn more about installing packages.
Source Distribution
Built Distribution
Filter files by name, interpreter, ABI, and platform.
If you're not sure about the file name format, learn more about wheel file names.
Copy a direct link to the current filters
File details
Details for the file snaffler_ng-1.2.1.tar.gz.
File metadata
- Download URL: snaffler_ng-1.2.1.tar.gz
- Upload date:
- Size: 136.0 kB
- Tags: Source
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/6.1.0 CPython/3.13.7
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
2c59f3e3e417e075aed263d38892fae0e42017a826a083c69c9fda1f1f0eb706
|
|
| MD5 |
faf3037ff358f5ad01f3d16c7b400ad3
|
|
| BLAKE2b-256 |
13e8c5c14029c40ff7247b0ebd57af5c9275b61fd6459c1e07bdc70dcaf65286
|
File details
Details for the file snaffler_ng-1.2.1-py3-none-any.whl.
File metadata
- Download URL: snaffler_ng-1.2.1-py3-none-any.whl
- Upload date:
- Size: 178.2 kB
- Tags: Python 3
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/6.1.0 CPython/3.13.7
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 |
404591512ce2423c2e9ee1e5e378c8d0b77d16bdab1b7b90ee2b1104563bbe09
|
|
| MD5 |
820f60ec033a1e378c7b371179797dba
|
|
| BLAKE2b-256 |
ef93f444cc24360160375e87a61f2895d24c82a5ea4da79db04dc8a262f54090
|